2026 New JN0-230 Exam Dumps with PDF and VCE Free: https://www.2passeasy.com/dumps/JN0-230/
Ucertify offers free demo for JN0-230 exam. "Security - Associate (JNCIA-SEC)", also known as JN0-230 exam, is a Juniper Certification. This set of posts, Passing the Juniper JN0-230 exam, will help you answer those questions. The JN0-230 Questions & Answers covers all the knowledge points of the real exam. 100% real Juniper JN0-230 exams and revised by experts!
Check JN0-230 free dumps before getting the full version:
NEW QUESTION 1
Which statements about NAT are correct? (Choose two.)
- A. When multiple NAT rules have overlapping match conditions, the rule listed first is chosen.
- B. Source NAT translates the source port and destination IP address.
- C. Source NAT translates the source IP address of packet.
- D. When multiple NAT rules have overlapping match conditions, the most specific rule is chosen.
Answer: AC
NEW QUESTION 2
Users in your network are downloading files with file extensions that you consider to be unsafe for your network. You must prevent files with specific file extensions from entering your network.
Which UTM feature should be enable on an SRX Series device to accomplish this task?
- A. Content filtering
- B. Web filtering
- C. Antispam
- D. URL filtering
Answer: A
NEW QUESTION 3
You have created a zones-based security policy that permits traffic to a specific webserver for the marketing team. Other groups in the company are not permitted to access the webserver. When marketing users attempt to access the server they are unable to do so.
What are two reasons for this access failure? (Choose two.)
- A. You failed to change the source zone to include any source zone.
- B. You failed to position the policy after the policy that denies access to the webserver.
- C. You failed to commit the policy change.
- D. You failed to position the policy before the policy that denies access the webserver
Answer: CD
NEW QUESTION 4
Which three actions would be performed on traffic traversing an IPsec VPAN? (Choose three.)
- A. Port forwarding
- B. Authentication
- C. Encryption
- D. Deep inspection
- E. Payload verification
Answer: BCE
NEW QUESTION 5
Referring to the exhibit.
****Exhibit is Missing****
Which type of NAT is performed by the SRX Series device?
- A. Source NAT with PAT
- B. Source Nat without PAT
- C. Destination NAT without PAT
- D. Destination NAT with PAT
Answer: D
NEW QUESTION 6
You configure and applied several global policies and some of the policies have overlapping match criteria.
- A. In this scenario, how are these global policies applies?
- B. The first matched policy is the only policy applied.
- C. The most restrictive that matches is applied.
- D. The least restrictive policy that matches is applied.
Answer: A
NEW QUESTION 7
Users on the network are restricted from accessing Facebook, however, a recent examination of the logs show that users are accessing Facebook.
Referring to the exhibit,
Why is this problem happening?
- A. Global rules are honored before zone-based rules.
- B. The internet-Access rule has a higher precedence value
- C. The internet-Access rule is listed first
- D. Zone-based rules are honored before global rules
Answer: D
NEW QUESTION 8
What are two characteristic of static NAT SRX Series devices? (Choose two.)
- A. Source and destination NAT rules take precedence over static NAT rules.
- B. A reverse mapping rule is automatically created for the source translation.
- C. Static NAT rule take precedence over source and destination NAT rules.
- D. Static rules cannot coexist with destination NAT rules on the same SRX Series device configuration.
Answer: BC
NEW QUESTION 9
Which two segments describes IPsec VPNs? (Choose two.)
- A. IPsec VPN traffic is always authenticated.
- B. IPsec VPN traffic is always encrypted.
- C. IPsec VPNs use security to secure traffic over a public network between two remote sites.
- D. IPsec VPNs are dedicated physical connections between two private networks.
Answer: AC
NEW QUESTION 10
Referring to the exhibit.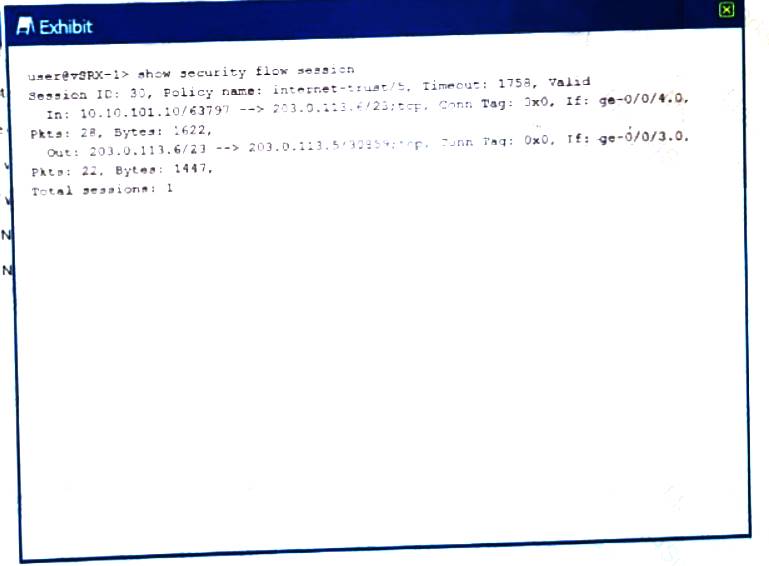
Which type of NAT is being performed?
