2026 New 70-412 Exam Dumps with PDF and VCE Free: https://www.2passeasy.com/dumps/70-412/
Your success in 70 412 vce is our sole target and we develop all our 70 412 exam in a way that facilitates the attainment of this target. Not only is our exam 70 412 material the best you can find, it is also the most detailed and the most updated. examcollection 70 412 for Microsoft 70-412 are written to the highest standards of technical accuracy.
Free demo questions for Microsoft 70-412 Exam Dumps Below:
NEW QUESTION 1
DRAG DROP
Your network contains an Active Directory domain named contoso.com. The domain contains two servers named Server1 and Server3. The network contains a standalone server named Server2.
All servers run Windows Server 2012 R2. The servers are configured as shown in the following table.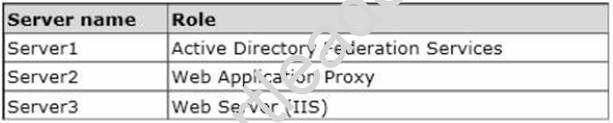
Server3 hosts an application named App1. App1 is accessible internally by using the URL https://app1.contoso.com. App1 only supports Integrated Windows authentication.
You need to ensure that all users from the Internet are pre-authenticated before they can access App1.
What should you do?
To answer, drag the appropriate servers to the correct actions. Each server may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.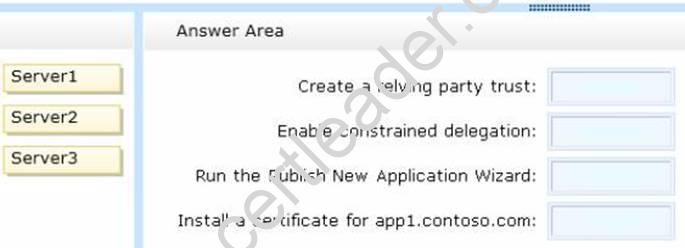
Answer:
Explanation: Box 1: Server1
For all types of application that you can publish using AD FS preauthentication, you must add a AD FS relying party trust to the Federation Service.
Use Server1 as it has AD FS.
Box 2: Server2
When publishing applications that use Integrated Windows authentication, the Web Application Proxy server uses Kerberos constrained delegation to authenticate users to the published application.
Box 3: Server2
To publish a claims-based application
1. On the Web Application Proxy server, in the Remote Access Management console, in the Navigation pane, click Web Application Proxy, and then in the Tasks pane, click Publish.
2. On the Publish New Application Wizard, on the Welcome page, click Next. Etc.
Box 4: Server2
Configure CAs and certificates (see c below)
Web Application Proxy servers require the following certificates in the certificate store on each Web Application Proxy server:
a) A certificate whose subject covers the federation service name. If you want to use Workplace Join, the certificate must also contain the following subject alternative names (SANs): <federation service name>.<domain> and enterpriseregistration.<domain>.
b) A wildcard certificate, a subject alternative name (SAN) certificate, several SAN certificates, or several certificates whose subjects cover each web application.
c) A copy of the certificate issued to external servers when using client certificate preauthentication.
NEW QUESTION 2
Your network contains an Active Directory domain named contoso.com.
The domain contains two domain controllers named DC1 and DC2 that run Windows Server 2012 R2.
DC1 and DC2 fail to replicate Active Directory information. You confirm that DC1 and DC2 have network connectivity.
The NTDS Settings of DC2 are configured as shown in the NTDS Settings exhibit. (Click tie Exhibit button.)
DNS is configured as shown in the DNS exhibit. (Click the Exhibit button.)
You need to ensure that DC1 and DC2 can replicate immediately.
Which two actions should you perform? (Each correct answer presents part of the solution. Choose two.)
