2026 New CS0-001 Exam Dumps with PDF and VCE Free: https://www.2passeasy.com/dumps/CS0-001/
It is more faster and easier to pass the CompTIA CS0-001 exam by using High value CompTIA CompTIA CSA+ Certification Exam questuins and answers. Immediate access to the Abreast of the times CS0-001 Exam and find the same core area CS0-001 questions with professionally verified answers, then PASS your exam with a high score now.
CompTIA CS0-001 Free Dumps Questions Online, Read and Test Now.
NEW QUESTION 1
A SIEM analyst noticed a spike in activities from the guest wireless network to several electronic health record (EHR) systems. After further analysis, the analyst discovered that a large volume of data has been uploaded to a cloud provider in the last six months. Which of the following actions should the analyst do FIRST?
- A. Contact the Office of Civil Rights (OCR) to report the breach
- B. Notify the Chief Privacy Officer (CPO)
- C. Activate the incident response plan
- D. Put an ACL on the gateway router
Answer: D
NEW QUESTION 2
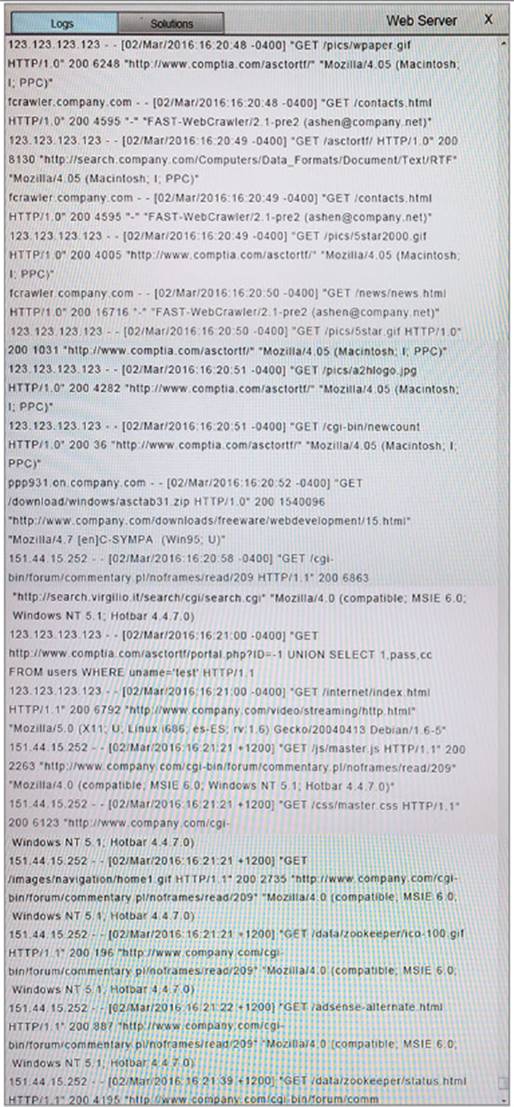
Given the following access log: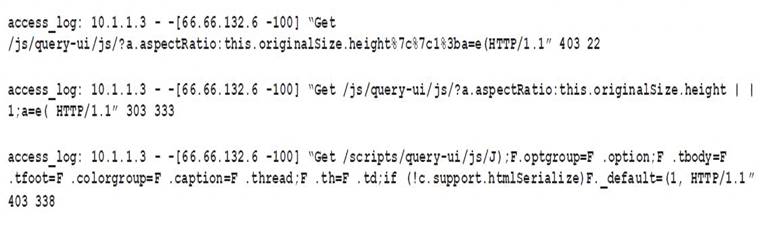
Which of the following accurately describes what this log displays?
- A. A vulnerability in jQuery
- B. Application integration with an externally hosted database
- C. A vulnerability scan performed from the Internet
- D. A vulnerability in Javascript
Answer: C
NEW QUESTION 3
A new zero day vulnerability was discovered within a basic screen capture app, which is used throughout the environment Two days after discovering the vulnerability, the manufacturer of the software has not announced a remediation or it there will be a fix for this newly discovered vulnerability. The vulnerable application is not uniquely critical, but it is used occasionally by the management and executive management teams The vulnerability allows remote code execution to gam privileged access to the system Which of the following is the BEST course of action to mitigate this threat'
- A. Work with the manufacturer to determine the tone frame for the fix.
- B. Block the vulnerable application traffic at the firewall and disable the application services on each computer.
- C. Remove the application and replace it with a similar non-vulnerable application.
- D. Communicate with the end users that the application should not be used until the manufacturer has reserved the vulnerability.
