2026 New CEH-001 Exam Dumps with PDF and VCE Free: https://www.2passeasy.com/dumps/CEH-001/
Our pass rate is high to 98.9% and the similarity percentage between our CEH-001 study guide and real exam is 90% based on our seven-year educating experience. Do you want achievements in the GAQM CEH-001 exam in just one try? I am currently studying for the GAQM CEH-001 exam. Latest GAQM CEH-001 Test exam practice questions and answers, Try GAQM CEH-001 Brain Dumps First.
Check CEH-001 free dumps before getting the full version:
NEW QUESTION 1
Bart is looking for a Windows NT/2000/XP command-line tool that can be used to assign, display, or modify ACL’s (access control lists) to files or folders and also one that can be used within batch files.
Which of the following tools can be used for that purpose? (Choose the best answer)
- A. PERM.exe
- B. CACLS.exe
- C. CLACS.exe
- D. NTPERM.exe
Answer: B
Explanation:
Cacls.exe is a Windows NT/2000/XP command-line tool you can use to assign, display, or modify ACLs (access control lists) to files or folders. Cacls is an interactive tool, and since it's a command-line utility, you can also use it in batch files.
NEW QUESTION 2
Buffer X in an Accounting application module for Brownies Inc. can contain 200 characters. The programmer makes an assumption that 200 characters are more than enough. Because there were no proper boundary checks being conducted, Bob decided to insert 400 characters into the 200-character buffer. (Overflows the buffer). Below is the code snippet: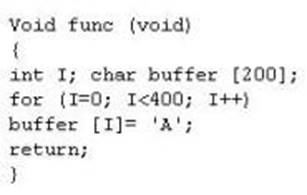
How can you protect/fix the problem of your application as shown above?
- A. Because the counter starts with 0, we would stop when the counter is less than 200
- B. Because the counter starts with 0, we would stop when the counter is more than 200
- C. Add a separate statement to signify that if we have written less than 200 characters to the buffer, the stack should stop because it cannot hold any more data
- D. Add a separate statement to signify that if we have written 200 characters to the buffer, the stack should stop because it cannot hold any more data
Answer: AD
NEW QUESTION 3
Cyber Criminals have long employed the tactic of masking their true identity. In IP spoofing, an attacker gains unauthorized access to a computer or a network by making it appear that a malicious message has come from a trusted machine, by "spoofing" the IP address of that machine.
How would you detect IP spoofing?
- A. Check the IPID of the spoofed packet and compare it with TLC checksu
- B. If the numbers match then it is spoofed packet
- C. Probe a SYN Scan on the claimed host and look for a response SYN/FIN packet, if the connection completes then it is a spoofed packet
- D. Turn on 'Enable Spoofed IP Detection' in Wireshark, you will see a flag tick if the packet is spoofed
- E. Sending a packet to the claimed host will result in a repl
- F. If the TTL in the reply is not the same as the packet being checked then it is a spoofed packet
Answer: D
NEW QUESTION 4
A company has hired a security administrator to maintain and administer Linux and Windows-based systems. Written in the nightly report file is the followinG.
Firewall log files are at the expected value of 4 MB. The current time is 12am. Exactly two hours later the size has decreased considerably. Another hour goes by and the log files have shrunk in size again.
Which of the following actions should the security administrator take?
- A. Log the event as suspicious activity and report this behavior to the incident response team immediately.
- B. Log the event as suspicious activity, call a manager, and report this as soon as possible.
- C. Run an anti-virus scan because it is likely the system is infected by malware.
- D. Log the event as suspicious activity, continue to investigate, and act according to the site's security policy.
Answer: D
NEW QUESTION 5
An attacker has successfully compromised a remote computer. Which of the following comes as one of the last steps that should be taken to ensure that the compromise cannot be traced back to the source of the problem?
- A. Install patches
- B. Setup a backdoor
- C. Install a zombie for DDOS
- D. Cover your tracks
Answer: D
NEW QUESTION 6
You are attempting to crack LM Manager hashed from Windows 2000 SAM file. You will be using LM Brute force hacking tool for decryption.
What encryption algorithm will you be decrypting?
- A. MD4
- B. DES
- C. SHA
- D. SSL
Answer: B
Explanation:
The LM hash is computed as follows.
1. The user’s password as an OEM string is converted to uppercase.
2. This password is either null-padded or truncated to 14 bytes.
3. The “fixed-length” password is split into two 7-byte halves.
1. 4. These values are used to create two DES keys, one from each 7-byte half.
5. Each of these keys is used to DES-encrypt the constant ASCII string “KGS!@#$%”, resulting in two 8-byte ciphertext values.
6. These two ciphertext values are concatenated to form a 16-byte value, which is the LM hash.
NEW QUESTION 7
Blane is a network security analyst for his company. From an outside IP, Blane performs an XMAS scan using Nmap. Almost every port scanned does not illicit a response. What can he infer from this kind of response?
- A. These ports are open because they do not illicit a response.
- B. He can tell that these ports are in stealth mode.
- C. If a port does not respond to an XMAS scan using NMAP, that port is closed.
