2026 New PT0-001 Exam Dumps with PDF and VCE Free: https://www.2passeasy.com/dumps/PT0-001/
Your success in CompTIA PT0-001 is our sole target and we develop all our PT0-001 braindumps in a way that facilitates the attainment of this target. Not only is our PT0-001 study material the best you can find, it is also the most detailed and the most updated. PT0-001 Practice Exams for CompTIA CompTIA Other Exam PT0-001 are written to the highest standards of technical accuracy.
Free PT0-001 Demo Online For CompTIA Certifitcation:
NEW QUESTION 1
A client is asking a penetration tester to evaluate a new web application for availability. Which of the following types of attacks should the tester use?
- A. TCP SYN flood
- B. SQL injection
- C. xss
- D. XMAS scan
Answer: A
NEW QUESTION 2
During a penetration test, a tester runs a phishing campaign and receives a shell from an internal PC running Windows 10 OS. The tester wants to perform credential harvesting with Mimikazt. Which of the following registry changes would allow for credential caching in memory?
A)
B)
C)
D)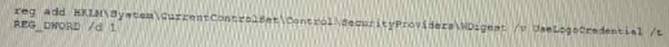
- A. Option A
- B. Option B
- C. Option C
- D. Option D
Answer: D
NEW QUESTION 3
After successfully capturing administrator credentials to a remote Windows machine, a penetration tester attempts to access the system using PSExec but is denied permission. Which of the following shares must be accessible for a successful PSExec connection?
- A. IPCS and C$
- B. C$ and ADMINS
- C. SERVICES and ADMINS
- D. ADMINS and IPCS
Answer: C
NEW QUESTION 4
A penetration tester has compromised a host. Which of the following would be the correct syntax to create a Netcat listener on the device?
- A. nc -lvp 4444 /bin/bash
- B. nc -vp 4444 /bin/bash
- C. nc -p 4444 /bin/bash
- D. nc -lp 4444 -e /bin/bash
Answer: D
NEW QUESTION 5
A penetration testet is attempting to capture a handshake between a client and an access point by monitoring a WPA2-PSK secured wireless network The (ester is monitoring the correct channel tor the identified network but has been unsuccessful in capturing a handshake Given this scenario, which of the following attacks would BEST assist the tester in obtaining this handshake?
- A. Karma attack
- B. Deauthentication attack
- C. Fragmentation attack
- D. SSID broadcast flood
Answer: B
NEW QUESTION 6
During an internal penetration test, several multicast and broadcast name resolution requests are observed traversing the network. Which of the following tools could be used to impersonate network resources and collect authentication requests?
- A. Ettercap
- B. Tcpdump
- C. Responder
- D. Medusa
Answer: D
NEW QUESTION 7
Given the following script: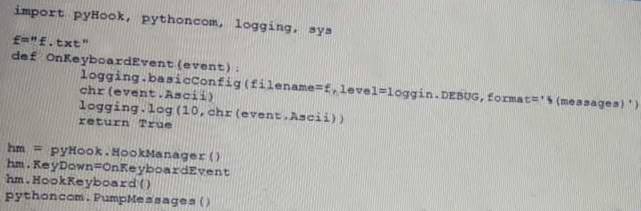
Which of the following BEST describes the purpose of this script?
- A. Log collection
- B. Event logging
- C. Keystroke monitoring
- D. Debug message collection
Answer: C
NEW QUESTION 8
A tester has captured a NetNTLMv2 hash using Responder Which of the following commands will allow the tester to crack the hash using a mask attack?
- A. hashcat -m 5600 -r rulea/beat64.rule hash.txt wordliat.txt
- B. hashcax -m 5€00 hash.txt
- C. hashc&t -m 5600 -a 3 haah.txt ?a?a?a?a?a?a?a?a
- D. hashcat -m 5600 -o reaulta.txt hash.txt wordliat.txt
Answer: A
NEW QUESTION 9
A security analyst has uncovered a suspicious request in the logs for a web application. Given the following URL: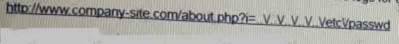
- A. Directory traversal
- B. Cross-site scripting
- C. Remote file inclusion
- D. User enumeration
Answer: D
NEW QUESTION 10
The following command is run on a Linux file system: Chmod 4111 /usr/bin/sudo
Which of the following issues may be explogted now?