Answer: D
NEW QUESTION 4
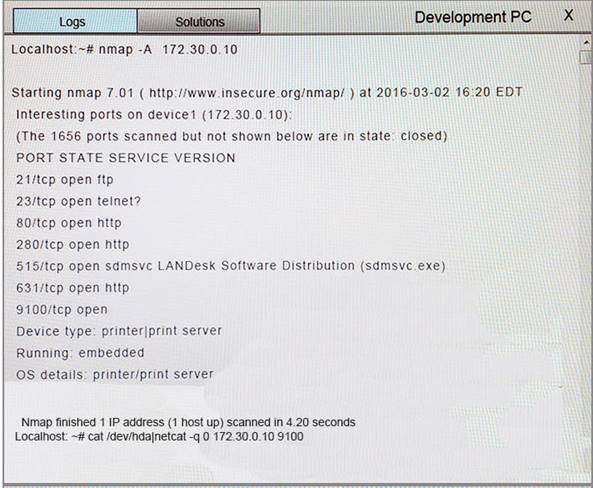
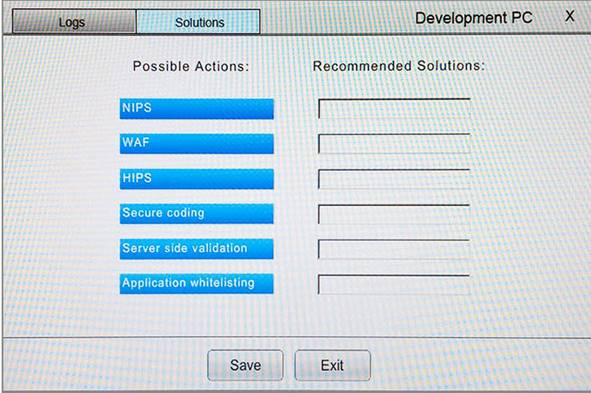
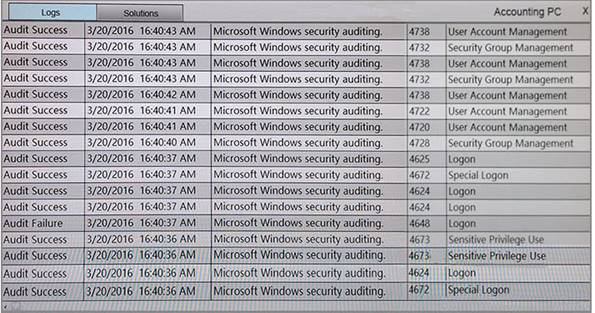
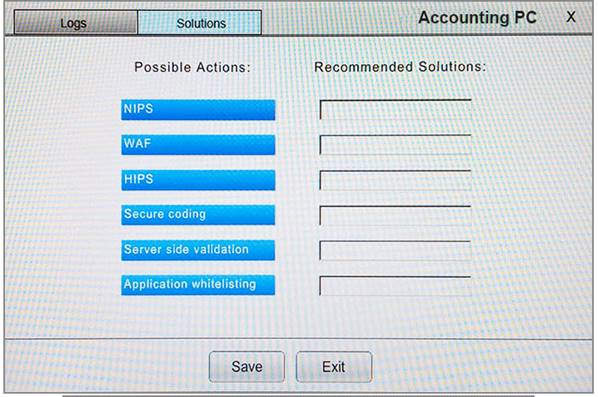
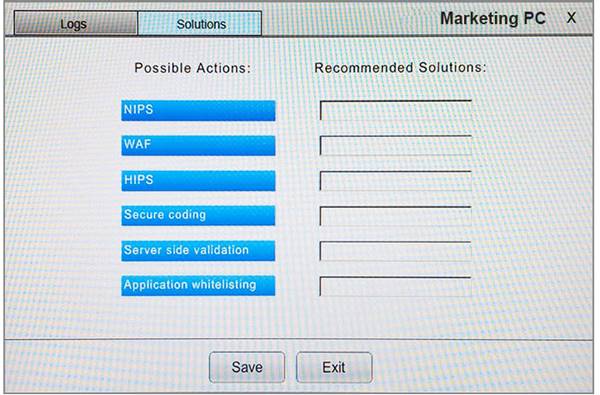
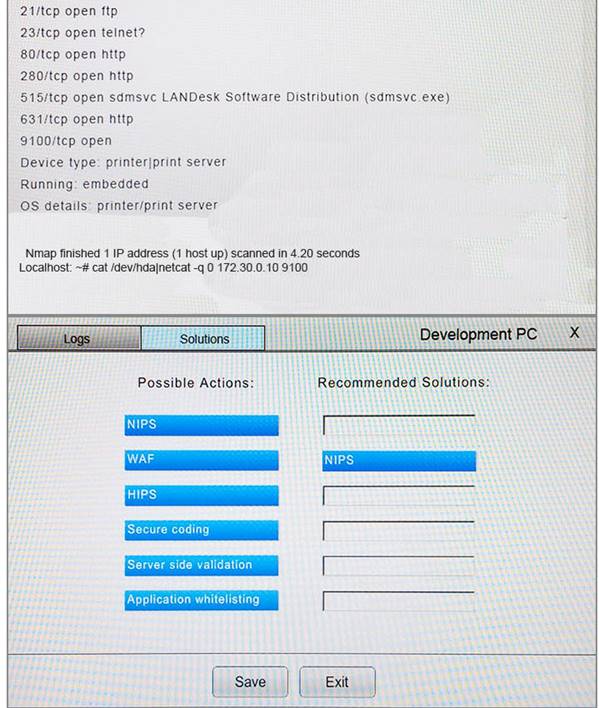
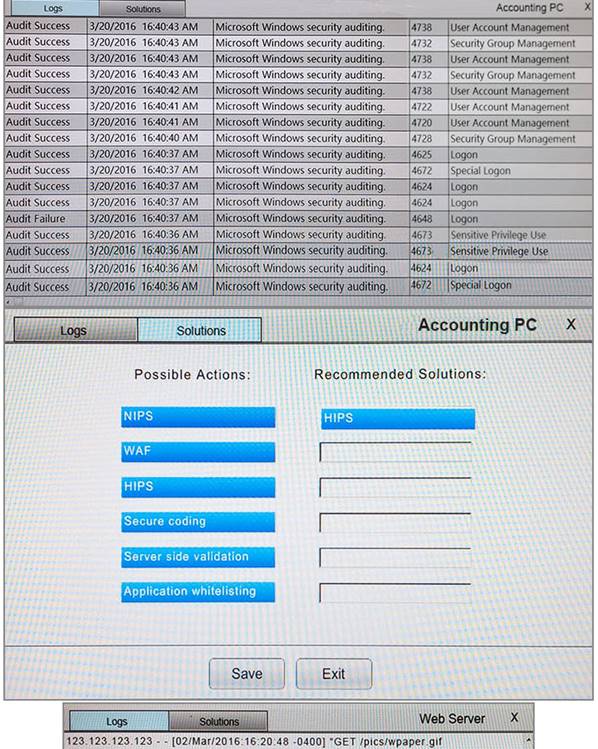
