2026 New 70-412 Exam Dumps with PDF and VCE Free: https://www.2passeasy.com/dumps/70-412/
Cause all that matters here is passing exam with microsoft 70 412. Cause all that you need is a high score of mcsa 70 412. The only one thing you need to do is downloading 70 412 dumps free now. We will not let you down with our money-back guarantee.
Online Microsoft 70-412 free dumps demo Below:
NEW QUESTION 1
Your network contains an Active Directory domain named contoso.com. The domain contains an IP Address Management (IPAM) server that uses a Windows Internal Database.
You install a Microsoft SQL Server 2012 instance on a new server. You need to migrate the IPAM database to the SQL Server instance. Which cmdlet should you run?
- A. Disable-IpamCapability
- B. Set-IpamConfiguration
- C. Update-IpamServer
- D. Move-IpamDatabase
Answer: D
Explanation: The Move-IpamDatabase cmdlet migrates the IP Address Management (IPAM) database to a Microsoft SQL Server database. You can migrate from Windows Internal Database (WID) or from a SQL Server database. The cmdlet creates a new IPAM schema and copies all data from the existing IPAM database. After the cmdlet completes copying data, it changes IPAM configuration settings to refer to the new database as the IPAM database.
Reference: Move-IpamDatabase
NEW QUESTION 2
Your network contains two Active Directory forests named contoso.com and adatum.com. All of the domain controllers in both of the forests run Windows Server 2012 R2. The adatum.com domain contains a file server named Servers.
Adatum.com has a one-way forest trust to contoso.com.
A contoso.com user name User10 attempts to access a shared folder on Servers and receives the error message shown in the exhibit. (Click the Exhibit button.)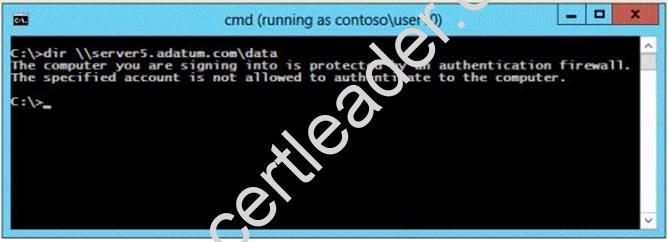
You verify that the Authenticated Users group has Read permissions to the Data folder. You need to ensure that User10 can read the contents of the Data folder on Server5 in the
adatum.com domain. What should you do?
- A. Grant the Other Organization group Read permissions to the Data folder.
- B. Modify the list of logon workstations of the contosoUser10 user account.
- C. Enable the Netlogon Service (NP-In) firewall rule on Server5.
- D. Modify the permissions on the Server5 computer object in Active Directory.
Answer: D
Explanation: * To resolve the issue, I had to open up AD Users and Computers --> enable Advanced Features --> Select the Computer Object --> Properties --> Security --> Add the Group I want to allow access to the computer (in this case, DomainADomain users) and allow "Allowed to Authenticate". Once I did that, everything worked:
* For users in a trusted Windows Server 2008 or Windows Server 2003 domain or forest to be able to access resources in a trusting Windows Server 2008 or Windows Server 2003 domain or forest where the trust authentication setting has been set to selective authentication, each user must be explicitly granted the Allowed to Authenticate permission on the security descriptor of the computer objects (resource computers) that reside in the
trusting domain or forest.
Reference: Grant the Allowed to Authenticate Permission on Computers in the Trusting Domain or Forest.
http://technet.microsoft.com/en-us/library/cc816733(v=ws.10).aspx
NEW QUESTION 3
You are considering adding a child domain to the dandenong.melbourne.victoria. australia.contoso.com domain tree.
Which of the following represents the maximum length in characters, including periods, of an Active Directory domain name?