- A. From DC1, restart the Netlogon service
- B. From DC2, run nltest.exe /sync
- C. From DC1, run ipconfig /flushdns
- D. From DC1, run repadmin /syncall
- E. From DC2, run ipconfig /registerdns
- F. From DC2, restart the Netlogon service
Answer: DF
Explanation: The figure of the DNS configuration can be seen that the alias (CNAME) entry that identifies DC2 as a domain controller of the domain certbase.de missing. While ipconfig / registerdns ensures that the IP address of a DNS client in DNS is registered, is restarting the Netlogon service on a domain controller ensures that all entries for the service location (Service Resource Records, SRVs) be the domain controller registered or renewed. After the service location records for DC2 completed or modified, can on one of the two domain controller with a call from repadmin / syncall immediate replication of the Active Directory database are introduced.
NEW QUESTION 3
You have an enterprise certification authority (CA) named CA1. You configure a recovery agent for CA1.
On CA1, you create a new certificate template named CertTemplate1, and then you
configure CA1 to allow certificates to be requested based on CertTemplate1.
You need to ensure that new certificates issued based on CertTemplate1 can be recovered.
What should you do?
- A. the Certification Authority console, modify the enrollment agents of CA1.
- B. From the Certification Authority console, modify the enrollment managers of CA1.
- C. From the Certification Templates console, modify the Issuance Requirements setting of CertTemplate1.
- D. From the Certification Templates console, modify the Request Handling setting of CertTemplate1.
Answer: C
NEW QUESTION 4
You perform a full installation of Windows Server 2012 R2 on a virtual machine named Server1.
You plan to use Server1 as a reference image.
You need to minimize the amount of storage space used by the Windows Server 2012 R2 installation.
Which cmdlet should you use?
- A. Remove-Module
- B. Optimize-VHD
- C. Optimize-Volume
- D. Uninstall-WindowsFeature
Answer: B
Explanation: The Optimize-VHD cmdlet optimizes the allocation of space in or more virtual hard disk files, except for fixed virtual hard disks. The Compact operation is used to optimize the files.
This operation reclaims unused blocks as well as rearranges the blocks to be more efficiently packed, which reduces the size of a virtual hard disk file.
Reference: Optimize-VHD
http://technet.microsoft.com/en-us/library/hh849732.aspx http://technet.microsoft.com/en-us/library/hh848458.aspx http://technet.microsoft.com/en-us/library/hh848675.aspx http://technet.microsoft.com/en-us/library/jj205471.aspx
NEW QUESTION 5
You have a server named Server1 that runs Windows Server 2012 R2. Server1 has the Windows Deployment Services server role installed.
You back up Server1 each day by using Windows Server Backup. The disk array on Server1 fails.
You replace the disk array.
You need to restore Server1 as quickly as possible. What should you do?
- A. Start Server1 from the Windows Server 2012 R2 installation media.
- B. Start Server1and press F8.
- C. Start Server1 and press Shift+F8.
- D. Start Server1 by using the PXE.
Answer: A
Explanation: A. Recovery of the OS uses the Windows Setup Disc http://technet.microsoft.com/en-us/library/cc753920.aspx http://www.windowsnetworking.com/articles_tutorials/Restoring-Windows-Server- BareMetal.html
NEW QUESTION 6
Your network contains three servers named Server1, Server2, and Server3. All servers run Windows Server 2012 R2.
You need to ensure that Server1 can provide iSCSI storage for Server2 and Server3. What should you do on Server1?
- A. Start the Microsoft iSCSI Initiator Service and configure the iSCSI Initiator Properties.
- B. Install the iSNS Server service feature and create a Discovery Domain.
- C. Install the Multipath I/O (MPIO) feature and configure the MPIO Properties.
- D. Install the iSCSI Target Server role service and configure iSCSI targets.
Answer: D
Explanation: iSCSI Target Server: The server runs the iSCSI Target. It is also the iSCSI Target role name in Windows Server 2012.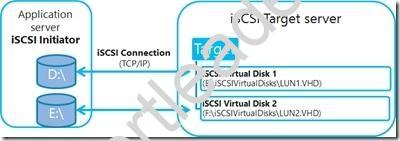
Note:
iSCSI: it is an industry standard protocol allow sharing block storage over the Ethernet. The server shares the storage is called iSCSI Target. The server (machine) consumes the storage is called iSCSI initiator. Typically, the iSCSI initiator is an application server. For example, iSCSI Target provides storage to a SQL server, the SQL server will be the iSCSI initiator in this deployment.