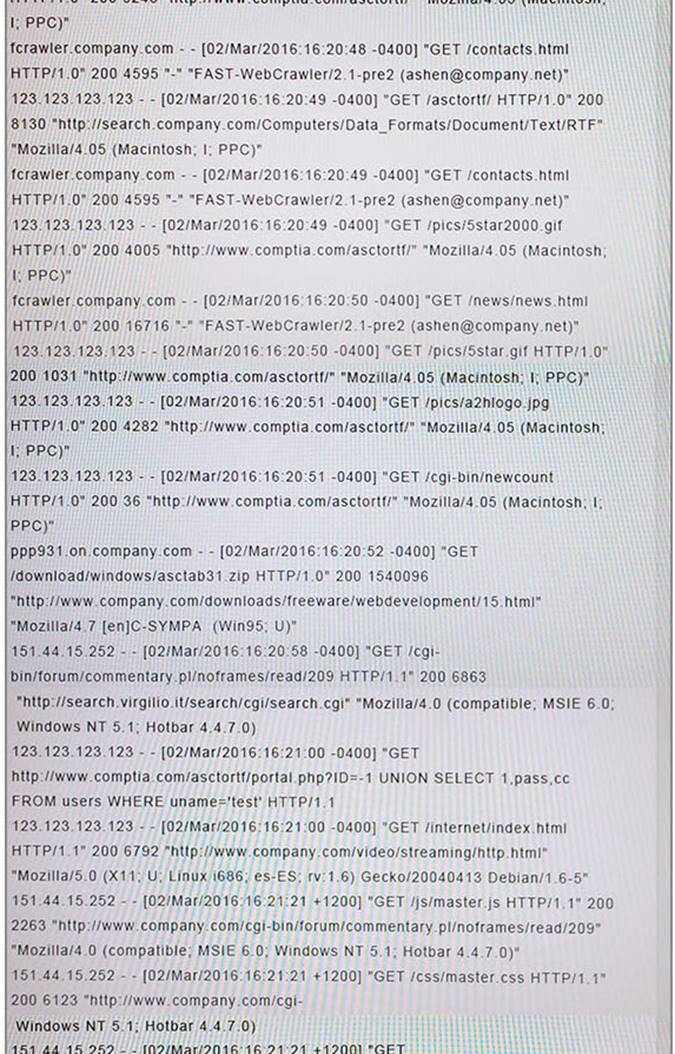
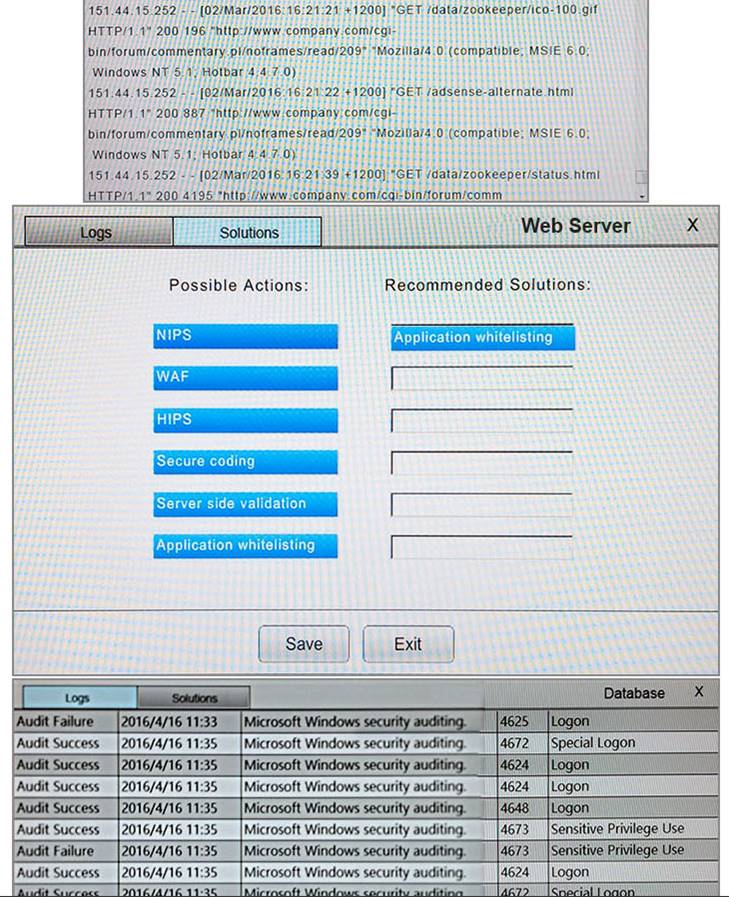
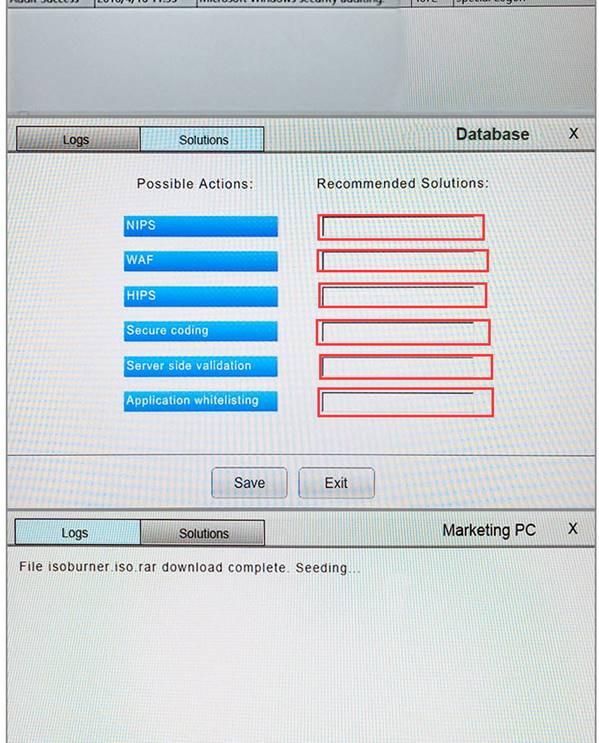
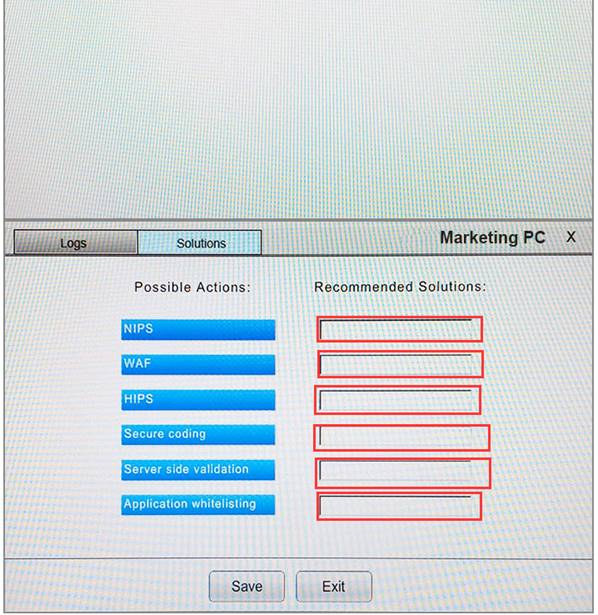
You suspect that multiple unrelated security events have occurred on several nodes on a corporate network. You must review all logs and correlate events when necessary to discover each security event by clicking on each node. Only select corrective actions if the logs shown a security event that needs remediation. Drag and drop the appropriate corrective actions to mitigate the specific security event occurring on each affected device.