- A. 64 characters
- B. 128 characters
- C. 256 characters
- D. 512 characters
Answer: A
NEW QUESTION 4
You have a server named LON-DC1 that runs Windows Server 2012 R2. An iSCSI virtual disk named VirtualiSCSI1.vhd exists on LON-DC1 as shown in the exhibit. (Click the Exhibit button.)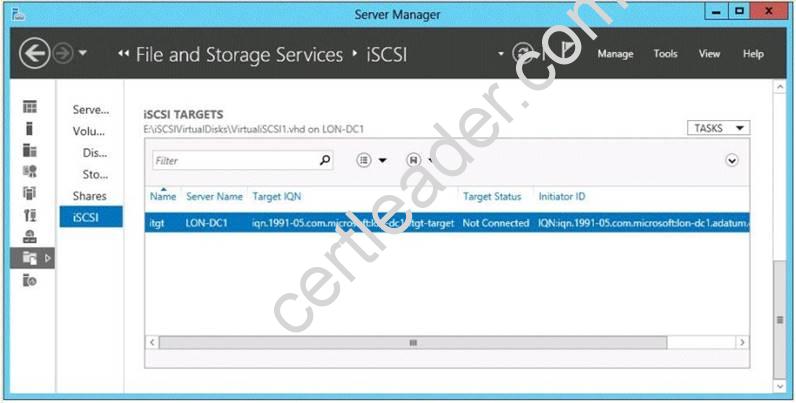
You create a new iSCSI virtual disk named VirtualiSCSI2.vhd by using the existing itgt iSCSI target.
VirtualiSCSIl.vhd is removed from LON-DC1.
You need to assign VirtualiSCSI2.vhd a logical unit value of 0. What should you do?
- A. Modify the properties of the itgt ISCSI target.
- B. Modify the properties of the VirtualiSCSI2.vhd iSCSI virtual disk.
- C. Run the Set-VirtualDisk cmdlet and specify the -Uniqueld parameter.
- D. Run the iscsicli command and specify the reportluns parameter.
Answer: B
Explanation: The virtual disk has the option to change the lun ID, no other option available in the answers appear to allow this change.
Note: Logical unit numbers (LUNs) created on an iSCSI disk storage subsystem are not directly assigned to aserver. For iSCSI, LUNs are assigned to logical entities called targets.
NEW QUESTION 5
DRAG DROP
Your network contains an Active Directory domain named adatum.com. The domain contains three servers. The servers are configured as shown in the following table.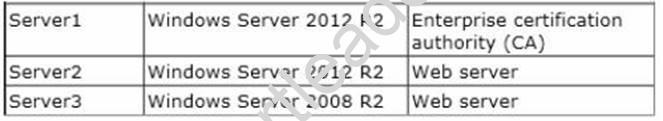
Server1 is configured as shown in the exhibit. (Click the Exhibit button.)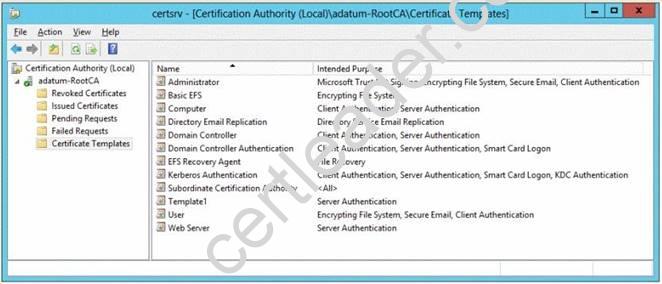
Template1 contains custom cryptography settings that are required by the corporate security team.
On Server2, an administrator successfully installs a certificate based on Template1.
The administrator reports that Template1 is not listed in the Certificate Enrollment wizard on Server3, even after selecting the Show all templates check box.
You need to ensure that you can install a server authentication certificate on Server3. The certificate must comply with the cryptography requirements.
Which three actions should you perform in sequence?
