2026 New SY0-601 Exam Dumps with PDF and VCE Free: https://www.2passeasy.com/dumps/SY0-601/
Want to know Examcollection SY0-601 Exam practice test features? Want to lear more about CompTIA CompTIA Security+ Exam certification experience? Study Highest Quality CompTIA SY0-601 answers to Update SY0-601 questions at Examcollection. Gat a success with an absolute guarantee to pass CompTIA SY0-601 (CompTIA Security+ Exam) test on your first attempt.
Also have SY0-601 free dumps questions for you:
NEW QUESTION 1
A security analyst has been asked to investigate a situation after the SOC started to receive alerts from the SIEM. The analyst first looks at the domain controller and finds the following events: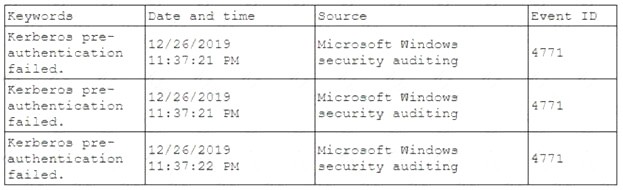
To better understand what is going on, the analyst runs a command and receives the following output: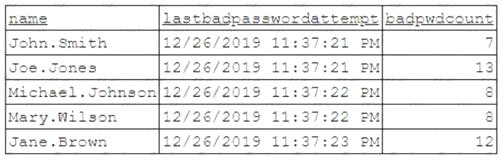
Based on the analyst’s findings, which of the following attacks is being executed?
- A. Credential harvesting
- B. Keylogger
- C. Brute-force
- D. Spraying
Answer: D
NEW QUESTION 2
After a ransomware attack a forensics company needs to review a cryptocurrency transaction between the victim and the attacker. Which of the following will the company MOST likely review to trace this transaction?
- A. The public ledger
- B. The NetFlow data
- C. A checksum
- D. The event log
Answer: A
NEW QUESTION 3
In which of the following common use cases would steganography be employed?
- A. Obfuscation
- B. Integrity
- C. Non-repudiation
- D. Blockchain
Answer: A
NEW QUESTION 4
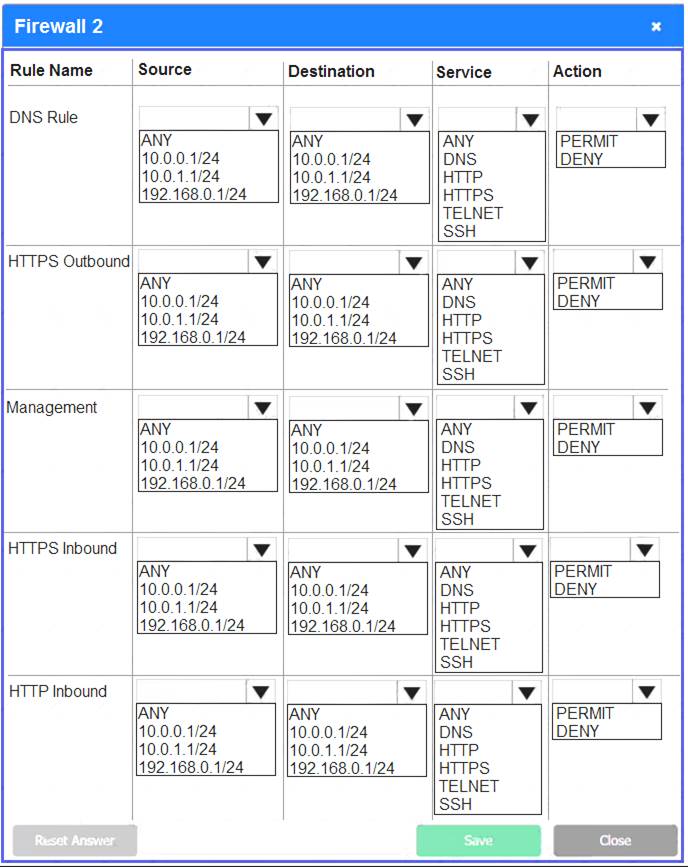
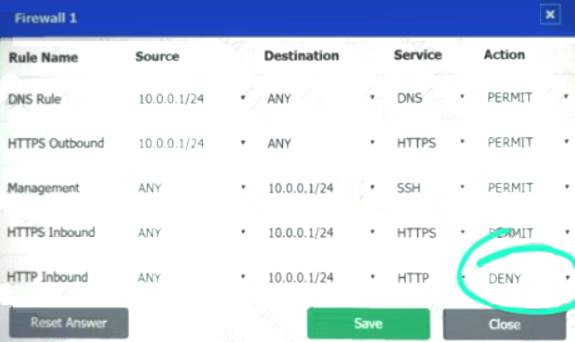
A company recently added a DR site and is redesigning the network. Users at the DR site are having issues browsing websites. INSTRUCTIONS
Click on each firewall to do the following:  Deny cleartext web traffic.
