2026 New 1D0-61C Exam Dumps with PDF and VCE Free: https://www.2passeasy.com/dumps/1D0-61C/
Vivid of 1D0-61C braindumps materials and preparation labs for CIW certification for consumer, Real Success Guaranteed with Updated 1D0-61C pdf dumps vce Materials. 100% PASS CIW Network Technology Associate exam Today!
Online CIW 1D0-61C free dumps demo Below:
NEW QUESTION 1
Jenny recently switched from broadband cable Internet to ADSL service with her local phone company.
To economize, she chose the self-installation option. It appears that her ADSL modem is not allowing her to connect to the Internet. Which setting should she check first?
- A. Loopback address
- B. Software version
- C. Default gateway
- D. Device name
Answer: C
NEW QUESTION 2
Wireless networks are subject to more security issues than standard wired networks. Which wireless security protocol can prevent unauthorized devices from connecting to the wireless network?
- A. WPA2
- B. RSA
- C. AES
- D. DES
Answer: A
NEW QUESTION 3
Which of the following is generally a component of a BYOD policy?
- A. Scope of control
- B. Insurance on devices
- C. Maintenance provision
- D. Device replacement or upgrade
Answer: A
NEW QUESTION 4
Sam is a professor at a small college. Due to a scheduling conflict, he was unable to obtain access to the computer lab to give the final exam. As an alternative, he asked students to bring their own devices (BYOD) and connect to the college’s Wi-Fi for network access. What security risk is associated with this implementation?
- A. Inability for students to share files
- B. Inability for students to back up user files
- C. Student devices sending unsecured data
- D. Student devices being more susceptible to malware
Answer: C
NEW QUESTION 5
John is the network administrator for a small company. The company’s network equipment has become outdated, and John has been asked to recommend a plan to update the company’s infrastructure. John has read extensively about the many advantages of using cloud-based services. Which of the following is an advantage of cloud-based services that John could cite to support his recommendation?
- A. Unlimited service options and choices
- B. Higher security in a cloud-based environment
- C. Elimination of need for high-speed Internet connection
- D. Elimination of equipment purchase and maintenance
Answer: D
NEW QUESTION 6
You have just been hired by a large company, and theIT manager is giving you an overview of the corporate network. He tells you that the corporation is spread out over several cities, and various departments are divided into subnetworks that are connected using routers. What type of network are you being shown?
- A. Local area network (LAN)
- B. Wide area network (WAN)
- C. Virtual private network (VPN)
- D. Internet Exchange Point (IPX)
Answer: B
NEW QUESTION 7
Carlos is the Information Technology (IT) administrator for a small company. Over the past year, employees have been using their personal mobile devices and smartphones for business use. This has reduced costs of purchasing new devices for employees. Carlos is now considering whether he should stop supplying employees with company phones and instead require all employees to use their personal smartphones for work. How can Carlos address the most significant security vulnerability?
- A. Develop a robust app to push security updates out to the various mobile OS devices
- B. Create an employee policy that requires employees to keep phones updated to the latest technology
- C. Create a policy that specifies acceptable use, ensuring security measures are in place for mobile devices
- D. Mandate that employees switch to the company’s mobile service provider to ensure security policies are enforced
Answer: C
NEW QUESTION 8
Which of the following is a security threat commonly associated with cloud-based services?
- A. Malware
- B. Phishing
- C. Hypervisor vulnerabilities
- D. Operating system vulnerabilities
Answer: C
NEW QUESTION 9
On your Windows laptop, you store all your vacation photos and your entire digital music library. Concerned about data loss, you perform frequent backups. Your laptop has recently been stolen and you need to restore your files to a desktop computer. Which Windows tool would you use to recover and set up the saved copies of your files onto your desktop computer?
- A. Backup and Restore
- B. Backup Recovery
- C. System Recovery
- D. System Restore
Answer: A
NEW QUESTION 10
SuperBank is considering a cloud service from Local Data Center, Inc., to support the bank’s expanding needs. SuperBank’s managers are concerned about security. What can SuperBank request to protect its data from security threats?
- A. For Local Data Center to run multiple hypervisors
- B. For Local Data Center to install a DDoS mitigation system
- C. For SuperBank staff to manage the servers at Local Data Center, Inc.
- D. For SuperBank to perform background checks on the staff at Local Data Center, Inc.
Answer: D
NEW QUESTION 11
Which security issue is most closely associated with wireless networks?
- A. Spoofing
- B. Wardriving
- C. Eavesdropping
- D. Man-in-the-middle
Answer: B
NEW QUESTION 12
You want to restrict host access to a wireless access point. What is the best way to do this?
- A. Enable MAC address filtering at each host.
- B. Log in to the access point and configure features, such as changing the SSID.
- C. Change the Direct Sequence Spread Spectrum (DSSS) signal at both the access point and each hosts NIC.
- D. Install software on the host you want to limit, then use a Web browser to log in to the host and configure it with the necessary settings to use the access point.
Answer: B
NEW QUESTION 13
The Internet has enabled many new anti-social activities, such as online stalking, cyberbullying, and addiction to solitary online activities. Which choice is the most feasible way for schools and parents to reduce cyberbullying?
- A. Monitor, track and record all online activity conducted by students.
- B. Teach teens that the use of online communication is a freedom of expression.
- C. Prevent students from accessing the Internet while at school so that they learn good habits.
- D. Educate students about cyber-ethics and the consequences of questionable online behavior.