To answer, move the appropriate three actions from the list of actions to the answer area and arrange them in the correct order.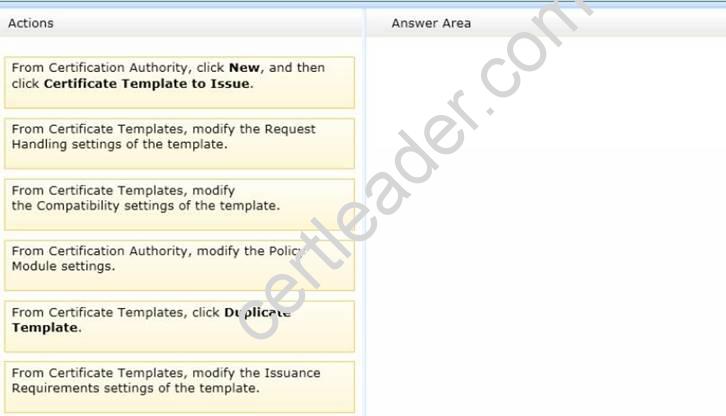
Answer:
Explanation: Note:
Duplicate an existing template, modify the Compatibility Settings (to Windows Server 2008), and modify the Request Handling settings.
NEW QUESTION 6
Your network contains an Active Directory domain named adatum.com. The domain contains two sites named Site1 and Site2 and two domain controllers named DC1 and DC2. DC1 is located in Site1 and DC2 is located in Site2.
You install an additional domain controller named DC3 in Site1 and you ship DC3 to Site2. A technician connects DC3 to Site2.
You discover that users in Site2 are authenticated only by DC2.
You need to ensure that the users in Site2 are authenticated by both DC2 and DC3. What should you do?
- A. In Active Directory Users and Computers, configure the msDS-PrimaryComputer attribute for DC3.
- B. In Active Directory Users and Computers, configure the msDS-Site-Affinity attribute for DC3.
- C. From Active Directory Sites and Services, move DC3.
- D. From Active Directory Sites and Services, modify the site link between Site1 and Site2.
Answer: C
Explanation: DC3 needs to be moved to Site2 in AD DS Reference: Move a domain controller between sites
http://technet.microsoft.com/en-us/library/cc759326(v=ws.10).aspx
NEW QUESTION 7
HOTSPOT
Your network contains one Active Directory forest named adatum.com. The forest contains a single domain.
The site topology for the forest is shown in the exhibit. Each site contain s one domain controller.
You need to ensure that replication between site2 and site4 occurs in 15 minutes or less.
What command should you run? To answer select the appropriate options in the answer area.
Answer Area
Answer:
Explanation: (Specifically look up - ReplicationFrequencyinMinutes) https://technet.microsoft.com/en-us/%5Clibrary/Hh852257(v=WPS.630).aspx
NEW QUESTION 8
Your network contains an Active Directory domain named contoso.com. The domain contains a file server named Server1 that runs Windows Server 2012 R2. All client computers run Windows 8.
You need to configure a custom Access Denied message that will be displayed to users when they are denied access to folders or files on Server1.
What should you configure?
- A. A classification property
- B. The File Server Resource Manager Options
- C. A file management task
- D. A file screen template
Answer: B
Explanation: Access-denied assistance can be configured by using the File Server Resource Manager console on the file server.
Note: Access-denied assistance is a new feature in Windows Server 2012, which provides the following ways to troubleshoot issues that are related to access to files and folders:
* Self-assistance. If a user can determine the issue and remediate the problem so that they can get the requested access, the impact to the business is low, and no special exceptions are needed in the central access policy. Access-denied assistance provides an access- denied message that file server administrators can customize with information specific to their organizations. For example, an administrator could set the message so that users can request access from a data owner without involving the file server administrator.
Reference: Scenario: Access-Denied Assistance
NEW QUESTION 9
Your company has a main office and a branch office.
The main office contains a file server named Server1. Server1 has the BranchCache for Network Files role service installed. The branch office contains a server named Server2. Server2 is configured as a BranchCache hosted cache server.
You need to preload the data from the file shares on Server1 to the cache on Server2. What should you run first?
- A. Publish-BCFileContent
- B. Add- BCDataCacheExtension
- C. Set-BCCache
- D. Export-BCCachePackage
Answer: A
Explanation: See step 2 below.
To prehash content and preload the content on hosted cache servers
✑ Log on to the file or Web server that contains the data that you wish to preload, and identify the folders and files that you wish to load on one or more remote hosted cache servers.