Target: It is an object which allows the iSCSI initiator to make a connection. The Target keeps track of the initiators which are allowed to be connected to it. The Target also keeps track of the iSCSI virtual disks which are associated with it. Once the initiator establishes the connection to the Target, all the iSCSI virtual disks associated with the Target will be accessible by the initiator.
NEW QUESTION 7
Your network contains an Active Directory domain named contoso.com. The domain contains a domain controller named DC1 that runs Windows Server 2012 R2. DC1 has the DNS Server server role installed.
The network contains client computers that run either Linux, Windows 7, or Windows 8. You have a standard primary zone named adatum.com as shown in the exhibit. (Click the Exhibit button.)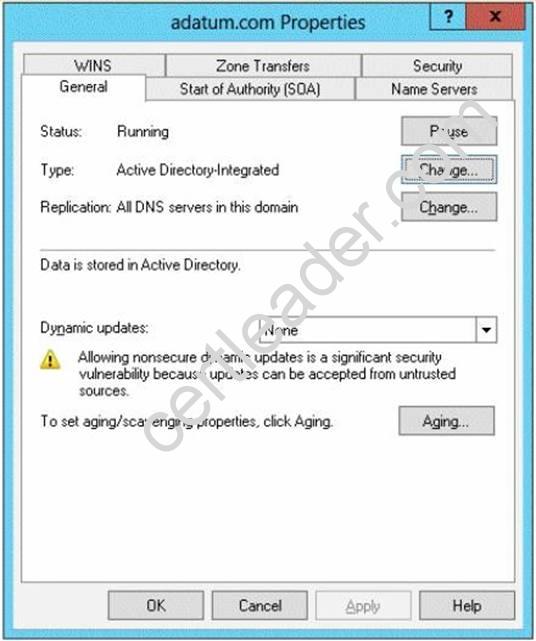
You plan to configure Name Protection on all of the DHCP servers.
You need to configure the adatum.com zone to support Name Protection.
Which two configurations should you perform from DNS Manager? (Each correct answer presents part of the solution. Choose two.)
- A. Sign the zone.
- B. Store the zone in Active Directory.
- C. Modify the Security settings of the zone.
- D. Configure Dynamic updates.
- E. Add a DNS key record
Answer: BD
Explanation: Name protection requires secure update to work. Without name protection DNS names may be hijacked.
You can use the following procedures to allow only secure dynamic updates for a zone. Secure dynamic update is supported only for Active Directory–integrated zones. If the zone type is configured differently, you must change the zone type and directory-integrate the zone before securing it for Domain Name System (DNS) dynamic updates.
1. (B) Convert primary DNS server to Active Directory integrated primary
2. (D) Enable secure dynamic updates
Reference: DHCP: Secure DNS updates should be configured if Name Protection is enabled on any IPv4 scope
http://technet.microsoft.com/en-us/library/ee941152(v=ws.10).aspx
NEW QUESTION 8
Your network contains an Active Directory forest named contoso.com. The forest contains a single domain. The forest contains three Active Directory sites named SiteA, SiteB, and SiteC. The sites contain four domain controllers. The domain controllers are configured as shown in the following table.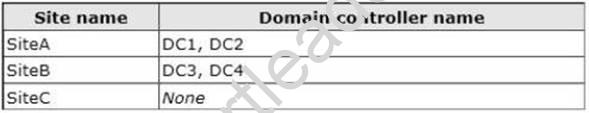
An IP site link exits between each site.
You discover that the users in SiteC are authenticated by the domain controllers in SiteA and SiteB.
You need to ensure that the SiteC users are authenticated by the domain controllers in SiteB, unless all of the domain controllers in SiteB are unavailable.
What should you do?
