2026 New 312-50v11 Exam Dumps with PDF and VCE Free: https://www.2passeasy.com/dumps/312-50v11/
Act now and download your EC-Council 312-50v11 test today! Do not waste time for the worthless EC-Council 312-50v11 tutorials. Download Up to date EC-Council Certified Ethical Hacker Exam (CEH v11) exam with real questions and answers and begin to learn EC-Council 312-50v11 with a classic professional.
EC-Council 312-50v11 Free Dumps Questions Online, Read and Test Now.
NEW QUESTION 1
You have successfully logged on a Linux system. You want to now cover your trade Your login attempt may be logged on several files located in /var/log. Which file does NOT belongs to the list:
- A. user.log
- B. auth.fesg
- C. wtmp
- D. btmp
Answer: C
NEW QUESTION 2
What does the following command in netcat do? nc -l -u -p55555 < /etc/passwd
- A. logs the incoming connections to /etc/passwd file
- B. loads the /etc/passwd file to the UDP port 55555
- C. grabs the /etc/passwd file when connected to UDP port 55555
- D. deletes the /etc/passwd file when connected to the UDP port 55555
Answer: C
NEW QUESTION 3
Vlady works in a fishing company where the majority of the employees have very little understanding of IT let alone IT Security. Several information security issues that Vlady often found includes, employees sharing password, writing his/her password on a post it note and stick it to his/her desk, leaving the computer unlocked, didn’t log out from emails or other social media accounts, and etc.
After discussing with his boss, Vlady decided to make some changes to improve the security environment in his company. The first thing that Vlady wanted to do is to make the employees understand the importance of keeping confidential information, such as password, a secret and they should not share it with other persons.
Which of the following steps should be the first thing that Vlady should do to make the employees in his company understand to importance of keeping confidential information a secret?
- A. Warning to those who write password on a post it note and put it on his/her desk
- B. Developing a strict information security policy
- C. Information security awareness training
- D. Conducting a one to one discussion with the other employees about the importance of information security
Answer: A
NEW QUESTION 4
Which type of security feature stops vehicles from crashing through the doors of a building?
- A. Bollards
- B. Receptionist
- C. Mantrap
- D. Turnstile
Answer: A
NEW QUESTION 5
During a black-box pen test you attempt to pass IRC traffic over port 80/TCP from a compromised web enabled host. The traffic gets blocked; however, outbound HTTP traffic is unimpeded. What type of firewall is inspecting outbound traffic?
- A. Circuit
- B. Stateful
- C. Application
- D. Packet Filtering
Answer: B
NEW QUESTION 6
Which system consists of a publicly available set of databases that contain domain name registration contact information?
- A. WHOIS
- B. CAPTCHA
- C. IANA
- D. IETF
Answer: A
NEW QUESTION 7
Which of the following incident handling process phases is responsible for defining rules, collaborating human workforce, creating a back-up plan, and testing the plans for an organization?
- A. Preparation phase
- B. Containment phase
- C. Identification phase
- D. Recovery phase
Answer: A
NEW QUESTION 8
The following is an entry captured by a network IDS. You are assigned the task of analyzing this entry. You notice the value 0x90, which is the most common NOOP instruction for the Intel processor. You figure that the attacker is attempting a buffer overflow attack.
You also notice "/bin/sh" in the ASCII part of the output. As an analyst what would you conclude about the attack?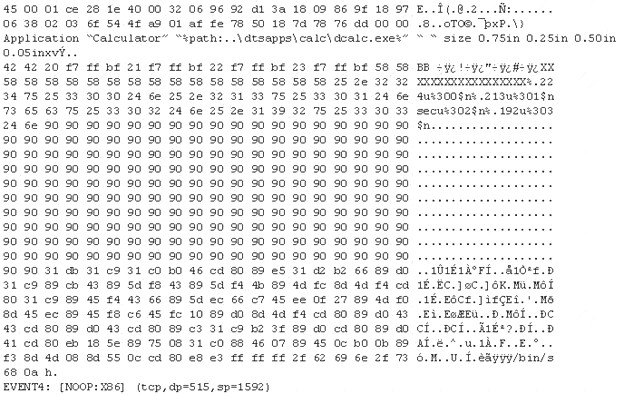
- A. The buffer overflow attack has been neutralized by the IDS
- B. The attacker is creating a directory on the compromised machine
- C. The attacker is attempting a buffer overflow attack and has succeeded
- D. The attacker is attempting an exploit that launches a command-line shell
Answer: D
NEW QUESTION 9
What does the –oX flag do in an Nmap scan?
- A. Perform an eXpress scan
- B. Output the results in truncated format to the screen
- C. Output the results in XML format to a file
- D. Perform an Xmas scan
Answer: C
NEW QUESTION 10
Why should the security analyst disable/remove unnecessary ISAPI filters?
- A. To defend against social engineering attacks
- B. To defend against webserver attacks
- C. To defend against jailbreaking
- D. To defend against wireless attacks
Answer: B
NEW QUESTION 11
You work for Acme Corporation as Sales Manager. The company has tight network security restrictions. You are trying to steal data from the company's Sales database (Sales.xls) and transfer them to your home computer. Your company filters and monitors traffic that leaves from the internal network to the Internet. How will you achieve this without raising suspicion?