- A. Kernel vulnerabilities
- B. Sticky bits
- C. Unquoted service path
- D. Misconfigured sudo
Answer: D
NEW QUESTION 11
Which of the following has a direct and significant impact on the budget of the security assessment?
- A. Scoping
- B. Scheduling
- C. Compliance requirement
- D. Target risk
Answer: A
NEW QUESTION 12
DRAG DROP
A manager calls upon a tester to assist with diagnosing an issue within the following Python script:
#!/usr/bin/python
s = "Administrator"
The tester suspects it is an issue with string slicing and manipulation Analyze the following code segment and drag and drop the correct output for each string manipulation to its corresponding code segment Options may be used once or not at all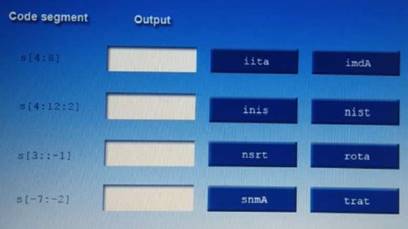
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
Nsrt
Snma
Trat
Imda
NEW QUESTION 13
A penetration tester has successfully explogted an application vulnerability and wants to remove the command history from the Linux session. Which of the following will accomplish this successfully?
- A. history --remove
- B. cat history I clear
- C. rm -f ./history
- D. history -c
Answer: D
NEW QUESTION 14
A penetration tester notices that the X-Frame-Optjons header on a web application is not set. Which of the following would a malicious actor do to explogt this configuration setting?
- A. Use path modification to escape the application's framework.
- B. Create a frame that overlays the application.
- C. Inject a malicious iframe containing JavaScript.
- D. Pass an iframe attribute that is maliciou
Answer: B
NEW QUESTION 15
A penetration test was performed by an on-staff technicians junior technician. During the test, the technician discovered the application could disclose an SQL table with user account and password information. Which of the following is the MOST effective way to notify management of this finding and its importance?
- A. Document Ihe findtngs with an executive summary, recommendations, and screenshots of the web apphcation disclosure.
- B. Connect to the SQL server using this information and change the password to one or two noncritical accounts to demonstrate a proof-of-concept to management.
- C. Notify the development team of the discovery and suggest that input validation be implementedon the web application's SQL query strings.
- D. Request that management create an RFP to begin a formal engagement with a professional penetration testing company.
Answer: B
NEW QUESTION 16
Which of the following types of physical security attacks does a mantrap mitigate-?
- A. Lock picking
- B. Impersonation
- C. Shoulder surfing
- D. Tailgating
Answer: D
NEW QUESTION 17
Given the following Python script: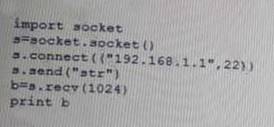
Which of the following actions will it perform?
- A. ARP spoofing
- B. Port scanner
- C. Reverse shell
- D. Banner grabbing
Answer: A
NEW QUESTION 18
After several attempts, an attacker was able to gain unauthorized access through a biometric sensor using the attacker's actual fingerprint without explogtation. Which of the following is the MOST likely explanation of what happened?
- A. The biometric device is tuned more toward false positives
- B. The biometric device is configured more toward true negatives
- C. The biometric device is set to fail closed
- D. The biometnc device duplicated a valid user's fingerpnn
Answer: A
NEW QUESTION 19
If a security consultant comes across a password hash that resembles the following b117 525b3454 7Oc29ca3dBaeOb556ba8
Which of the following formats is the correct hash type?