- A. Create an SMTP site link between SiteB and SiteC.
- B. Create additional connection objects for DC3 and DC4.
- C. Decrease the cost of the site link between SiteB and SiteC.
- D. Create additional connection objects for DC1 and DC2.
Answer: C
Explanation: By decreasing the site link cost between SiteB and SiteC the SiteC users would be authenticated by SiteB rather than by SiteA.
NEW QUESTION 9
Your network contans one active directory domain named contoso.com.
The domain contains two servers named Server1 and Server2 that run Windows Server 2012 R2.
You perform daily backups of the data on Server1 to microsoft azure. You need to restore the data from the 1st backup of Server1 to Server2. What should you do first?
- A. On Server2, install the azure backup agent.
- B. In the domain, add server1 to the backup operators group.
- C. From the azure management portal, modify the configuration of the backup vault.
- D. On Server2, install the windows server backup feature.
Answer: A
Explanation: https://azure.microsoft.com/en-us/documentation/articles/backup-azure-restore-windows-server/#recover-to-an-alternate-machine
NEW QUESTION 10
Your network contains two servers named HV1 and HV2. Both servers run Windows Server 2012 R2 and have the Hyper-V server role installed.
HV1 hosts 25 virtual machines. The virtual machine configuration files and the virtual hard disks are stored in D:VM.
You shut down all of the virtual machines on HV1. You copy D:VM to D:VM on HV2.
You need to start all of the virtual machines on HV2. You want to achieve this goal by using the minimum amount of administrative effort.
What should you do?
- A. Run the Import-VMInitialReplication cmdlet.
- B. From HV1, export all virtual machines to D:V
- C. Copy D:VM to D:VM on HV2 and overwrite the existing file
- D. On HV2, run the Import Virtual Machine wizard.
- E. From HV1, export all virtual machines to D:V
- F. Copy D:VM to D:VM on HV2 and overwrite the existing file
- G. On HV2, run the New Virtual Machine wizard.
- H. Run the Import-VM cmdlet.
Answer: D
Explanation: Import-VM
Imports a virtual machine from a file.
Example
Imports the virtual machine from its configuration file. The virtual machine is registered in- place, so its files are not copied.
Windows PowerShell
PS C:> Import-VM –Path 'D:TestVirtualMachines5AE40946-3A98-428E-8C83- 081A3C6BD18C.XML'
Reference: Import-VM
NEW QUESTION 11
Your network contains an Active Directory forest named adatum.com. All servers run Windows Server 2012 R2. The domain contains four servers. The servers are configured as shown in the following table.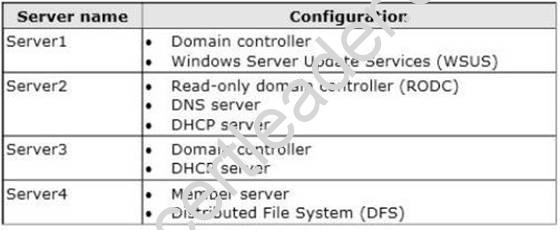
You need to deploy IP Address Management (IPAM) to manage DNS and DHCP. On which server should you install IPAM?
- A. Server1
- B. Server2
- C. Server3
- D. Server4
Answer: D
Explanation: An IPAM server is intended as a single-purpose server. It is not recommended to collocate other network infrastructure roles such as DNS or DHCP on the same server. IPAM installation is not supported on a domain controller, and discovery of DHCP servers will be disabled if you install IPAM on a server that is also running the DHCP Server service. The following features and tools are automatically installed when you install IPAM Server.
Reference: IPAM Deployment Planning
NEW QUESTION 12
Your network contains an Active Directory domain named contoso.com. The network contains a file server named Server1 that runs Windows Server 2012 R2.
You are configuring a central access policy for temporary employees.
You enable the Department resource property and assign the property a suggested value of Temp.
You need to configure a target resource condition for the central access rule that is scoped
to resources assigned to Temp only. Which condition should you use?
