2026 New GCIA Exam Dumps with PDF and VCE Free: https://www.2passeasy.com/dumps/GCIA/
Your success in GIAC GCIA is our sole target and we develop all our GCIA braindumps in a way that facilitates the attainment of this target. Not only is our GCIA study material the best you can find, it is also the most detailed and the most updated. GCIA Practice Exams for GIAC GCIA are written to the highest standards of technical accuracy.
Check GCIA free dumps before getting the full version:
NEW QUESTION 1
You work as a Network Administrator for Infonet Inc. The company has a Windows Server 2008 Active Directory-based single forest multiple domain IPv4 network. All the DNS servers on the network run Windows Server 2008. The users in the network use NetBIOS name to connect network application on the network. You have migrated the network to IPv6-enabled network. Now you want to enable DNS Server to perform lookups in GlobalNames Zone. Which of the following commands will you use to accomplish the task?
- A. Dnscmd <server name> /config /enableglobalnames 1
- B. Dnscmd <server name> /config /enableglobalnamessupport 0
- C. Dnscmd <server name> /config /enableglobalnamessupport 1
- D. Dnscmd <server name> /config /globalnamesqueryorder 0
Answer: C
NEW QUESTION 2
You work as a Network Administrator for Infonet Inc. The company has a Windows Server 2008 domain-based network. The network has three Windows Server 2008 member servers and 150 Windows Vista client computers. The network contains a Windows Server 2008 Core computer. You want to install the DNS server role on the Windows Server 2008 Core computer. Which of the following commands will you use to accomplish the task?
- A. start /w ocsetup DnsServercorerole
- B. net start "dns server"
- C. start /w ocsetup DNS-Server-Core-Role
- D. start /w ocsetup DnsServer
Answer: C
NEW QUESTION 3
Which of the following networks relies on the tunneling protocol?
- A. Wide Area Network (WAN)
- B. Virtual Private Network (VPN)
- C. Local Area Network (LAN)
- D. Wireless Network
Answer: B
NEW QUESTION 4
Which of the following are well-known ports?
Each correct answer represents a complete solution. Choose two.
- A. 443
- B. 21
- C. 1024
- D. 8080
Answer: AB
NEW QUESTION 5
Adam works as a Security Administrator for Umbrella Inc. A project has been assigned to him to secure access to the network of the company from all possible entry points. He segmented the network into several subnets and installed firewalls all over the network. He has placed very stringent rules on all the firewalls, blocking everything in and out except ports that must be used.
He does need to have port 80 open since his company hosts a website that must be accessed from the Internet. Adam is still worried about programs like Hping2 that can get into a network through covert channels.
Which of the following is the most effective way to protect the network of the company from an attacker using Hping2 to scan his internal network?
- A. Block ICMP type 13 messages
- B. Block all outgoing traffic on port 21
- C. Block all outgoing traffic on port 53
- D. Block ICMP type 3 messages
Answer: A
NEW QUESTION 6
Which of the following is used to hash the information in Netcat?
- A. MD5
- B. SHA-256
- C. MD5deep
- D. SHA-1
Answer: C
NEW QUESTION 7
Which of the following conclusions can be drawn from viewing the given output generated by the PING command-line utility?
- A. The network bandwidth is heavily utilize
- B. The IP address of the destination computer is not resolve
- C. There is no connectivity between the source and the destination compute
- D. The hub is not workin
Answer: C
NEW QUESTION 8
Which of the following ICMP types refers to the message "Time Exceeded"?
- A. Type 4
- B. Type 12
- C. Type 11
- D. Type 5
Answer: C
NEW QUESTION 9
Which of the following is not a Denial of Service (DoS) attack?
- A. Smurf attack
- B. Code injection attack
- C. Ping of Death attack
- D. Teardrop attack
Answer: B
NEW QUESTION 10
You work as a Network Administrator for McNeil Inc. The company's Windows 2000-based network is configured with Internet Security and Acceleration (ISA) Server 2000. You want to configure intrusion detection on the server. You find that the different types of attacks on the Intrusion Detection tab page of the IP Packet Filters Properties dialog box are disabled. What is the most likely cause?