- D. The scan was not performed correctly using NMAP since all ports, no matter what their state, will illicit some sort of response from an XMAS scan.
Answer: A
NEW QUESTION 8
TCP packets transmitted in either direction after the initial three-way handshake will have which of the following bit set?
- A. SYN flag
- B. ACK flag
- C. FIN flag
- D. XMAS flag
Answer: B
NEW QUESTION 9
John is using a special tool on his Linux platform that has a signature database and is therefore able to detect hundred of vulnerabilities in UNIX, Windows, and commonly-used web CGI scripts. Additionally, the database detects DDoS zombies and Trojans. What would be the name of this multifunctional tool?
- A. nmap
- B. hping
- C. nessus
- D. make
Answer: C
Explanation:
Nessus is the world's most popular vulnerability scanner, estimated to be used by over 75, 000 organizations world-wide. Nmap is mostly used for scanning, not for detecting vulnerabilities. Hping is a free packet generator and analyzer for the TCP/IP protocol and make is used to automatically build large applications on the *nix plattform.
NEW QUESTION 10
What does the following command in netcat do? nc -l -u -p55555 < /etc/passwd
- A. logs the incoming connections to /etc/passwd file
- B. loads the /etc/passwd file to the UDP port 55555
- C. grabs the /etc/passwd file when connected to UDP port 55555
- D. deletes the /etc/passwd file when connected to the UDP port 55555
Answer: C
Explanation:
-l forces netcat to listen for incoming connections.
-u tells netcat to use UDP instead of TCP
-p 5555 tells netcat to use port 5555
< /etc/passwd tells netcat to grab the /etc/passwd file when connected to.
NEW QUESTION 11
Frederickson Security Consultants is currently conducting a security audit on the networks of Hawthorn Enterprises, a contractor for the Department of Defense. Since Hawthorn Enterprises conducts business daily with the federal government, they must abide by very stringent security policies. Frederickson is testing all of Hawthorn's physical and logical security measures including biometrics, passwords, and permissions. The federal government requires that all users must utilize random, non-dictionary passwords that must take at least 30 days to crack. Frederickson has confirmed that all Hawthorn employees use a random password generator for their network passwords. The Frederickson consultants have saved off numerous SAM files from Hawthorn's servers using Pwdump6 and are going to try and crack the network passwords. What method of attack is best suited to crack these passwords in the shortest amount of time?
- A. Brute force attack
- B. Birthday attack
- C. Dictionary attack
- D. Brute service attack
Answer: A
NEW QUESTION 12
Which of the following statements best describes the term Vulnerability?
- A. A weakness or error that can lead to a compromise
- B. An agent that has the potential to take advantage of a weakness
- C. An action or event that might prejudice security
- D. The loss potential of a threat.
Answer: A
Explanation:
Vulnerabilities are all weaknesses that can be exploited.
NEW QUESTION 13
International Organization for Standardization (ISO) standard 27002 provides guidance for compliance by outlining
- A. guidelines and practices for security controls.
- B. financial soundness and business viability metrics.
- C. standard best practice for configuration management.
- D. contract agreement writing standards.
Answer: A
NEW QUESTION 14
While probing an organization you discover that they have a wireless network. From your attempts to connect to the WLAN you determine that they have deployed MAC filtering by using ACL on the access points. What would be the easiest way to circumvent and communicate on the WLAN?
- A. Attempt to crack the WEP key using Airsnort.
- B. Attempt to brute force the access point and update or delete the MAC ACL.
- C. Steel a client computer and use it to access the wireless network.
- D. Sniff traffic if the WLAN and spoof your MAC address to one that you captured.
Answer: D
Explanation:
The easiest way to gain access to the WLAN would be to spoof your MAC address to one that already exists on the network.
NEW QUESTION 15
Data is sent over the network as clear text (unencrypted) when Basic Authentication is configured on Web Servers.
- A. true
- B. false
Answer: A
NEW QUESTION 16
What two things will happen if a router receives an ICMP packet, which has a TTL value of 1, and the destination host is several hops away? (Select 2 answers)
- A. The router will discard the packet
- B. The router will decrement the TTL value and forward the packet to the next router on the path to the destination host
- C. The router will send a time exceeded message to the source host
- D. The router will increment the TTL value and forward the packet to the next router on the path to the destination host.
- E. The router will send an ICMP Redirect Message to the source host
Answer: AC
NEW QUESTION 17
Jayden is a network administrator for her company. Jayden wants to prevent MAC spoofing on all the Cisco switches in the network. How can she accomplish this?
- A. Jayden can use the comman
- B. ip binding set.
- C. Jayden can use the comman
- D. no ip spoofing.
- E. She should use the comman
- F. no dhcp spoofing.
- G. She can use the comman
- H. ip dhcp snooping binding.
Answer: D
NEW QUESTION 18
Neil notices that a single address is generating traffic from its port 500 to port 500 of several other machines on the network. This scan is eating up most of the network bandwidth and Neil is concerned. As a security professional, what would you infer from this scan?