Deny cleartext web traffic. Ensure secure management protocols are used.
Ensure secure management protocols are used.  Resolve issues at the DR site.
Resolve issues at the DR site.
The ruleset order cannot be modified due to outside constraints.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.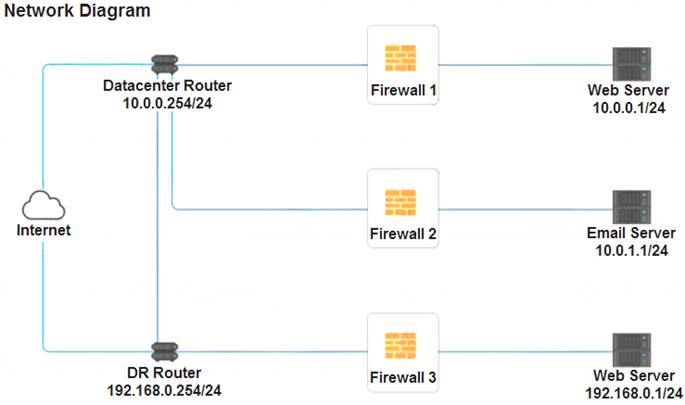

- A.
Answer: A
Explanation:
See explanation below.
Explanation
Firewall 1: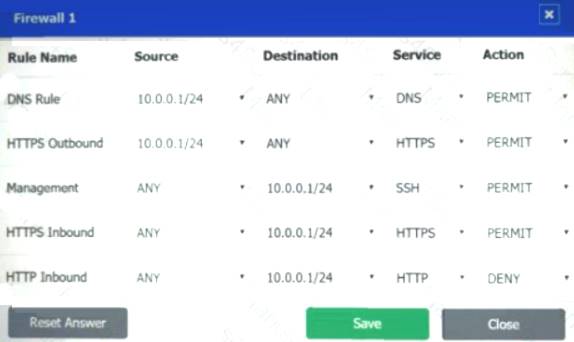
DNS Rule – ANY --> ANY --> DNS --> PERMIT
HTTPS Outbound – 10.0.0.1/24 --> ANY --> HTTPS --> PERMIT Management – ANY --> ANY --> SSH --> PERMIT
HTTPS Inbound – ANY --> ANY --> HTTPS --> PERMIT HTTP Inbound – ANY --> ANY --> HTTP --> DENY
Firewall 2: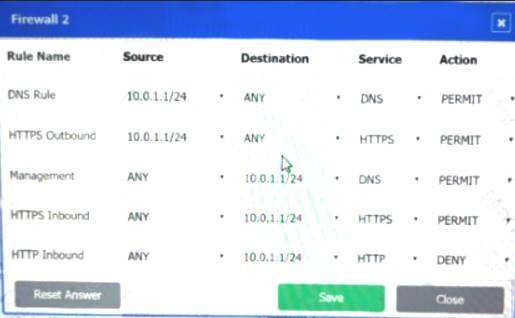

Firewall 3:
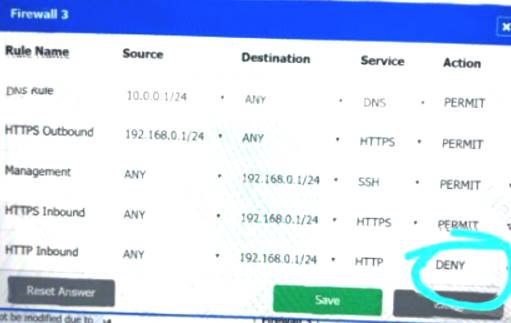
DNS Rule – ANY --> ANY --> DNS --> PERMIT
HTTPS Outbound – 192.168.0.1/24 --> ANY --> HTTPS --> PERMIT Management – ANY --> ANY --> SSH --> PERMIT
HTTPS Inbound – ANY --> ANY --> HTTPS --> PERMIT HTTP Inbound – ANY --> ANY --> HTTP --> DENY
NEW QUESTION 5
A company needs to centralize its logs to create a baseline and have visibility on its security events. Which of the following technologies will accomplish this objective?