- A. The PPTP through ISA firewall check box on the PPTP tab page of the IP Packet Filters Properties dialog box is not enable
- B. The Enable IP routing check box on the General tab page of the IP Packet Filters Properties dialog box is not selecte
- C. The Log packets from Allow filters check box on the Packet Filters tab page of the IP Packet Filters Properties dialog box is not enable
- D. The Enable Intrusion detection check box on the General tab page of the IP Packet Filters Properties dialog box is not selecte
Answer: D
NEW QUESTION 11
You work as a Network Administrator for Tech Perfect Inc. The office network is configured as an IPv6 network. You have to configure a computer with the IPv6 address, which is equivalent to an IPv4 publicly routable address. Which of the following types of addresses will you choose?
- A. Site-local
- B. Global unicast
- C. Local-link
- D. Loopback
Answer: B
NEW QUESTION 12
Which of the following algorithms produces a digital signature which is used to authenticate the bit-stream images?
- A. MD6
- B. MD5
- C. BOINIC
- D. HashClash
Answer: B
NEW QUESTION 13
You work as a Network Administrator for Tech Perfect Inc. The company has a TCP/IP-based routed network. You have recently come to know about the Slammer worm, which attacked computers in 2003 and doubled the number of infected hosts every 9 seconds or so. Slammer infected 75000 hosts in the first 10 minutes of the attack. To mitigate such security threats, you want to configure security tools on the network. Which of the following tools will you use?
- A. Intrusion Prevention Systems
- B. Firewall
- C. Intrusion Detection Systems
- D. Anti-x
Answer: A
NEW QUESTION 14
Which of the following units of data does the data-link layer send from the network layer to the physical layer of the OSI model?
- A. Protocols
- B. Raw bits
- C. Data packets
- D. Data frames
- E. Data segments
Answer: D
NEW QUESTION 15
Adam works as a Computer Hacking Forensic Investigator in a law firm. He has been assigned with his first project. Adam collected all required evidences and clues. He is now required to write an investigative report to present before court for further prosecution of the case. He needs guidelines to write an investigative report for expressing an opinion. Which of the following are the guidelines to write an investigative report in an efficient way?
Each correct answer represents a complete solution. Choose all that apply.
- A. All ideas present in the investigative report should flow logically from facts to conclusion
- B. Opinion of a lay witness should be included in the investigative repor
- C. The investigative report should be understandable by any reade
- D. There should not be any assumptions made about any facts while writing the investigative repor
Answer: ACD
NEW QUESTION 16
In which of the following IDS evasion attacks does an attacker send a data packet such that IDS accepts the data packet but the host computer rejects it?
- A. Fragmentation overlap attack
- B. Evasion attack
- C. Fragmentation overwrite attack
- D. Insertion attack
Answer: D
NEW QUESTION 17
Which of the following methods is used by forensic investigators to acquire an image over the network in a secure manner?
- A. DOS boot disk
- B. EnCase with a hardware write blocker
- C. Linux Live CD
- D. Secure Authentication for EnCase (SAFE)
Answer: D
NEW QUESTION 18
Which of the following is the default port used by Simple Mail Transfer Protocol (SMTP)?
- A. 80
- B. 25
- C. 20
- D. 21
Answer: B
NEW QUESTION 19
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He has written the following snort signature: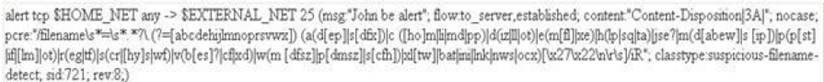
Which of the following statements about this snort signature is true?
- A. It detects the session splicing IDS evasion attac
- B. It detects AOL IM cha
- C. It detects Yahoo IM cha
- D. It detects the bad file attachments coming to the mail serve
Answer: D
NEW QUESTION 20
......
Thanks for reading the newest GCIA exam dumps! We recommend you to try the PREMIUM Allfreedumps.com GCIA dumps in VCE and PDF here: https://www.allfreedumps.com/GCIA-dumps.html (508 Q&As Dumps)