- A. It is a network fault and the originating machine is in a network loop
- B. It is a worm that is malfunctioning or hardcoded to scan on port 500
- C. The attacker is trying to detect machines on the network which have SSL enabled
- D. The attacker is trying to determine the type of VPN implementation and checking for IPSec
Answer: D
Explanation:
Port 500 is used by IKE (Internet Key Exchange). This is typically used for IPSEC-based VPN software, such as Freeswan, PGPnet, and various vendors of in-a-box VPN solutions such as Cisco. IKE is used to set up the session keys. The actual session is usually sent with ESP (Encapsulated Security Payload) packets, IP protocol 50 (but some in-a-box VPN's such as Cisco are capable of negotiating to send the encrypted tunnel over a UDP channel, which is useful for use across firewalls that block IP protocols other than TCP or UDP).
NEW QUESTION 19
To what does “message repudiation” refer to what concept in the realm of email security?
- A. Message repudiation means a user can validate which mail server or servers a message was passed through.
- B. Message repudiation means a user can claim damages for a mail message that damaged their reputation.
- C. Message repudiation means a recipient can be sure that a message was sent from a particular person.
- D. Message repudiation means a recipient can be sure that a message was sent from a certain host.
- E. Message repudiation means a sender can claim they did not actually send a particular message.
Answer: E
Explanation:
A quality that prevents a third party from being able to prove that a communication between two other parties ever took place. This is a desirable quality if you do not want your communications to be traceable.
Non-repudiation is the opposite quality—a third party can prove that a communication between two other parties took place. Non-repudiation is desirable if you want to be able to trace your communications and prove that they occurred. Repudiation – Denial of message submission or delivery.
NEW QUESTION 20
_____ will let you assume a users identity at a dynamically generated web page or site.
- A. SQL attack
- B. Injection attack
- C. Cross site scripting
- D. The shell attack
- E. Winzapper
Answer: C
Explanation:
Cross site scripting is also referred to as XSS or CSS. You must know the user is online and you must scam that user into clicking on a link that you have sent in order for this hack attack to work.
NEW QUESTION 21
What are the three phases involved in security testing?
- A. Reconnaissance, Conduct, Report
- B. Reconnaissance, Scanning, Conclusion
- C. Preparation, Conduct, Conclusion
- D. Preparation, Conduct, Billing
Answer: C
Explanation:
Preparation phase - A formal contract is executed containing non-disclosure of the client's data and legal protection for the tester. At a minimum, it also lists the IP addresses to be tested and time to test.
Conduct phase - In this phase the penetration test is executed, with the tester looking for potential vulnerabilities.
Conclusion phase - The results of the evaluation are communicated to the pre-defined organizational contact, and corrective action is advised.
NEW QUESTION 22
Which of the following types of firewall inspects only header information in network traffic?
- A. Packet filter
- B. Stateful inspection
- C. Circuit-level gateway
- D. Application-level gateway
Answer: A
NEW QUESTION 23
If a tester is attempting to ping a target that exists but receives no response or a response that states the destination is unreachable, ICMP may be disabled and the network may be using TCP. Which other option could the tester use to get a response from a host using TCP?
- A. Hping
- B. Traceroute
- C. TCP ping
- D. Broadcast ping
Answer: A
NEW QUESTION 24
An attacker finds a web page for a target organization that supplies contact information for the company. Using available details to make the message seem authentic, the attacker drafts e-mail to an employee on the contact page that appears to come from an individual who might reasonably request confidential information, such as a network administrator.
The email asks the employee to log into a bogus page that requests the employee's user name and password or click on a link that will download spyware or other malicious programming.
Google's Gmail was hacked using this technique and attackers stole source code and sensitive data from Google servers. This is highly sophisticated attack using zero-day exploit vectors, social engineering and malware websites that focused on targeted individuals working for the company.
What is this deadly attack called?
- A. Spear phishing attack
- B. Trojan server attack
- C. Javelin attack
- D. Social networking attack
Answer: A
NEW QUESTION 25
When working with Windows systems, what is the RID of the true administrator account?
- A. 500
- B. 501
- C. 1000
- D. 1001
- E. 1024
- F. 512
Answer: A
Explanation:
Because of the way in which Windows functions, the true administrator account always has a RID of 500.
NEW QUESTION 26
Ethereal works best on .
- A. Switched networks
- B. Linux platforms
- C. Networks using hubs
- D. Windows platforms
- E. LAN's
Answer: C
Explanation:
Ethereal is used for sniffing traffic. It will return the best results when used on an unswitched (i.e. hub. network.
NEW QUESTION 27
A newly discovered flaw in a software application would be considered which kind of security vulnerability?
- A. Input validation flaw
- B. HTTP header injection vulnerability
- C. 0-day vulnerability
- D. Time-to-check to time-to-use flaw
Answer: C
NEW QUESTION 28
......
P.S. Easily pass CEH-001 Exam with 878 Q&As Dumps-hub.com Dumps & pdf Version, Welcome to Download the Newest Dumps-hub.com CEH-001 Dumps: https://www.dumps-hub.com/CEH-001-dumps.html (878 New Questions)