- A. Source NAT with PAT
- B. Source NAT without PAT
- C. Destination NAT without PAT
- D. Destination NAT with PAT
Answer: A
NEW QUESTION 11
Which actions would be applied for the pre-ID default policy unified policies?
- A. Redirect the session
- B. Reject the session
- C. Log the session
- D. Silently drop the session
Answer: C
NEW QUESTION 12
Which two statements are true about UTM on an SRX340? (Choose two.)
- A. A default UTM policy is created.
- B. No default profile is created.
- C. No default UTM policy is created
- D. A default UTM profile is created
Answer: BC
NEW QUESTION 13
Which two actions are performed on an incoming packet matching an existing session? (Choose two.)
- A. Zone processing
- B. Security policy evolution
- C. Service ALG processing
- D. Screens processing
Answer: CD
NEW QUESTION 14
Which two feature on the SRX Series device are common across all Junos devices? (Choose two.)
- A. Stateless firewall filters
- B. UTM services
- C. The separation of control and forwarding planes
- D. screens
Answer: AC
NEW QUESTION 15
Which two notifications are available when the antivirus engine detects and infected file? (Choose two.)
- A. e-mail notifications
- B. SNMP notifications
- C. SMS notifications
- D. Protocol-only notification
Answer: AD
NEW QUESTION 16
Which two statements are true about security policy actions? (Choose two.)
- A. The reject action drops the traffic and sends a message to the source device.
- B. The deny action silently drop the traffic.
- C. The deny action drops the traffic and sends a message to the source device.
- D. The reject action silently drops the traffic.
Answer: AB
NEW QUESTION 17
What must you do first to use the Monitor/Events workspace in the j-Web interface?
- A. You must enable stream mode security logging on the SRX Series device
- B. You must enable event mode security logging on the SRX Series device.
- C. You must enable security logging that uses the SD-Syslog format.
- D. You must enable security logging that uses the TLS transport mode.
Answer: B
NEW QUESTION 18
Which two match conditions would be used in both static NAT and destination NAT rule sets? (Choose two.)
- A. Destination zone
- B. Destination interface
- C. Source interface
- D. Source zone
Answer: BD
NEW QUESTION 19
Which statement is correct about IKE?
- A. IKE phase 1 is used to establish the data path
- B. IKE phase 1 only support aggressive mode.
- C. IKE phase 1 negotiates a secure channel between gateways.
- D. IKE phase 1 establishes the tunnel between devices
Answer: C
NEW QUESTION 20
Which two private cloud solution support vSRX devices? (Choose two.)
- A. Microsoft Azure
- B. Amazon Web Services (AWS)
- C. VMware Web Services (AWS)
- D. VMware NSX
- E. Contrail Cloud
Answer: AB
NEW QUESTION 21
The Sky ATP premium or basic-Threat Feed license is needed fort which two features? (Choose two.)
- A. Outbound protection
- B. C&C feeds
- C. Executable inspection
- D. Custom feeds
Answer: BD
NEW QUESTION 22
What is the purpose of the Shadow Policies workspace in J-Web?
- A. The Shadow Policies workspace shows unused security policies due to policy overlap.
- B. The Shadow Policies workspace shows unused IPS policies due to policy overlap.
- C. The Shadow Policies workspace shows used security policies due to policy overlap
- D. The Shadow Policies workspace shows used IPS policies due to policy overlap
Answer: A
NEW QUESTION 23
Which two statements are correct about using global-based policies over zone-based policies? (Choose two.)
- A. With global-based policies, you do not need to specify a destination zone in the match criteria.
- B. With global-based policies, you do not need to specify a source zone in the match criteria.
- C. With global-based policies, you do not need to specify a destination address in the match criteria.
- D. With global-based policies, you do not need to specify a source address in the match criteria.
Answer: AB
NEW QUESTION 24
You have configured a Web filtering UTM policy?
Which action must be performed before the Web filtering UTM policy takes effect?
- A. The UTM policy must be linked to an egress interface
- B. The UTM policy be configured as a routing next hop.
- C. The UTM policy must be linked to an ingress interface.
- D. The UTM policy must be linked to a security policy
Answer: D
NEW QUESTION 25
Which statements is correct about global security policies?
- A. Global policies allow you to regulate traffic with addresses and applications, regardless of their security zones.
- B. Traffic matching global is not added to the session table.
- C. Global policies eliminate the need to assign interface to security zones.
- D. Global security require you to identify a source and destination zone.
Answer: A
NEW QUESTION 26
......
Recommend!! Get the Full JN0-230 dumps in VCE and PDF From Certshared, Welcome to Download: https://www.certshared.com/exam/JN0-230/ (New 65 Q&As Version)