- A. Encrypt the Sales.xls using PGP and e-mail it to your personal gmail account
- B. Package the Sales.xls using Trojan wrappers and telnet them back your home computer
- C. You can conceal the Sales.xls database in another file like photo.jpg or other files and send it out in an innocent looking email or file transfer using Steganography techniques
- D. Change the extension of Sales.xls to sales.txt and upload them as attachment to your hotmail account
Answer: C
NEW QUESTION 12
Which of the following tools can be used for passive OS fingerprinting?
- A. nmap
- B. tcpdump
- C. tracert
- D. ping
Answer: B
NEW QUESTION 13
What two conditions must a digital signature meet?
- A. Has to be the same number of characters as a physical signature and must be unique.
- B. Has to be unforgeable, and has to be authentic.
- C. Must be unique and have special characters.
- D. Has to be legible and neat.
Answer: B
NEW QUESTION 14
Matthew, a black hat, has managed to open a meterpreter session to one of the kiosk machines in Evil Corp’s lobby. He checks his current SID, which is S-1-5-21-1223352397-1872883824-861252104-501. What needs to happen before Matthew has full administrator access?
- A. He must perform privilege escalation.
- B. He needs to disable antivirus protection.
- C. He needs to gain physical access.
- D. He already has admin privileges, as shown by the “501” at the end of the SID.
Answer: A
NEW QUESTION 15
Which of the following Linux commands will resolve a domain name into IP address?
- A. >host-t a hackeddomain.com
- B. >host-t ns hackeddomain.com
- C. >host -t soa hackeddomain.com
- D. >host -t AXFR hackeddomain.com
Answer: A
NEW QUESTION 16
Study the following log extract and identify the attack.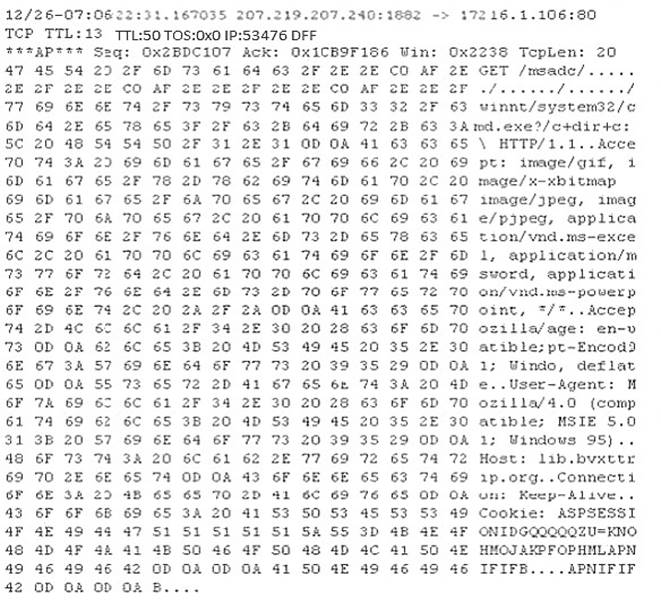
- A. Hexcode Attack
- B. Cross Site Scripting
- C. Multiple Domain Traversal Attack
- D. Unicode Directory Traversal Attack
Answer: D
NEW QUESTION 17
What is the purpose of DNS AAAA record?
- A. Authorization, Authentication and Auditing record
- B. Address prefix record
- C. Address database record
- D. IPv6 address resolution record
Answer: D
NEW QUESTION 18
An Intrusion Detection System (IDS) has alerted the network administrator to a possibly malicious sequence of packets sent to a Web server in the network’s external DMZ. The packet traffic was captured by the IDS and saved to a PCAP file. What type of network tool can be used to determine if these packets are genuinely malicious or simply a false positive?
- A. Protocol analyzer
- B. Network sniffer
- C. Intrusion Prevention System (IPS)
- D. Vulnerability scanner
Answer: A
NEW QUESTION 19
Tremp is an IT Security Manager, and he is planning to deploy an IDS in his small company. He is looking for an IDS with the following characteristics: - Verifies success or failure of an attack - Monitors system activities Detects attacks that a network-based IDS fails to detect - Near real-time detection and response - Does not require additional hardware - Lower entry cost Which type of IDS is best suited for Tremp's requirements?
- A. Gateway-based IDS
- B. Network-based IDS
- C. Host-based IDS
- D. Open source-based
Answer: C
NEW QUESTION 20
As a securing consultant, what are some of the things you would recommend to a company to ensure DNS security?
- A. Use the same machines for DNS and other applications
- B. Harden DNS servers
- C. Use split-horizon operation for DNS servers
- D. Restrict Zone transfers
- E. Have subnet diversity between DNS servers
Answer: BCDE
NEW QUESTION 21
......
Recommend!! Get the Full 312-50v11 dumps in VCE and PDF From Certshared, Welcome to Download: https://www.certshared.com/exam/312-50v11/ (New 254 Q&As Version)