2026 New 312-50v11 Exam Dumps with PDF and VCE Free: https://www.2passeasy.com/dumps/312-50v11/
Master the 312-50v11 Certified Ethical Hacker Exam (CEH v11) content and be ready for exam day success quickly with this Exambible 312-50v11 test questions. We guarantee it!We make it a reality and give you real 312-50v11 questions in our EC-Council 312-50v11 braindumps.Latest 100% VALID EC-Council 312-50v11 Exam Questions Dumps at below page. You can use our EC-Council 312-50v11 braindumps and pass your exam.
Online EC-Council 312-50v11 free dumps demo Below:
NEW QUESTION 1
A new wireless client is configured to join a 802.11 network. This client uses the same hardware and software as many of the other clients on the network. The client can see the network, but cannot connect. A wireless packet sniffer shows that the Wireless Access Point (WAP) is not responding to the association requests being sent by the wireless client. What is a possible source of this problem?
- A. The WAP does not recognize the client’s MAC address
- B. The client cannot see the SSID of the wireless network
- C. Client is configured for the wrong channel
- D. The wireless client is not configured to use DHCP
Answer: A
NEW QUESTION 2
What term describes the amount of risk that remains after the vulnerabilities are classified and the countermeasures have been deployed?
- A. Residual risk
- B. Impact risk
- C. Deferred risk
- D. Inherent risk
Answer: A
NEW QUESTION 3
What hacking attack is challenge/response authentication used to prevent?
- A. Replay attacks
- B. Scanning attacks
- C. Session hijacking attacks
- D. Password cracking attacks
Answer: A
NEW QUESTION 4
Why would you consider sending an email to an address that you know does not exist within the company you are performing a Penetration Test for?
- A. To determine who is the holder of the root account
- B. To perform a DoS
- C. To create needless SPAM
- D. To illicit a response back that will reveal information about email servers and how they treat undeliverable mail
- E. To test for virus protection
Answer: D
NEW QUESTION 5
The collection of potentially actionable, overt, and publicly available information is known as
- A. Open-source intelligence
- B. Real intelligence
- C. Social intelligence
- D. Human intelligence
Answer: A
NEW QUESTION 6
To reach a bank web site, the traffic from workstations must pass through a firewall. You have been asked to review the firewall configuration to ensure that workstations in network 10.10.10.0/24 can only reach the bank web site 10.20.20.1 using https. Which of the following firewall rules meets this requirement?
- A. If (source matches 10.10.10.0/24 and destination matches 10.20.20.1 and port matches 443) then permit
- B. If (source matches 10.10.10.0/24 and destination matches 10.20.20.1 and port matches 80 or 443) then permit
- C. If (source matches 10.20.20.1 and destination matches 10.10.10.0/24 and port matches 443) then permit
- D. If (source matches 10.10.10.0 and destination matches 10.20.20.1 and port matches 443) then permit
Answer: A
NEW QUESTION 7
Which of the following tools is used to detect wireless LANs using the 802.11a/b/g/n WLAN standards on a linux platform?
- A. Kismet
- B. Abel
- C. Netstumbler
- D. Nessus
Answer: A
NEW QUESTION 8
Every company needs a formal written document which spells out to employees precisely what they are allowed to use the company's systems for, what is prohibited, and what will happen to them if they break the rules. Two printed copies of the policy should be given to every employee as soon as possible after they join the organization. The employee should be asked to sign one copy, which should be safely filed by the company. No one should be allowed to use the company's computer systems until they have signed the policy in acceptance of its terms.
What is this document called?
- A. Information Audit Policy (IAP)
- B. Information Security Policy (ISP)
- C. Penetration Testing Policy (PTP)
- D. Company Compliance Policy (CCP)
Answer: B
NEW QUESTION 9
Eve is spending her day scanning the library computers. She notices that Alice is using a computer whose port 445 is active and listening. Eve uses the ENUM tool to enumerate Alice machine. From the command prompt, she types the following command.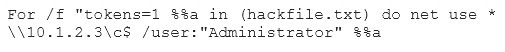
What is Eve trying to do?