- A. Security information and event management
- B. A web application firewall
- C. A vulnerability scanner
- D. A next-generation firewall
Answer: A
NEW QUESTION 6
A security administrator currently spends a large amount of time on common security tasks, such aa report generation, phishing investigations, and user provisioning and deprovisioning This prevents the administrator from spending time on other security projects. The business does not have the budget to add more staff members. Which of the following should the administrator implement?
- A. DAC
- B. ABAC
- C. SCAP
- D. SOAR
Answer: D
NEW QUESTION 7
The SOC is reviewing process and procedures after a recent incident. The review indicates it took more than 30 minutes to determine that quarantining an infected host was the best course of action. The allowed the malware to spread to additional hosts before it was contained. Which of the following would be BEST to improve the incident response process?
- A. Updating the playbooks with better decision points
- B. Dividing the network into trusted and untrusted zones
- C. Providing additional end-user training on acceptable use
- D. Implementing manual quarantining of infected hosts
Answer: A
NEW QUESTION 8
A user reports constant lag and performance issues with the wireless network when working at a local coffee shop. A security analyst walks the user through an installation of Wireshark and get a five-minute pcap to analyze. The analyst observes the following output: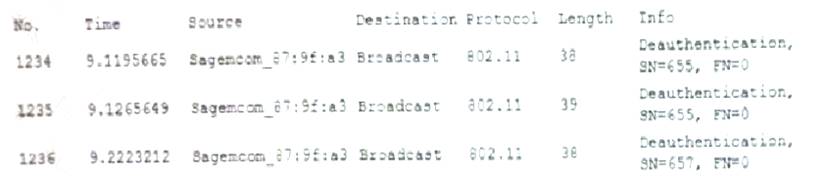
Which of the following attacks does the analyst MOST likely see in this packet capture?
- A. Session replay
- B. Evil twin
- C. Bluejacking
- D. ARP poisoning
Answer: B
NEW QUESTION 9
In the middle of a cybersecurity, a security engineer removes the infected devices from the network and lock down all compromised accounts. In which of the following incident response phases is the security engineer currently operating?
- A. Identification
- B. Preparation
- C. Eradiction
- D. Recovery
- E. Containment
Answer: E
NEW QUESTION 10
A public relations team will be taking a group of guest on a tour through the facility of a large e-commerce company. The day before the tour, the company sends out an email to employees to ensure all whiteboars are cleaned and all desks are cleared. The company is MOST likely trying to protect against.
- A. Loss of proprietary information
- B. Damage to the company’s reputation
- C. Social engineering
- D. Credential exposure
Answer: C
NEW QUESTION 11
A university with remote campuses, which all use different service providers, loses Internet connectivity across all locations. After a few minutes, Internet and VoIP services are restored, only to go offline again at random intervals, typically within four minutes of services being restored. Outages continue throughout the day, impacting all inbound and outbound connections and services. Services that are limited to the local LAN or WiFi network are not impacted, but all WAN and VoIP services are affected.
Later that day, the edge-router manufacturer releases a CVE outlining the ability of an attacker to exploit the SIP protocol handling on devices, leading to resource exhaustion and system reloads. Which of the following BEST describe this type of attack? (Choose two.)
- A. DoS
- B. SSL stripping
- C. Memory leak
- D. Race condition
- E. Shimming
- F. Refactoring
Answer: AD
NEW QUESTION 12
A security analyst reviews the datacenter access logs for a fingerprint scanner and notices an abundance of errors that correlate with users' reports of issues accessing the facility. Which of the following MOST likely the cause of the cause of the access issues?