✑ Run Windows PowerShell as an Administrator. For each folder and file, run either the Publish-BCFileContent command or the Publish-BCWebContent command, depending on the type of content server, to trigger hash generation and to add data to a data package.
✑ After all the data has been added to the data package, export it by using the Export-BCCachePackage command to produce a data package file.
✑ Move the data package file to the remote hosted cache servers by using your choice of file transfer technology. FTP, SMB, HTTP, DVD and portable hard disks are all viable transports.
✑ Import the data package file on the remote hosted cache servers by using the Import-BCCachePackage command.
Reference: Prehashing and Preloading Content on Hosted Cache Servers (Optional)
NEW QUESTION 10
HOTSPOT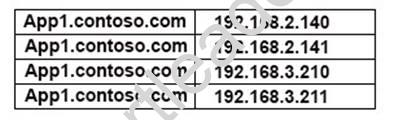
You discover that when users connect to app1.contoso.com, they are connected frequently to a server that is not on their local subnet.
You need to ensure that when the users connect to app1.contoso.com, they connect to a server on their local subnet. The connections must be distributed across the servers that host app1.contoso.com on their subnet.
Which options should you select?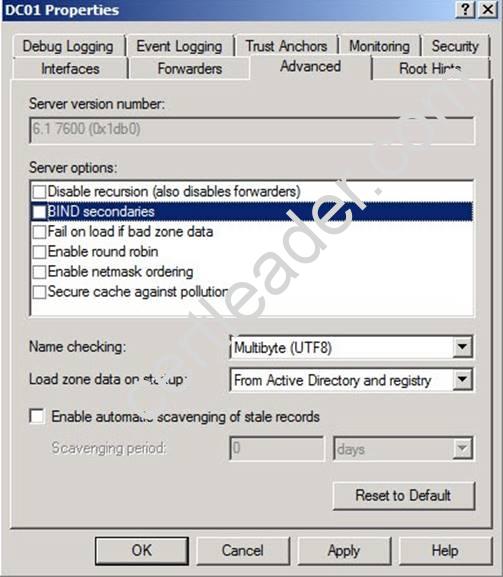
Answer:
Explanation: 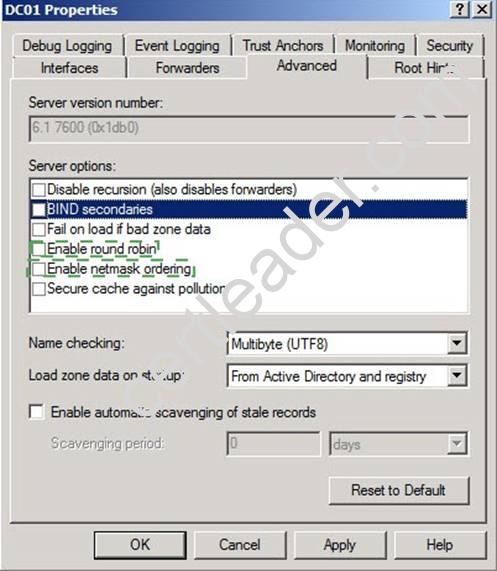
NEW QUESTION 11
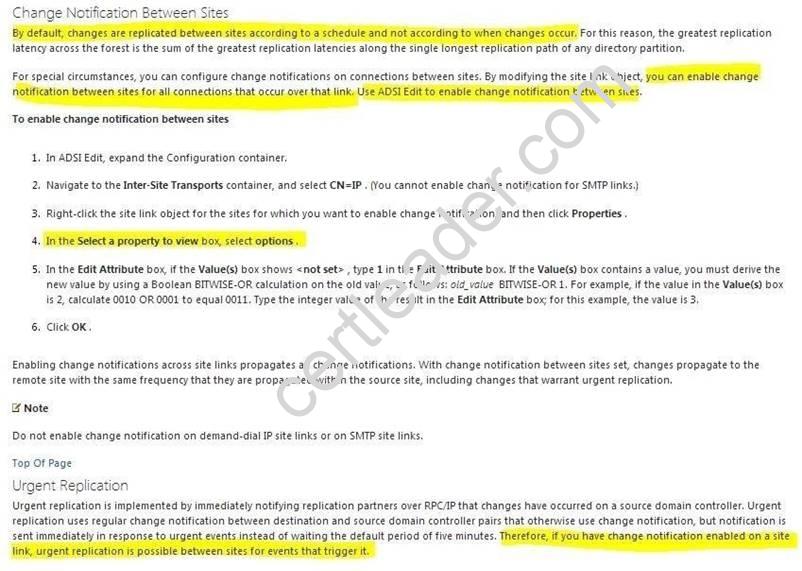
You are employed as a senior network administrator at ABC.com. ABC.com has an Active Directory domain named ABC.com.