- A. Eve is trying to connect as a user with Administrator privileges
- B. Eve is trying to enumerate all users with Administrative privileges
- C. Eve is trying to carry out a password crack for user Administrator
- D. Eve is trying to escalate privilege of the null user to that of Administrator
Answer: C
NEW QUESTION 10
During an Xmas scan what indicates a port is closed?
- A. No return response
- B. RST
- C. ACK
- D. SYN
Answer: B
NEW QUESTION 11
Which of the following is a component of a risk assessment?
- A. Administrative safeguards
- B. Physical security
- C. DMZ
- D. Logical interface
Answer: A
NEW QUESTION 12
DNS cache snooping is a process of determining if the specified resource address is present in the DNS cache records. It may be useful during the examination of the network to determine what software update resources are used, thus discovering what software is installed.
What command is used to determine if the entry is present in DNS cache?
- A. nslookup -fullrecursive update.antivirus.com
- B. dnsnooping –rt update.antivirus.com
- C. nslookup -norecursive update.antivirus.com
- D. dns --snoop update.antivirus.com
Answer: C
NEW QUESTION 13
An attacker is trying to redirect the traffic of a small office. That office is using their own mail server, DNS server and NTP server because of the importance of their job. The attacker gain access to the DNS server and redirect the direction www.google.com to his own IP address. Now when the employees of the office want to go to Google they are being redirected to the attacker machine. What is the name of this kind of attack?
- A. MAC Flooding
- B. Smurf Attack
- C. DNS spoofing
- D. ARP Poisoning
Answer: C
NEW QUESTION 14
What is correct about digital signatures?
- A. A digital signature cannot be moved from one signed document to another because it is the hash of the original document encrypted with the private key of the signing party.
- B. Digital signatures may be used in different documents of the same type.
- C. A digital signature cannot be moved from one signed document to another because it is a plain hash of the document content.
- D. Digital signatures are issued once for each user and can be used everywhere until they expire.
Answer: A
NEW QUESTION 15
By using a smart card and pin, you are using a two-factor authentication that satisfies
- A. Something you are and something you remember
- B. Something you have and something you know
- C. Something you know and something you are
- D. Something you have and something you are
Answer: B
NEW QUESTION 16
Which of the following is the best countermeasure to encrypting ransomwares?
- A. Use multiple antivirus softwares
- B. Pay a ransom
- C. Keep some generation of off-line backup
- D. Analyze the ransomware to get decryption key of encrypted data
Answer: C
NEW QUESTION 17
Eric has discovered a fantastic package of tools named Dsniff on the Internet. He has learnt to use these tools in his lab and is now ready for real world exploitation. He was able to effectively intercept communications between the two entities and establish credentials with both sides of the connections. The two remote ends of the communication never notice that Eric is relaying the information between the two. What would you call this attack?
- A. Interceptor
- B. Man-in-the-middle
- C. ARP Proxy
- D. Poisoning Attack
Answer: B
NEW QUESTION 18
If a token and 4-digit personal identification number (PIN) are used to access a computer system and the token performs off-line checking for the correct PIN, what type of attack is possible?
- A. Birthday
- B. Brute force
- C. Man-in-the-middle
- D. Smurf
Answer: B
NEW QUESTION 19
Bob, a network administrator at BigUniversity, realized that some students are connecting their notebooks in the wired network to have Internet access. In the university campus, there are many Ethernet ports available for professors and authorized visitors but not for students.
He identified this when the IDS alerted for malware activities in the network. What should Bob do to avoid this problem?
- A. Disable unused ports in the switches
- B. Separate students in a different VLAN
- C. Use the 802.1x protocol
- D. Ask students to use the wireless network
Answer: C
NEW QUESTION 20
If a tester is attempting to ping a target that exists but receives no response or a response that states the destination is unreachable, ICMP may be disabled and the network may be using TCP. Which other option could the tester use to get a response from a host using TCP?
- A. Traceroute
- B. Hping
- C. TCP ping
- D. Broadcast ping
Answer: B
NEW QUESTION 21
......
Recommend!! Get the Full 312-50v11 dumps in VCE and PDF From 2passeasy, Welcome to Download: https://www.2passeasy.com/dumps/312-50v11/ (New 254 Q&As Version)