Instructions:
The Web Server, Database Server, IDS, Development PC, Accounting PC and Marketing PC are clickable. Some actions may not be required and each actions can only be used once per node. The corrective action order is not important. If at any time you would like to bring back the initial state of the simulation, please select the Reset button. When you have completed the simulation, please select the Done button to submit. Once the simulation is submitted, please select the Next button to continue.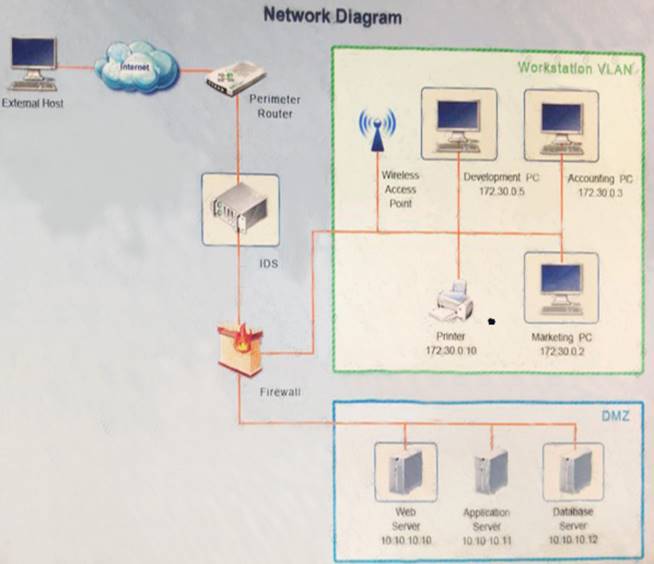
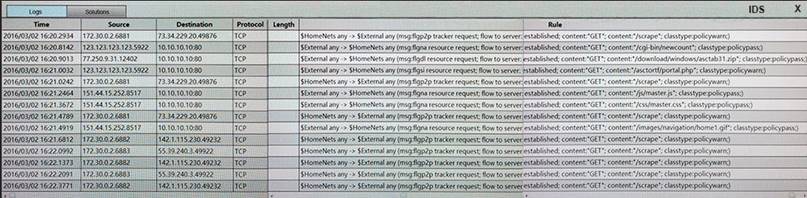
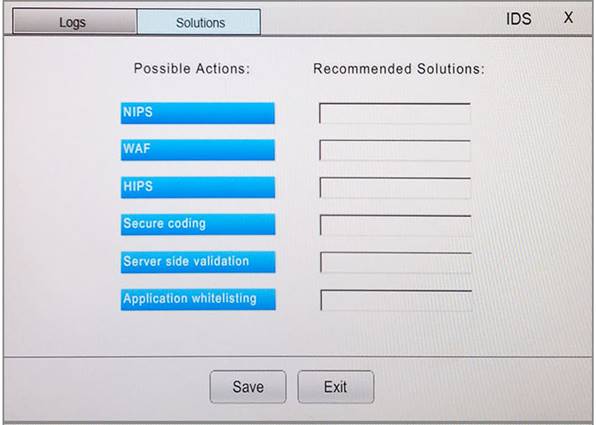
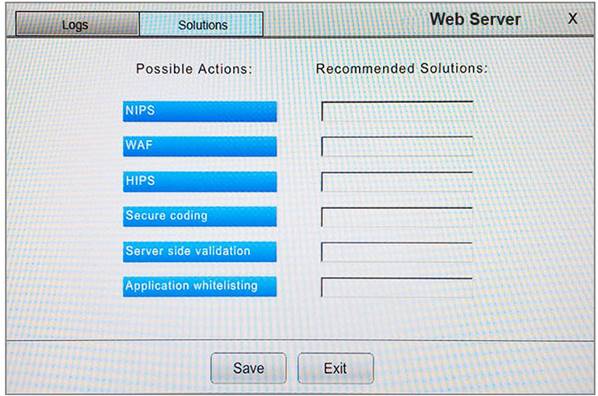
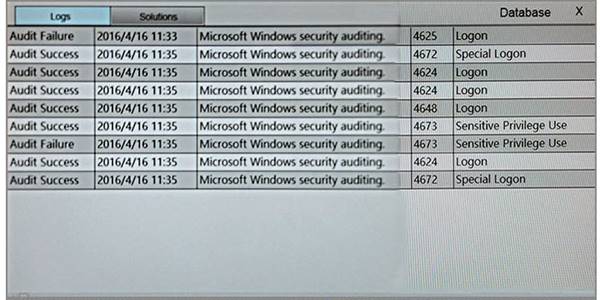
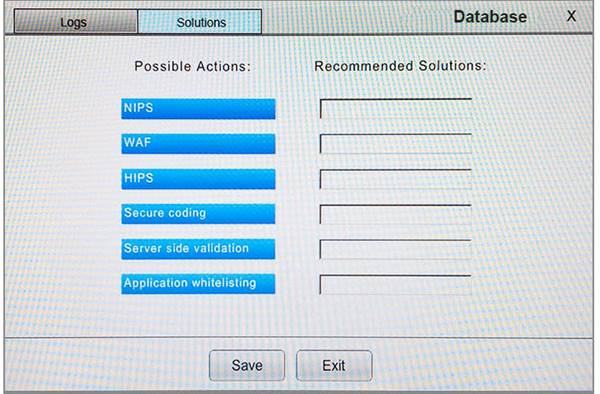
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 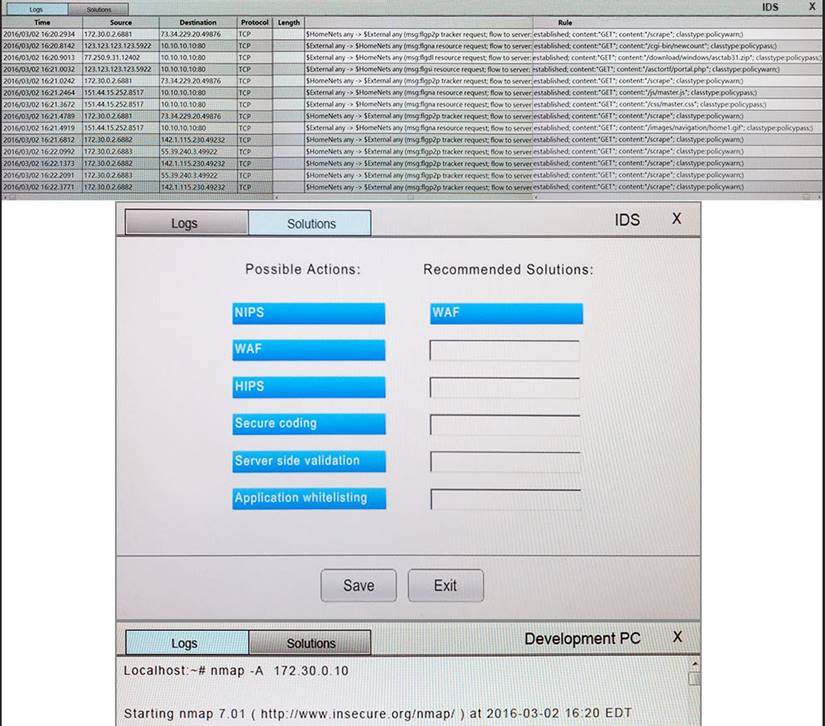
NEW QUESTION 5
A system administrator recently deployed and verified the installation of a critical patch issued by the company’s primary OS vendor. This patch was supposed to remedy a vulnerability that would allow an adversary to remotely execute code from over the network. However, the administrator just ran a vulnerability assessment of networked systems, and each of them still reported having the same vulnerability. Which of the following is the MOST likely explanation for this?
- A. The administrator entered the wrong IP range for the assessment.
- B. The administrator did not wait long enough after applying the patch to run the assessment.
- C. The patch did not remediate the vulnerability.
- D. The vulnerability assessment returned false positives.
Answer: C
NEW QUESTION 6
The development team recently moved a new application into production for the accounting department. After this occurred, the Chief Information Officer (CIO) was contacted by the head of accounting because the application is missing a key piece of functionality that is needed to complete the corporation’s quarterly tax returns. Which of the following types of testing would help prevent this from reoccurring?
