2026 New 350-701 Exam Dumps with PDF and VCE Free: https://www.2passeasy.com/dumps/350-701/
Want to know Passleader 350-701 Exam practice test features? Want to lear more about Cisco Implementing and Operating Cisco Security Core Technologies certification experience? Study Real Cisco 350-701 answers to Up to the minute 350-701 questions at Passleader. Gat a success with an absolute guarantee to pass Cisco 350-701 (Implementing and Operating Cisco Security Core Technologies) test on your first attempt.
Free demo questions for Cisco 350-701 Exam Dumps Below:
NEW QUESTION 1
Which two application layer preprocessors are used by Firepower Next Generation Intrusion Prevention System? (Choose two.)
- A. SIP
- B. inline normalization
- C. SSL
- D. packet decoder
- E. modbus
Answer: AC
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/security/firepower/60/configuration/guide/fpmc-config-guide-v60/Application_Layer_Preprocessors.html
NEW QUESTION 2
In which form of attack is alternate encoding, such as hexadecimal representation, most often observed?
- A. smurf
- B. distributed denial of service
- C. cross-site scripting
- D. rootkit exploit
Answer: C
NEW QUESTION 3
Which two features are used to configure Cisco ESA with a multilayer approach to fight viruses and malware? (Choose two.)
- A. Sophos engine
- B. white list
- C. RAT
- D. outbreak filters
- E. DLP
Answer: AD
NEW QUESTION 4
What is the purpose of the Decrypt for Application Detection feature within the WSA Decryption options?
- A. It decrypts HTTPS application traffic for unauthenticated users.
- B. It alerts users when the WSA decrypts their traffic.
- C. It decrypts HTTPS application traffic for authenticated users.
- D. It provides enhanced HTTPS application detection for AsyncOS.
Answer: D
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/security/wsa/wsa11-7/user_guide/b_WSA_UserGuide_11_7/b_WSA_UserGuide_11_7_chapter_01011.html
NEW QUESTION 5
Which two probes are configured to gather attributes of connected endpoints using Cisco Identity Services Engine? (Choose two.)
- A. RADIUS
- B. TACACS+
- C. DHCP
- D. sFlow
- E. SMTP
Answer: AC
Explanation:
Reference: https://www.cisco.com/en/US/docs/security/ise/1.0/user_guide/ise10_prof_pol.html
NEW QUESTION 6
Refer to the exhibit.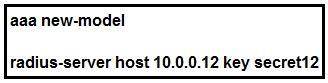
Which statement about the authentication protocol used in the configuration is true?
- A. The authentication request contains only a password
- B. The authentication request contains only a username
- C. The authentication and authorization requests are grouped in a single packet.
- D. There are separate authentication and authorization request packets.
Answer: C
NEW QUESTION 7
DRAG DROP
Drag and drop the Firepower Next Generation Intrustion Prevention System detectors from the left onto the correct definitions on the right.
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/security/firepower/640/configuration/guide/fpmc-config-guide-v64/detecting_specific_threats.html
NEW QUESTION 8
The Cisco ASA must support TLS proxy for encrypted Cisco Unified Communications traffic. Where must the ASA be added on the Cisco UC Manager platform?
- A. Certificate Trust List
- B. Endpoint Trust List
- C. Enterprise Proxy Service
- D. Secured Collaboration Proxy
Answer: A
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/security/asa/special/unified-communications/guide/unified-comm/unified-comm-tlsproxy.html
NEW QUESTION 9
Which two capabilities does TAXII support? (Choose two.)
- A. exchange
- B. pull messaging
- C. binding
- D. correlation
- E. mitigating
Answer: BC
NEW QUESTION 10
Which two conditions are prerequisites for stateful failover for IPsec? (Choose two.)
- A. Only the IKE configuration that is set up on the active device must be duplicated on the standby device; the IPsec configuration is copied automatically.
- B. The active and standby devices can run different versions of the Cisco IOS software but must be the same type of device.
- C. The IPsec configuration that is set up on the active device must be duplicated on the standby device.
- D. Only the IPsec configuration that is set up on the active device must be duplicated on the standby device; the IKE configuration is copied automatically.
- E. The active and standby devices must run the same version of the Cisco IOS software and must be the same type of device.
Answer: BC
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/ios-xml/ios/sec_conn_vpnav/configuration/15-mt/sec-vpn-availability-15-mt-book/sec-state-fail-ipsec.html
NEW QUESTION 11
Which two preventive measures are used to control cross-site scripting? (Choose two.)
- A. Enable client-side scripts on a per-domain basis.
- B. Incorporate contextual output encoding/escaping.
- C. Disable cookie inspection in the HTML inspection engine.
- D. Run untrusted HTML input through an HTML sanitization engine.
- E. SameSite cookie attribute should not be used.
Answer: AB
NEW QUESTION 12
An engineer must force an endpoint to re-authenticate an already authenticated session without disrupting the endpoint to apply a new or updated policy from ISE. Which CoA type achieves this goal?
- A. Port Bounce
- B. CoA Terminate
- C. CoA Reauth
- D. CoA Session Query
Answer: C
NEW QUESTION 13
Which ASA deployment mode can provide separation of management on a shared appliance?
