2026 New 350-701 Exam Dumps with PDF and VCE Free: https://www.2passeasy.com/dumps/350-701/
we provide Realistic Cisco 350-701 rapidshare which are the best for clearing 350-701 test, and to get certified by Cisco Implementing and Operating Cisco Security Core Technologies. The 350-701 Questions & Answers covers all the knowledge points of the real 350-701 exam. Crack your Cisco 350-701 Exam with latest dumps, guaranteed!
Online 350-701 free questions and answers of New Version:
NEW QUESTION 1
Which two conditions are prerequisites for stateful failover for IPsec? (Choose two.)
- A. Only the IKE configuration that is set up on the active device must be duplicated on the standby device; the IPsec configuration is copied automatically.
- B. The active and standby devices can run different versions of the Cisco IOS software but must be the same type of device.
- C. The IPsec configuration that is set up on the active device must be duplicated on the standby device.
- D. Only the IPsec configuration that is set up on the active device must be duplicated on the standby device; the IKE configuration is copied automatically.
- E. The active and standby devices must run the same version of the Cisco IOS software and must be the same type of device.
Answer: BC
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/ios-xml/ios/sec_conn_vpnav/configuration/15-mt/sec-vpn-availability-15-mt-book/sec-state-fail-ipsec.html
NEW QUESTION 2
Refer to the exhibit.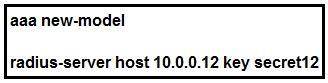
Which statement about the authentication protocol used in the configuration is true?
- A. The authentication request contains only a password
- B. The authentication request contains only a username
- C. The authentication and authorization requests are grouped in a single packet.
- D. There are separate authentication and authorization request packets.
Answer: C
NEW QUESTION 3
Which policy represents a shared set of features or parameters that define the aspects of a managed device that are likely to be similar to other managed devices in a deployment?
- A. group policy
- B. access control policy
- C. device management policy
- D. platform service policy
Answer: D
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/security/firepower/622/configuration/guide/fpmc-config-guide-v622/platform_settings_policies_for_managed_devices.pdf
NEW QUESTION 4
Which two services must remain as on-premises equipment when a hybrid email solution is deployed? (Choose two.)
- A. DDoS
- B. antispam
- C. antivirus
- D. encryption
- E. DLP
Answer: DE
Explanation:
Reference: https://www.cisco.com/c/dam/en/us/td/docs/security/ces/overview_guide/Cisco_Cloud_Hybrid_Email_Security_Overview_Guide.pdf
NEW QUESTION 5
Which two application layer preprocessors are used by Firepower Next Generation Intrusion Prevention System? (Choose two.)
- A. SIP
- B. inline normalization
- C. SSL
- D. packet decoder
- E. modbus
Answer: AC
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/security/firepower/60/configuration/guide/fpmc-config-guide-v60/Application_Layer_Preprocessors.html
NEW QUESTION 6
Which two behavioral patterns characterize a ping of death attack? (Choose two.)
- A. The attack is fragmented into groups of 16 octets before transmission.
- B. The attack is fragmented into groups of 8 octets before transmission.
- C. Short synchronized bursts of traffic are used to disrupt TCP connections.
- D. Malformed packets are used to crash systems.
- E. Publicly accessible DNS servers are typically used to execute the attack.
Answer: BD
Explanation:
Reference: https://en.wikipedia.org/wiki/Ping_of_death
NEW QUESTION 7
An engineer configured a new network identity in Cisco Umbrella but must verify that traffic is being routed through the Cisco Umbrella network. Which action tests the routing?
- A. Ensure that the client computers are pointing to the on-premises DNS servers.
- B. Enable the Intelligent Proxy to validate that traffic is being routed correctly.
- C. Add the public IP address that the client computers are behind to a Core Identity.
- D. Browse to http://welcome.umbrella.com/ to validate that the new identity is working.
Answer: B
NEW QUESTION 8
In which form of attack is alternate encoding, such as hexadecimal representation, most often observed?
- A. smurf
- B. distributed denial of service
- C. cross-site scripting
- D. rootkit exploit
Answer: C
NEW QUESTION 9
Which two deployment model configurations are supported for Cisco FTDv in AWS? (Choose two.)