Answer: D
NEW QUESTION 14
Patrick visits his teenage daughter’s social media page and discovers several offensive posts about one of her classmates. After speaking with his daughter, Patrick learns that several other girls in her class are upset with the classmate and have been posting, texting and e-mailing others about the girl. What is the best way for Patrick to help his daughter understand cyberbullying?
- A. He should advise his daughter to ignore the posts, texts and c-mails.
- B. He should explain to his daughter that she is participating in the bullying by accepting others’posts, texts and c-mails.
- C. He should explain to his daughter that the Internet embraces freedom of speech, and anyone is allowed to write anything.
- D. He should advise his daughter to delete all the posts, texts and c-mails she has received, as well as any new ones that appear.
Answer: B
NEW QUESTION 15
Lisa is traveling on company business. She has a company-issued smartphone with 4G access. Her hotel does not provide Internet access. What advantage does4G provide to help her access the Internet?
- A. She can use a 4G mobile hotspot device with her phone to connect her laptop to Wi-Fi.
- B. She can use the 4G phone to establish a VPN connection into the company network.
- C. She can use the41G phone to call and locate a public location that provides free Wi-Fl.
- D. She can use her41G phone’s GPS to identify another hotel that provides in-room Internet access.
Answer: A
NEW QUESTION 16
When using cloud-based services to host company data, a company’s disaster recovery plan should include strategies for:
- A. Creating redundancy and ensuring there is an exclusive contract with the cloud service provider.
- B. Distributing data and software services across multiple cloud service providers.
- C. Creating redundancy and using multiple cloud service providers.
- D. Using a single well-established cloud service provider.
Answer: C
NEW QUESTION 17
Server-based networks typically contain centralized network resources, which are usually not available on peer-to-peer (P2P) networks. Which of the following examples describes a serverbased network?
- A. Three network clients connecting to a file server
- B. Downloading a file by using BitTorrent technology
- C. Sharing one or more files to another computer via the Internet
- D. A client connecting to another computer over the Internet to share music
Answer: A
NEW QUESTION 18
Mobile computing has become a common necessity for both personal and business transactions. Which device has features similar to a smartphone but usually does not have telephone capabilities?
- A. Portable media player
- B. Netbook
- C. Laptop
- D. Tablet
Answer: D
NEW QUESTION 19
When a PC computer device wants to communicate with the processor, which system resource does it use?
- A. I/O
- B. DMA
- C. PIO
- D. IRQ
Answer: D
NEW QUESTION 20
To restore a backup file on a Windows-based computer, you:
- A. Use the Disk Management utility in the Microsoft Management Console (MMC).
- B. Use the BackupandRestore utility in the Control Panel.
- C. Use Device Manager in the Control Panel.
- D. Extract the backed-up file.
Answer: B
NEW QUESTION 21
Jose is experiencing performance problems with his notebook computer that he purchased a year ago. Upon discussing this issue with him, you learn that he has never deleted any temporary files since owning the device. What can Jose do to fix this problem most efficiently?
- A. Reformat his hard drive.
- B. Use the Windows chkdsk utility.
- C. Use the Windows Disk Cleanup utility.
- D. Back up his computer and delete the active partition.
Answer: C
NEW QUESTION 22
Acme Corp. is a small manufacturing company. To reduceIT infrastructure costs, it uses cloud- based services extensively and strives to have the least amount ofIT equipment onsite. Last year, Acme suffered a failure that resulted in significant down time and data loss. Management has decided to implement a continuous data protection (CDP) solution. Which type of CDP solution best fits Acme’s situation?
- A. Cloud-only solution
- B. Local systems solution
- C. Distributed network services provider
- D. Contracted network services provider
Answer: A
NEW QUESTION 23
Consider the network configuration shown in the command prompt: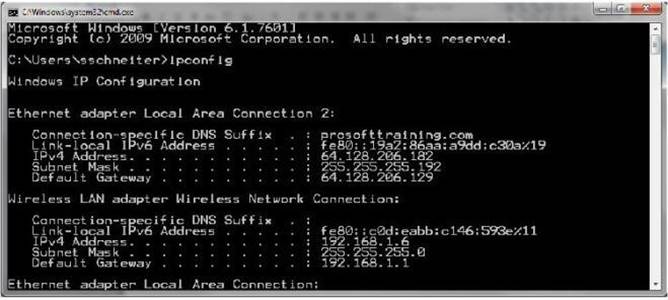
What does the Default Gateway identify?
- A. The file server on the network
- B. The local host on the network
- C. The computer on the network
- D. The router on the network
Answer: D
NEW QUESTION 24
Which type of attack is a form of social engineering in which an attacker attempts to steal personal or confidential information by sending e-mail that lures unsuspecting victims to log in to an authentic-looking but imposter Web site?
- A. Replay
- B. Phishing
- C. Spoofing
- D. Pharming
Answer: B
NEW QUESTION 25
You are distributing a large video game file using BitTorrent. First, you upload the initial file and make it available via a central server called a tracker. Other users can then connect to the tracker and download the file. Each user who downloads the file makesit available to other users todownload. The use of BitTorrent significantly reduces the original provider’s hardware and bandwidth resource costs. BitTorrent is an example of what type of network?
- A. Centralized network
- B. Client-server network
- C. Peer-to-peer (P2P) network
- D. Virtual private network (VPN)
Answer: C
NEW QUESTION 26
......
Thanks for reading the newest 1D0-61C exam dumps! We recommend you to try the PREMIUM Downloadfreepdf.net 1D0-61C dumps in VCE and PDF here: https://www.downloadfreepdf.net/1D0-61C-pdf-download.html (59 Q&As Dumps)