- A. DMZ multiple zone mode
- B. transparent firewall mode
- C. multiple context mode
- D. routed mode
Answer: C
NEW QUESTION 14
An administrator wants to ensure that all endpoints are compliant before users are allowed access on the corporate network. The endpoints must have the corporate antivirus application installed and be running the latest build of Windows 10. What must the administrator implement to ensure that all devices are compliant before they are allowed on the network?
- A. Cisco Identity Services Engine and AnyConnect Posture module
- B. Cisco Stealthwatch and Cisco Identity Services Engine integration
- C. Cisco ASA firewall with Dynamic Access Policies configured
- D. Cisco Identity Services Engine with PxGrid services enabled
Answer: A
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/security/vpn_client/anyconnect/anyconnect46/administration/guide/b_AnyConnect_Administrator_Guide_4-6/configure-posture.html
NEW QUESTION 15
Where are individual sites specified to be blacklisted in Cisco Umbrella?
- A. application settings
- B. content categories
- C. security settings
- D. destination lists
Answer: D
NEW QUESTION 16
Which Talos reputation center allows you to track the reputation of IP addresses for email and web traffic?
- A. IP Blacklist Center
- B. File Reputation Center
- C. AMP Reputation Center
- D. IP and Domain Reputation Center
Answer: D
NEW QUESTION 17
Which two kinds of attacks are prevented by multifactor authentication? (Choose two.)
- A. phishing
- B. brute force
- C. man-in-the-middle
- D. DDOS
- E. tear drop
Answer: BC
NEW QUESTION 18
DRAG DROP
Drag and drop the capabilities from the left onto the correct technologies on the right.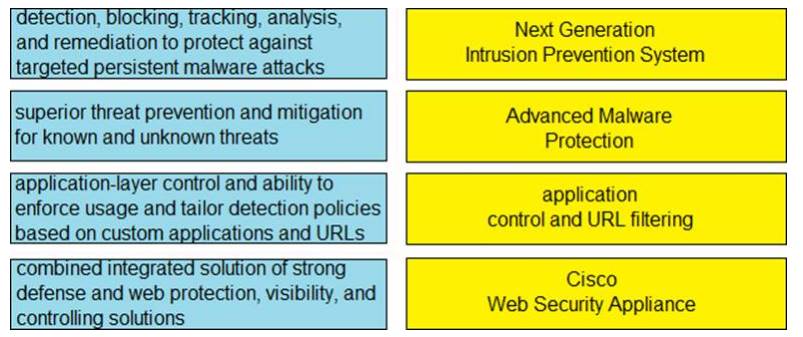
- A. Mastered
- B. Not Mastered
Answer: A
Explanation: 
NEW QUESTION 19
Which functions of an SDN architecture require southbound APIs to enable communication?
- A. SDN controller and the network elements
- B. management console and the SDN controller
- C. management console and the cloud
- D. SDN controller and the cloud
Answer: A
NEW QUESTION 20
Which cloud service model offers an environment for cloud consumers to develop and deploy applications without needing to manage or maintain the underlying cloud infrastructure?
- A. PaaS
- B. XaaS
- C. IaaS
- D. SaaS
Answer: A
NEW QUESTION 21
Which policy represents a shared set of features or parameters that define the aspects of a managed device that are likely to be similar to other managed devices in a deployment?
- A. group policy
- B. access control policy
- C. device management policy
- D. platform service policy
Answer: D
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/security/firepower/622/configuration/guide/fpmc-config-guide-v622/platform_settings_policies_for_managed_devices.pdf
NEW QUESTION 22
What provides visibility and awareness into what is currently occurring on the network?
- A. CMX
- B. WMI
- C. Prime Infrastructure
- D. Telemetry
Answer: C
NEW QUESTION 23
Refer to the exhibit.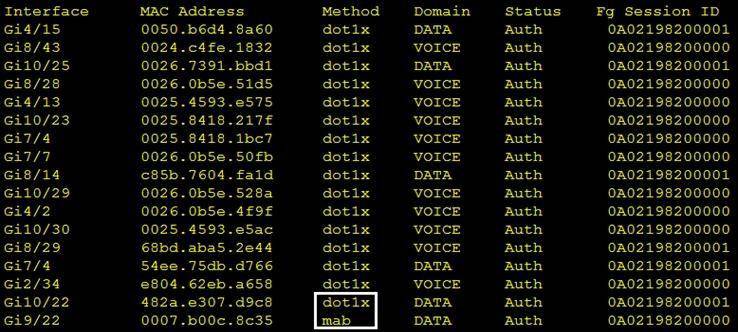
Which command was used to generate this output and to show which ports are authenticating with dot1x or mab?
- A. show authentication registrations
- B. show authentication method
- C. show dot1x all
- D. show authentication sessions
Answer: B
NEW QUESTION 24
......
P.S. Easily pass 350-701 Exam with 102 Q&As Surepassexam Dumps & pdf Version, Welcome to Download the Newest Surepassexam 350-701 Dumps: https://www.surepassexam.com/350-701-exam-dumps.html (102 New Questions)