All servers on the ABC.com network have Windows Server 2012 R2 installed.
The ABC.com domain has an Active Directory site configured in London,and an Active Directory site in New york.
You have been instructed to make sure that the synchronization of account lockout data happens quicker.
- A. You should consider editing the options attribute from WANLINK properties
- B. You should consider editing the options attribute from LANLIK properties
- C. You should consider editing the options attribute from the DEFAULTSITELINK properties
- D. You should consider editing the proxyAddressess attribute from the DEFAULTIPSITELINK properties.
Answer: C
Explanation: http://technet.microsoft.com/en-us/library/cc961787.aspx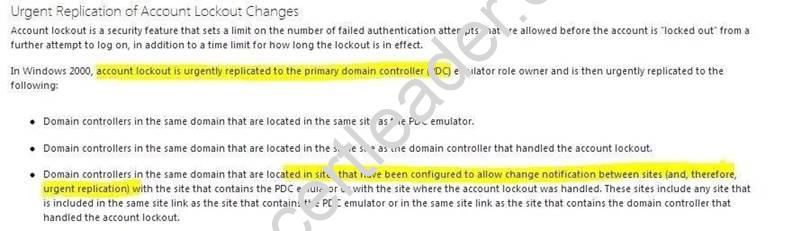
NEW QUESTION 12
HOTSPOT
Your network contains an Active Directory domain named contoso.com. The domain contains two DHCP servers named Server1 and Server2. Both servers have multiple IPv4 scopes.
Server1 and Server2 are used to assign IP addresses for the network IDs of 172.20.0.0/16 and 131.107.0.0/16.
You install the IP Address Management (IPAM) Server feature on a server named IPAM1 and configure IPAM1 to manage Server1 and Server2.
Some users from the 172.20.0.0 network report that they occasionally receive an IP address conflict error message.
You need to identify whether any scopes in the 172.20.0.0 network ID conflict with one another.
What Windows PowerShell cmdlet should you run?
To answer, select the appropriate options in the answer area.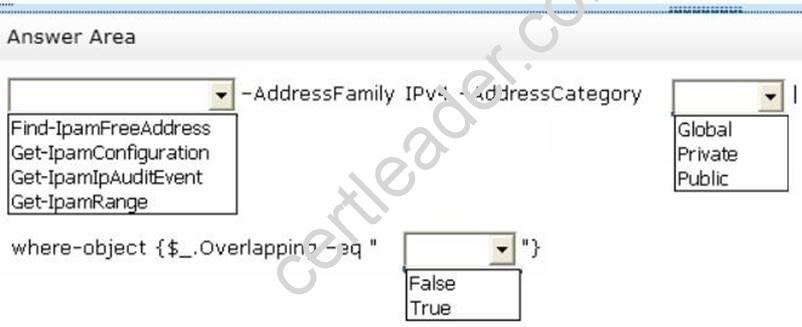
Answer:
Explanation: Type the following command at a Windows PowerShell prompt and press ENTER:
PS C:> Get-IpamRange –AddressFamily IPv4 –AddressCategory Private|where-object
{$_.Overlapping –eq “True”}
The previous command will display any overlapping IP address ranges, if they exist.
NEW QUESTION 13
HOTSPOT
Your network contains one Active Directory forest named adatum.com. The forest contains a single domain.