- A. Security regression testing
- B. User acceptance testing
- C. Input validation testing
- D. Static code testing
Answer: B
NEW QUESTION 7
Which of the following stakeholders would need to be aware of an e-discovery notice received by the security office about an ongoing case within the manufacturing department?
- A. Board of trustees
- B. Human resources
- C. Legal
- D. Marketing
Answer: C
NEW QUESTION 8
Alerts have been received from the SIEM, indicating infections on multiple computers. Based on threat characteristic, these files were quarantined by the host-based antivirus program. At the same time, additional alerts in the SIEM show multiple blocked URLs from the address of the infected computers; the URLs were clashed as uncategorized. The domain location of the IP address of the URLs that were blocked is checked, and it is registered to an ISP in Russia. Which of the following steps should be taken NEXT?
- A. Remove those computers from the network and replace the hard drives Send the Infected hard drives out lot investigation.
- B. Run a full antivirus scan on all computers and use Splunk to search for any suspicious activity that happened just before the alerts were received in the SIEM.
- C. Run a vulnerability scan and patch discovered vulnerabilities on the next patching cycle Have the users restart their computer Create a use case in the SIEM to monitor farted logins oninfected computers.
- D. Install a computer with the same settings as the infected computers in the DM^ to use as a honeypot Permit the URLs classified as uncategorized to and from that host.
Answer: B
NEW QUESTION 9
A vulnerability scan has returned the following information: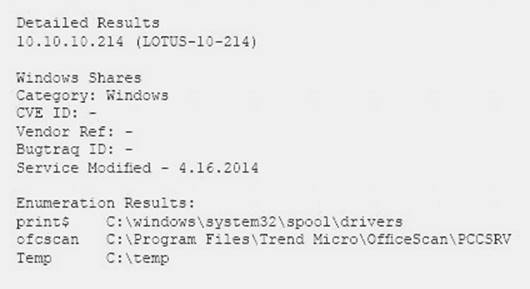
Which of the following describes the meaning of these results?