- A. Kerberos
- B. NetNTLMvl
- C. NTLM
- D. SHA-1
Answer: C
NEW QUESTION 20
DRAG DROP
During a penetration test, you gain access to a system with a limited user interface. This machine appears to have access to an isolated network that you would like to port scan. INSTRUCTIONS:
Analyze the code segments to determine which sections are needed to complete a port scanning script.
Drag the appropriate elements into the correct locations to complete the script.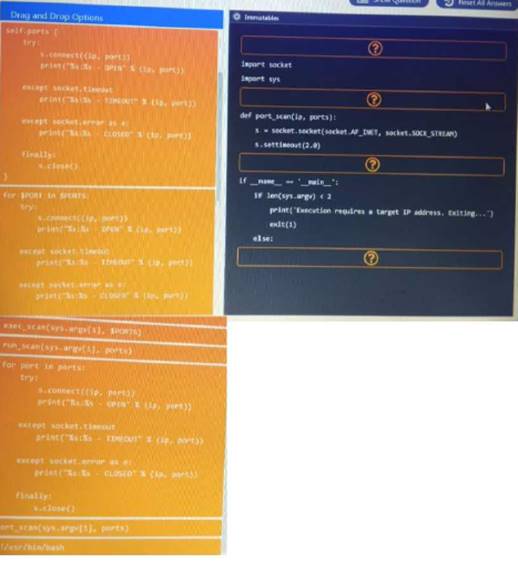
- A. Mastered
- B. Not Mastered
Answer: A
NEW QUESTION 21
HOTSPOT
You are a security analyst tasked with hardening a web server.
You have been given a list of HTTP payloads that were flagged as malicious.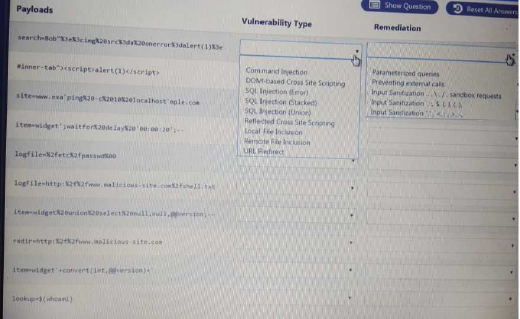

- A. Mastered
- B. Not Mastered
Answer: A
NEW QUESTION 22
A company contracted a firm specializing in penetration testing to assess the security of a core business application. The company provided the firm with a copy of the Java bytecode. Which of the following steps must the firm take before it can run a static code analyzer?
- A. Run the application through a dynamic code analyzer.
- B. Employ a fuzzing utility.
- C. Decompile the application.
- D. Check memory allocation
Answer: D
NEW QUESTION 23
Which of the following BEST explains why it is important to maintain confidentiality of any identified findings when performing a penetration test?
- A. Penetration test findings often contain company intellectual property
- B. Penetration test findings could lead to consumer dissatisfaction if made pubic
- C. Penetration test findings are legal documents containing privileged information
- D. Penetration test findings can assist an attacker in compromising a system
Answer: C
NEW QUESTION 24
A penetration tester successfully explogts a DM2 server that appears to be listening on an outbound port The penetration tester wishes to forward that traffic back to a device Which of the following are the BEST tools to use few this purpose? (Select TWO)
- A. Tcpdump
- B. Nmap
- C. Wiresrtark
- D. SSH
- E. Netcat
- F. Cain and Abel
Answer: CD
NEW QUESTION 25
A tester has determined that null sessions are enabled on a domain controller. Which of the following attacks can be performed to leverage this vulnerability?
- A. RID cycling to enumerate users and groups
- B. Pass the hash to relay credentials
- C. Password brute forcing to log into the host
- D. Session hijacking to impersonate a system account
Answer: C
NEW QUESTION 26
......
Thanks for reading the newest PT0-001 exam dumps! We recommend you to try the PREMIUM Passcertsure PT0-001 dumps in VCE and PDF here: https://www.passcertsure.com/PT0-001-test/ (145 Q&As Dumps)