The forest contains the domain controllers configured as shown in the following table.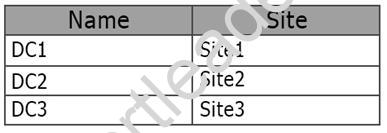
Recently, a domain controller named DC4 was deployed to adatum.com. DC4 is in the Default-First-Site-Name site.
The adatum.com site links are configured as follows.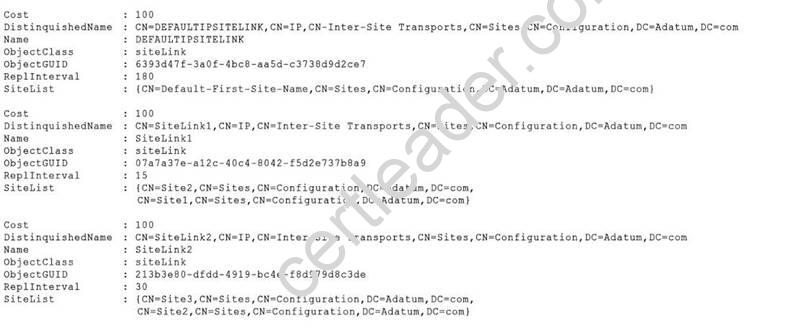
The schedule for SiteLink1 is shown in the SiteLink1 exhibit. (Click the Exhibit button.)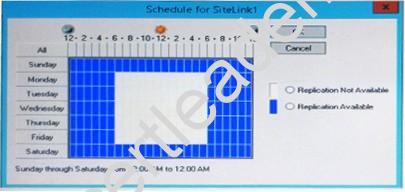
The schedule for SiteLink2 is shown in the SiteLink2 exhibit. (Click the Exhibit button.)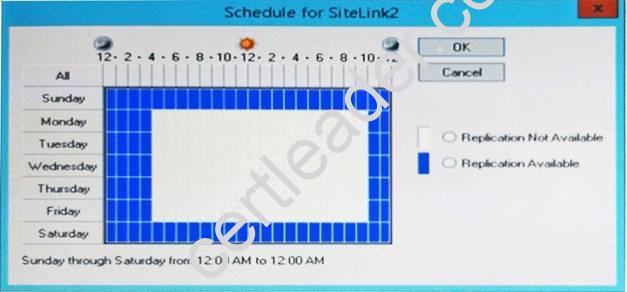
For each of the following statements, select Yes if the statement is true. Otherwise, select No.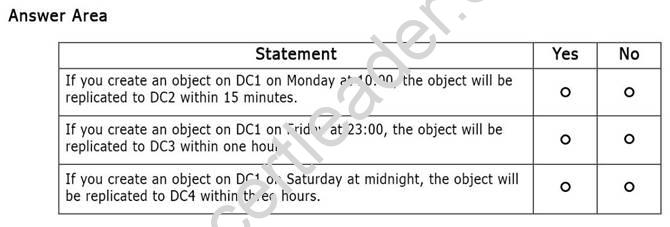
Answer:
Explanation: * SiteLink1 replication is not available at 10:00.
* SiteLink1 and SiteLink2 replication is available at Friday at 23:00. Replication intervals are 15 minutes and 30 minutes respectively.
* DefaultIPSitelink will be used to replicate an object from DC1 to DC4. The replication interval of DefaultIPSitelink is 180 minutes.
NEW QUESTION 14
Your network contains two Web servers named Server1 and Server2. Both servers run Windows Server 2012 R2.
Server1 and Server2 are nodes in a Network Load Balancing (NLB) cluster. The NLB cluster contains an application named App1 that is accessed by using the URLhttp://app1.contoso.com.
You plan to perform maintenance on Server1.
You need to ensure that all new connections to App1 are directed to Server2. The solution must not disconnect the existing connections to Server1.
What should you run?
