2026 New P2150-870 Exam Dumps with PDF and VCE Free: https://www.2passeasy.com/dumps/P2150-870/
Want to know Testking P2150-870 Exam practice test features? Want to lear more about IBM Technical Sales Foundations for IBM Security Intelligence and Analytics V1 certification experience? Study 100% Guarantee IBM P2150-870 answers to Up to date P2150-870 questions at Testking. Gat a success with an absolute guarantee to pass IBM P2150-870 (Technical Sales Foundations for IBM Security Intelligence and Analytics V1) test on your first attempt.
Check P2150-870 free dumps before getting the full version:
NEW QUESTION 1
To view flow data in QRadar, which tab should a user navigate to?
- A. Assets
- B. Log Activity
- C. User Analytics
- D. Network Activity
Answer: A
NEW QUESTION 2
Which types of software appliance are involved of an events is received by an Event Collector, and the event is then to an Event Processor and causes an Offense to be updated on the Console?
- A. 13xx to 17xx to 31xx
- B. 13xx to 18xxt o 21xx
- C. 13xx to 16xx to 31xx
- D. 15xx to 17xx to 21xx
Answer: C
NEW QUESTION 3
Which categorizes a threat to a type of attack?
- A. Sniffin
- B. Interruption
- C. SQL injection, Interception
- D. Man in the middle, Fabrication
- E. Denial of Service, Modification
Answer: B
NEW QUESTION 4
What is the least secure of the five transmission types?
- A. Wireless
- B. Fiber Optic
- C. Coaxial Cable
- D. Shielded Twisted Pair
- E. Unshielded Twisted Pair
Answer: C
NEW QUESTION 5
What type of appliance is a 3105?
- A. Flow Collector
- B. Event Collector
- C. Event Processor
- D. All in One OR Console
Answer: A
NEW QUESTION 6
Which TCP/IP protocols are at layer 4 of the OSI model (Select 2)
- A. TCP
- B. UDP
- C. ARP
- D. ICMP
- E. IGMP
Answer: AB
NEW QUESTION 7
Which is the most common formatused to send event data to a SIEM?
- A. JSON
- B. LEEF
- C. Syslog
- D. NetFlow
Answer: D
NEW QUESTION 8
Which QRadar Apps integrate with the User Behaviour Analytics App to enhance its detection capabilities?
- A. QRadar Risk Manager and QRadar Network Security
- B. QRadar Machine Learning App and Reference Data Import - LDAP
- C. QRadar Asset Profiler App and Palo Alto Networks App for QRadar
- D. QRadar Incident Remediation App and QRadar Artificial Analysis App
Answer: C
NEW QUESTION 9
Which case shows how approximately 1000 Events per second, using an encrypted channel, can be sent from a private cloud to a QRader processor?
- A. Place an event processor in the private cloud, and forward the events to another event collector.
- B. Place a risk manager appliance in the private cloud, and forward the events to another event collector.
- C. Place a packet capture appliance in the private cloud, and forward the events to a cloud events processor.
- D. Place an event collector in the private cloud, and forward the event to the customers event processor.
Answer: A
NEW QUESTION 10
In this diagram, showing the Ariel Search Flow, what is the name of the components as ‘X’, running on the Console?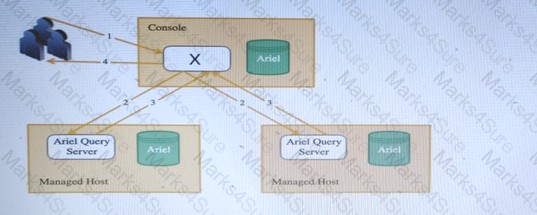
- A. AQL Processor
- B. Ariel Proxy Server
- C. Ariel Query Server
- D. REST -API endpoint
Answer: A
NEW QUESTION 11
What would be relevant questions to ask for scoping the environment? (Select 3)
- A. How many data centers do you have?
- B. How many users will be using QRadar?
- C. How many storage networks to you have?
- D. How many QRadar appliances do you want to acquire?
- E. How many log sources do you want to add to the project?
- F. In how many countries do you want to deploy QRadar?
- G. Which compliance extensions do you need to deploy?
Answer: CFG
NEW QUESTION 12
Which metrics are defined for the three virtual appliance system specification (Minimum/Medium/High). (select 4)
- A. NICs
- B. IOPS
- C. Memory
- D. Storage
- E. CPU cores/speed
- F. Maximum Latency
- G. Virtual Networks
Answer: ACEG
NEW QUESTION 13
In which use case can QRadar Vulnerability Manager be used to detect a particular vulnerability and assist in remediating?
QRadar Vulnerability Manager:
- A. to patch systems for high risk vulnerabilities.
- B. to analyze events from and to a known Botnet site.
- C. to extract packets and reconstruct the network traffic session.
- D. for searching which systems are vulnerable to a particular exploit and what Intrusion Preventions systems can be used to remediate it.
Answer: D
NEW QUESTION 14
How can assets be used to help in investigations?
- A. As valuable data sources.
- B. Make searching for offenses easier.
- C. Help connect an offense to a device.
- D. Provide external threat intelligence.
Answer: D
NEW QUESTION 15
What does QRadar Incident Forensics do? QRadar Incident Forensics:
- A. analyzes event data for an incident that is discovered by QRadar SI EM.
- B. analyzes flow data for an incident that is discovered by a QRadar SI EM.
- C. brings in the vulnerability data relevant for an incident that is discovered by QRadar SIEM.
- D. aggregates the relevant network data for an incident that is discovered by QRadar SIEM.
Answer: A
NEW QUESTION 16
Which is a valid use case for implementing QRadar reference data collections?
- A. Change all incoming events to add an additional field value.
- B. Provide an index for all data (events and flow data) in real time.
- C. Store hash values and test each incoming hash against this set
- D. Speed up dashboard functions due to caching common widget data sets
Answer: C
NEW QUESTION 17
Which is a valid use case for QRadar Network Insights (QN|)?
- A. Finding anomalies and behavior exceptions in event traffic volumes
- B. Analyzing network traffic and finding document hashes from email attachments.
- C. Discovering the network topology within the enterprise based on retrieving the firewall and router/switch rule sets.
- D. Doing after the factreconstruction of user web sessions, chat sessions, and documents, and finding relations between all these.
Answer: C
NEW QUESTION 18
Which IBM artificial intelligence service can be used to speed up analysis of external threats?
- A. QRadar Incident Overview
- B. QRadar Advisor with Watson
- C. QRadar Machine Learning Analytics
- D. QRadar Artificial Intelligence toolbox
Answer: D
NEW QUESTION 19
......
P.S. Certshared now are offering 100% pass ensure P2150-870 dumps! All P2150-870 exam questions have been updated with correct answers: https://www.certshared.com/exam/P2150-870/ (40 New Questions)