- A. There is an unknown bug in a Lotus server with no Bugtraq ID.
- B. Connecting to the host using a null session allows enumeration of share names.
- C. Trend Micro has a known exploit that must be resolved or patched.
- D. No CVE is present, so it is a false positive caused by Lotus running on a Windows server.
Answer: B
NEW QUESTION 10
Server contains baseline images that are deployed to sensitive workstations on a regular basis. The images are evaluated once per month for patching and other fixes, but do not change otherwise. Which of the following controls should be put in place to secure the file server and ensure the images are not changed?
- A. Install and configure a file integrity monitoring tool on the server and allow updates to the mages each month.
- B. Schedule vulnerability scans of the server at least once per month before the images are updated
- C. Require the use of two-factor authentication tor any administrator or user who needs to connect to the server.
- D. Install a honeypot to identify any attacks before the baseline images can be compromised
Answer: A
NEW QUESTION 11
A cybersecurity analyst has identified a new mission-essential function that utilizes a public cloud-based system. The analyst needs to classify the information processed by the system with respect to CIA. Which of the following should provide the CIA classification for the information?
- A. The cloud provider
- B. The data owner
- C. The cybersecurity analyst
- D. The system administrator
Answer: B
NEW QUESTION 12
A cybersecurity analyst is reviewing Apache logs on a web server and finds that some logs are missing. The analyst has identified that the systems administrator accidentally deleted some log files. Which of the following actions or rules should be implemented to prevent this incident from reoccurring?
- A. Personnel training
- B. Separation of duties
- C. Mandatory vacation
- D. Backup server
Answer: D
NEW QUESTION 13
A network administrator is attempting to troubleshoot an issue regarding certificates on a secure website. During the troubleshooting process, the network administrator notices that the web gateway proxy on the local network has signed all of the certificates on the local machine.
Which of the following describes the type of attack the proxy has been legitimately programmed to perform?
- A. Transitive access
- B. Spoofing
- C. Man-in-the-middle
- D. Replay
Answer: C
NEW QUESTION 14
A security analyst was asked to join an outage call to a critical web application. The web middleware support team determined (he wet) server w running and having no trouble processing requests, however, some investigation has revealed firewall denies to the web server that began around 1 00 a m that morning. An emergency change was made to enable the access, but management has asked tor a root cause determination. Which of the following would be the BEST next step?
- A. Install a packet analyze, near the web server to capture sample traffic to find anomalies.
- B. Block alt traffic lo the web server with an ACL.
- C. Use a port scan to determine all listening pons on the web server.
- D. Search the logging sewers for any rule changes.
Answer: D
NEW QUESTION 15
Weeks before a proposed merger is scheduled for completion, a security analyst has noticed unusual traffic patterns on a file server that contains financial information. Routine scans are not detecting the signature of any known exploits or malware. The following entry is seen in the ftp server logs:
tftp –I 10.1.1.1 GET fourthquarterreport.xls
Which of the following is the BEST course of action?
- A. Continue to monitor the situation using tools to scan for known exploits.
- B. Implement an ACL on the perimeter firewall to prevent data exfiltration.
- C. Follow the incident response procedure associate with the loss of business critical data.
- D. Determine if any credit card information is contained on the server containing the financials.
Answer: C
NEW QUESTION 16
After implementing and running an automated patching tool, a security administrator ran a vulnerability scan that reported no missing patches found. Which of the following BEST describes why this tool was used?
- A. To create a chain of evidence to demonstrate when the servers were patched.
- B. To harden the servers against new attacks.
- C. To provide validation that the remediation was active.
- D. To generate log data for unreleased patches.
Answer: B
NEW QUESTION 17
A software development company in the manufacturing sector has just completed the alpha version of its flagship application. The application has been under development for the past three years. The SOC has seen intrusion attempts made by indicators associated with a particular APT. The company has a hot site location for COOP. Which of the following threats would most likely incur the BIGGEST economic impact for the company?
- A. DDoS
- B. ICS destruction
- C. IP theft
- D. IPS evasion
Answer: A
NEW QUESTION 18
An analyst wants to use a command line tool to identify open ports and running services on a host along with the application that is associated with those services and port. Which of the following should the analyst use?
- A. Wireshark
- B. Qualys
- C. netstat
- D. nmap
- E. ping
Answer: D
NEW QUESTION 19
A threat intelligence analyst who works for a financial services firm received this report:
“There has been an effective waterhole campaign residing at www.bankfinancecompsoftware.com. This domain is delivering ransomware. This ransomware variant has been called “LockMaster” by researchers due to its ability to overwrite the MBR, but this term is not a malware signature. Please execute a defensive
operation regarding this attack vector.”
The analyst ran a query and has assessed that this traffic has been seen on the network. Which of the following actions should the analyst do NEXT? (Select TWO).