- A. False rejection
- B. Cross-over error rate
- C. Efficacy rale
- D. Attestation
Answer: B
NEW QUESTION 13
A security administrator checks the table of a network switch, which shows the following output: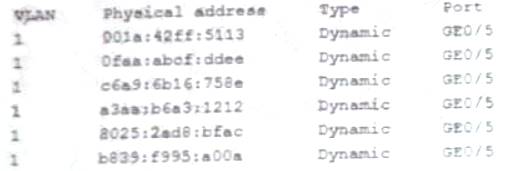
Which of the following is happening to this switch?
- A. MAC Flooding
- B. DNS poisoning
- C. MAC cloning
- D. ARP poisoning
Answer: A
NEW QUESTION 14
A company provides mobile devices to its users to permit access to email and enterprise applications. The company recently started allowing users to select from several different vendors and device models. When configuring the MDM, which of the following is a key security implication of this heterogeneous device approach?
- A. The most common set of MDM configurations will become the effective set of enterprise mobile security controls.
- B. All devices will need to support SCEP-based enrollment; therefore, the heterogeneity of the chosen architecture may unnecessarily expose private keys to adversaries.
- C. Certain devices are inherently less secure than others, so compensatory controls will be needed to address the delta between device vendors.
- D. MDMs typically will not support heterogeneous deployment environments, so multiple MDMs will need to be installed and configured.
Answer: C
NEW QUESTION 15
After entering a username and password, and administrator must gesture on a touch screen. Which of the following demonstrates what the administrator is providing?
- A. Multifactor authentication
- B. Something you can do
- C. Biometric
- D. Two-factor authentication
Answer: D
NEW QUESTION 16
A user recent an SMS on a mobile phone that asked for bank delays. Which of the following social-engineering techniques was used in this case?
- A. SPIM
- B. Vishing
- C. Spear phishing
- D. Smishing
Answer: D
NEW QUESTION 17
A cybersecurity analyst reviews the log files from a web server and sees a series of files that indicates a directory-traversal attack has occurred. Which of the following is the analyst MOST likely seeing?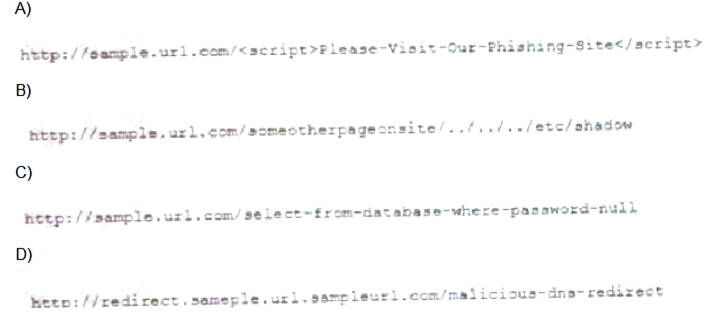
- A. Option A
- B. Option B
- C. Option C
- D. Option D
Answer: B
NEW QUESTION 18
A company recently moved sensitive videos between on-premises. Company-owned websites. The company then learned the videos had been uploaded and shared to the internet. Which of the following would MOST likely allow the company to find the cause?
- A. Checksums
- B. Watermarks
- C. Oder of volatility
- D. A log analysis
- E. A right-to-audit clause
Answer: D
NEW QUESTION 19
The facilities supervisor for a government agency is concerned about unauthorized access to environmental systems in the event the staff WiFi network is breached. Which of the blowing would BEST address this security concern?
- A. install a smart meter on the staff WiFi.
- B. Place the environmental systems in the same DHCP scope as the staff WiFi.
- C. Implement Zigbee on the staff WiFi access points.
- D. Segment the staff WiFi network from the environmental systems network.
Answer: D
NEW QUESTION 20
Which of the following control sets should a well-written BCP include? (Select THREE)
- A. Preventive
- B. Detective
- C. Deterrent
- D. Corrective
- E. Compensating
- F. Physical
- G. Recovery
Answer: ADG
NEW QUESTION 21
......
100% Valid and Newest Version SY0-601 Questions & Answers shared by DumpSolutions.com, Get Full Dumps HERE: https://www.dumpsolutions.com/SY0-601-dumps/ (New 218 Q&As)