- A. The Set-NlbCluster cmdlet
- B. The Set-NlbClusterNode cmdlet
- C. The Stop-NlbCluster cmdlet
- D. The Stop-NlbClusterNode cmdlet
Answer: D
Explanation: The Stop-NlbClusterNode cmdlet stops a node in an NLB cluster. When you use the stop the nodes in the cluster, client connections that are already in progress are interrupted. To avoid interrupting active connections, consider using the -drain parameter, which allows the node to continue servicing active connections but disables all new traffic to that node.
-Drain <SwitchParameter>
Drains existing traffic before stopping the cluster node. If this parameter is omitted, existing traffic will be dropped.
Reference: Stop-NlbClusterNode
NEW QUESTION 15
Which of the following services would you restart on a domain controller if you wanted to trigger a reregistration of the domain controller's _ldap and _kerberos SRV records?
- A. DNS Server
- B. Server
- C. Workstation
- D. Netlogon
Answer: D
NEW QUESTION 16
Your network contains an Active Directory domain named contoso.com.
The domain contains a server named Server1. Server1 runs Windows Server 2012 R2. You create a group Managed Service Account named gService1.
You need to configure a service named Service1 to run as the gService1 account. How should you configure Service1?
- A. From a command prompt, run sc.exe and specify the theconfig parameter.
- B. From the Services console, configure the General settings.
- C. From Windows PowerShell, run Set-Service and specify the -StartupType parameter.
- D. From the Services console, configure the Log On settings.
Answer: A
Explanation: Executing the sc.exe command with the config parameter will modify service configuration.
NEW QUESTION 17
You have a server named Server1 that runs Windows Server 2012 R2. Windows Server 2012 R2 is installed on volume C.
You need to ensure that Safe Mode with Command Prompt loads the next time Server1 restarts.
Which tool should you use?
- A. The Restart-Server cmdlet
- B. The Bootcfg command
- C. The Restart-Computer cmdlet
- D. The Bcdedit command
Answer: D
Explanation: How To Force Windows To Restart in Safe Mode
1. Open Advanced Startup Options in Windows 8
2. Open Command Prompt.
3. With Command Prompt open, execute the correct bcdedit command as shown below based on which Safe Mode option you'd like to start:
Safe Mode:
bcdedit /set {default} safeboot minimal
http://pcsupport.about.com/od/repair-recovery/a/force-or-stop-safe-mode-windows.htm
NEW QUESTION 18
You are employed as a network administrator at consoto.com.
Contoso.com has in an Active Directory domain named contoso.com.
All Servers on the contoso.com network have Windows Server 2012 R2 installed.
A contoso.com server ,named Server1,hosts the Active Directory Certificate Services Server role and utilizes a hardware security module(HSM) to safeguard its private key.
You have beed instructed to backup the Active Directory Certificate Services (ADCS) database,log files,and private key regularly.
You should not use a utility supplied by the hardware security module (HSM) creator. Which of the following actions should you take?
- A. You should consider scheduling an incremental backup
- B. You Should consider making use of the certutil.exe command.
- C. You should consider schedulling a differential backup
- D. You should consider schedulling a copy backup
Answer: B
Explanation: A. ADCS needs to be backup up using certutil
B. -Backup, -backupdb, -backupKey: You can use Certutil.exe to dump and display certification authority (CA) configuration information, configure Certificate Services, backup and restore CA components, and verify certificates, key pairs, and certificate chains.
C. ADCS needs to be backup up using certutil
D. ADCS needs to be backup up using certutil
http://technet.microsoft.com/library/cc732443.aspx http://technet.microsoft.com/en-us/library/cc732443.aspx#BKMK_backup http://technet.microsoft.com/en-us/library/cc732443.aspx#BKMK_backupDB http://technet.microsoft.com/en-us/library/cc732443.aspx#BKMK_backupKey
http://blogs.technet.com/b/pki/archive/2010/04/20/disaster-recovery-procedures-for-theactive-directorycertificate-services-adcs.aspx
Recommend!! Get the Full 70-412 dumps in VCE and PDF From Certleader, Welcome to Download: https://www.certleader.com/70-412-dumps.html (New 435 Q&As Version)