- A. Cisco FTDv configured in routed mode and managed by an FMCv installed in AWS
- B. Cisco FTDv with one management interface and two traffic interfaces configured
- C. Cisco FTDv configured in routed mode and managed by a physical FMC appliance on premises
- D. Cisco FTDv with two management interfaces and one traffic interface configured
- E. Cisco FTDv configured in routed mode and IPv6 configured
Answer: AC
Explanation:
Reference: https://www.cisco.com/c/en/us/products/collateral/security/adaptive-security-virtual-appliance-asav/white-paper-c11-740505.html
NEW QUESTION 10
Which feature is supported when deploying Cisco ASAv within AWS public cloud?
- A. multiple context mode
- B. user deployment of Layer 3 networks
- C. IPv6
- D. clustering
Answer: B
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/security/asa/asa96/asav/quick-start-book/asav-96-qsg/asav-aws.html
NEW QUESTION 11
Refer to the exhibit.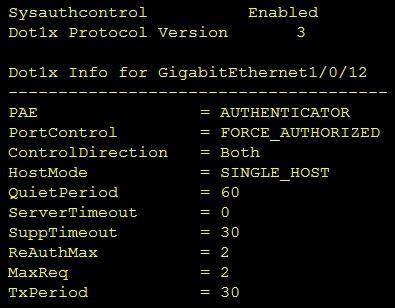
Which command was used to display this output?
- A. show dot1x all
- B. show dot1x
- C. show dot1x all summary
- D. show dot1x interface gi1/0/12
Answer: A
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/ios-xml/ios/sec_usr_8021x/configuration/xe-3se/3850/sec-user-8021x-xe-3se-3850-book/config-ieee-802x-pba.html
NEW QUESTION 12
An engineer used a posture check on a Microsoft Windows endpoint and discovered that the MS17-010 patch was not installed, which left the endpoint vulnerable to WannaCry ransomware. Which two solutions mitigate the risk of this ransomware infection? (Choose two.)
- A. Configure a posture policy in Cisco Identity Services Engine to install the MS17-010 patch before allowing access on the network.
- B. Set up a profiling policy in Cisco Identity Service Engine to check and endpoint patch level before allowing access on the network.
- C. Configure a posture policy in Cisco Identity Services Engine to check that an endpoint patch level is met before allowing access on the network.
- D. Configure endpoint firewall policies to stop the exploit traffic from being allowed to run and replicate throughout the network.
- E. Set up a well-defined endpoint patching strategy to ensure that endpoints have critical vulnerabilities patched in a timely fashion.
Answer: AC
NEW QUESTION 13
Which deployment model is the most secure when considering risks to cloud adoption?
- A. public cloud
- B. hybrid cloud
- C. community cloud
- D. private cloud
Answer: D
NEW QUESTION 14
Which two kinds of attacks are prevented by multifactor authentication? (Choose two.)
- A. phishing
- B. brute force
- C. man-in-the-middle
- D. DDOS
- E. tear drop
Answer: BC
NEW QUESTION 15
An engineer is configuring a Cisco ESA and wants to control whether to accept or reject email messages to a recipient address. Which list contains the allowed recipient addresses?
- A. SAT
- B. BAT
- C. HAT
- D. RAT
Answer: D
NEW QUESTION 16
How is Cisco Umbrella configured to log only security events?
- A. per policy
- B. in the Reporting settings
- C. in the Security Settings section
- D. per network in the Deployments section
Answer: A
Explanation:
Reference: https://docs.umbrella.com/deployment-umbrella/docs/log-management
NEW QUESTION 17
Which two request of REST API are valid on the Cisco ASA Platform? (Choose two.)
- A. put
- B. options
- C. get
- D. push
- E. connect
Answer: AC
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/security/asa/api/qsg-asa-api.html
NEW QUESTION 18
......
Thanks for reading the newest 350-701 exam dumps! We recommend you to try the PREMIUM Dumps-hub.com 350-701 dumps in VCE and PDF here: https://www.dumps-hub.com/350-701-dumps.html (337 Q&As Dumps)