- A. Advise the firewall engineer to implement a block on the domain
- B. Visit the domain and begin a threat assessment
- C. Produce a threat intelligence message to be disseminated to the company
- D. Advise the security architects to enable full-disk encryption to protect the MBR
- E. Advise the security analysts to add an alert in the SIEM on the string “LockMaster”
- F. Format the MBR as a precaution
Answer: BD
NEW QUESTION 20
A company has decided to process credit card transactions directly. Which of the following would meet the requirements for scanning this type of data?
- A. Quarterly
- B. Yearly
- C. Bi-annually
- D. Monthly
Answer: A
NEW QUESTION 21
An organization wants to remediate vulnerabilities associated with its web servers. An initial vulnerability scan has been performed, and analysts are reviewing the results. Before starling any remediation the analysts want to remove false positives to avoid spending time on issues that are not actual vulnerabilities. Which of the following would be an indicator of a likely false positive?
- A. Reports indicate that findings are informational.
- B. Any item& labeled "low" are considered informational only.
- C. The scan result version is different front the automated asset inventory.
- D. HTTPS entries indicate the web page is encrypted securely.
Answer: A
NEW QUESTION 22
A company allows employees to work remotely. The security administration is configuring services that will allow remote help desk personnel to work secure outside the company’s headquarters. Which of the following presents the BEST solution to meet this goal?
- A. Configure a VPN concentrator to terminate in the DMZ to allow help desk personnel access to resources.
- B. Open port 3389 on the firewall to the server to allow users to connect remotely.
- C. Set up a jump box for all help desk personnel to remotely access system resources.
- D. Use the company’s existing web server for remote access and configure over port 8080.
Answer: A
NEW QUESTION 23
A computer al a company was used to commit a crime. The system was seized and removed for the further analysis. Which of the following »s the purpose of labeling cables and connections when seeing the computer system?
- A. To capture the system configuration as it was at the time it w3s removed
- B. To maintain the chain of custody
- C. To block any communication with the computer system from attack
- D. To document the model, manufacturer, and type of cables connected
Answer: A
NEW QUESTION 24
The board of directors made the decision to adopt a cloud-first strategy. The current security infrastructure was designed for on-premise implementation. A critical application that is subject to the Federal Information Security Management Act (FISMA) of 2002 compliance has been identified as a candidate for a hybrid cloud deployment model. Which of the following should be conducted FIRST?
- A. Develop a request for proposal.
- B. Perform a risk assessment.
- C. Review current security controls.
- D. Review the SLA for FISMA compliance.
Answer: C
NEW QUESTION 25
Which of the fallowing has the GREAT EST impact to the data retention policies of an organization?
- A. The CIA classification matrix assigned to each piece of data
- B. The level of sensitivity of the data established by the data owner
- C. The regulatory requirements concerning the data set
- D. The technical constraints of the technology used to store the data
Answer: D
NEW QUESTION 26
Which of the following is a control that allows a mobile application to access and manipulate information which should only be available by another application on the same mobile device (e.g. a music application posting the name of the current song playing on the device on a social media site)?
- A. Co-hosted application
- B. Transitive trust
- C. Mutually exclusive access
- D. Dual authentication
Answer: B
NEW QUESTION 27
A security analyst is reviewing output from a CVE-based vulnerability scanner. Before conducting the scan, the analyst was careful to select only Windows-based servers in a specific datacenter. The scan revealed that the datacenter includes 27 machines running Windows 2003 Server Edition (Win2003SE). In 2015, there were 36 new vulnerabilities discovered in the Win2003SE environment. Which of the following statements are MOST likely applicable? (Choose two.)
- A. Remediation is likely to require some form of compensating control.
- B. Microsoft’s published schedule for updates and patches for Win2003SE have continued uninterrupted.
- C. Third-party vendors have addressed all of the necessary updates and patches required by Win2003SE.
- D. The resulting report on the vulnerability scan should include some reference that the scan of the datacenter included 27 Win2003SE machines that should be scheduled for replacement and deactivation.
- E. Remediation of all Win2003SE machines requires changes to configuration settings and compensating controls to be made through Microsoft Security Center’s Win2003SE Advanced Configuration Toolkit.
Answer: D
NEW QUESTION 28
A security analyst is assisting with a computer crime investigator and has been asked to secure a PC and deliver it to the forensics lab. Which of the following items would be MOST helpful to secure the PC (Select THREE)
- A. Tamper-proof seals
- B. Fataday cage
- C. Chan of custody form
- D. Drive eraser
- E. Write blocks
- F. Network tap
- G. Millimeter
Answer: ABC
NEW QUESTION 29
......
P.S. Easily pass CS0-001 Exam with 363 Q&As DumpSolutions Dumps & pdf Version, Welcome to Download the Newest DumpSolutions CS0-001 Dumps: https://www.dumpsolutions.com/CS0-001-dumps/ (363 New Questions)