- A. (Temp.Resource Equals "Department")
- B. (Resource.Temp Equals "Department")
- C. (Resource.Department Equals "Temp")
- D. (Department.Value Equals "Temp")
Answer: C
Explanation: Example:
Targeting: Resource.Department Contains Finance
Access rule: Allow read User.Country=Resource.Country AND User.department = Resource.Department
Reference: Deploy a Central Access Policy (Demonstration Steps)
NEW QUESTION 13
Your network contains an Active Directory domain named contoso.com.
The domain contains a domain controller named Dc1. DC1 has the DNS Server server role installed.
The network has two sites named Site1 and Site2. Site1 uses 10.10.0.0/16 IP addresses and Site2 uses 10.11.0.0/16 IP addresses.
All computers use DC1 as their DNS server. The domain contains four servers named Server1, Server2, Server3, and Server4.
All of the servers run a service named Service1. DNS host records are configured as shown in the exhibit. (Click the Exhibit button.)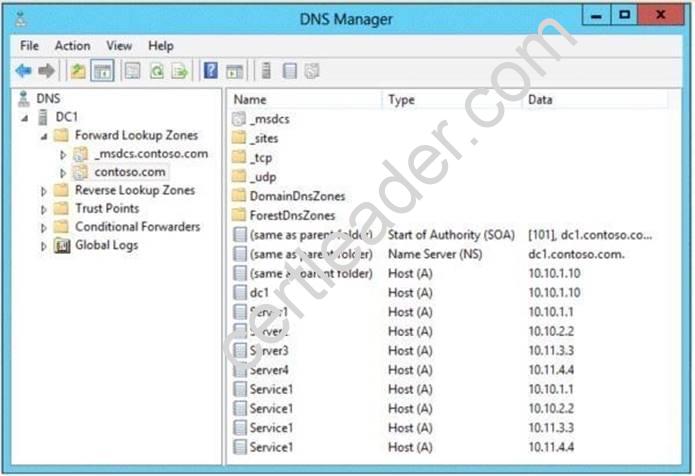
You discover that computers from the 10.10.1.0/24 network always resolve Service1 to the [P address of Server1.
You need to configure DNS on DC1 to distribute computers in Site1 between Server1 and Server2 when the computers attempt to resolve Service1.
What should run on DC1?
- A. dnscmd /config /bindsecondaries 1
- B. dnscmd /config /localnetpriority 0
- C. dnscmd /config /localnetprioritynetmask 0x0000ffff
- D. dnscmd /config /roundrobin 0
Answer: C
Explanation: A. Specifies use of fast transfer format used by legacy Berkeley Internet Name Domain (BIND) servers. 1 enables
B. Disables netmask ordering.
C. You can use the Dnscmd /Config /LocalNetPriorityNetMask 0x0000FFFF command to use class B ( or 16 bit) for netmask ordering for DNS round robin
D. Disables round robin rotation.
http://technet.microsoft.com/en-us/library/cc737355(v=ws.10).aspx http://technet.microsoft.com/en-us/library/cc738473(v=ws.10).aspx http://support.microsoft.com/kb/842197 http://technet.microsoft.com/en-us/library/cc779169(v=ws.10).aspx
NEW QUESTION 14
Your network contains an Active Directory domain named contoso.com. Network Access Protection (NAP) is deployed to the domain.
You need to create NAP event trace log files on a client computer. What should you run?
- A. Logman
- B. Tracert
- C. Register-EngineEvent
- D. Register-ObjectEvent
Answer: A
NEW QUESTION 15
You have a server named Server1 that runs Windows Server 2012 R2. You modify the properties of a system driver and you restart Server1.
You discover that Server1 continuously restarts without starting Windows Server 2012 R2.
You need to start Windows Server 2012 R2 on Server1 in the least amount of time. The solution must minimize the amount of data loss.
Which Advanced Boot Option should you select?
- A. Repair Your Computer
- B. Last Known Good Configuration (advanced)
- C. Disable Driver Signature Enforcement
- D. Disable automatic restart on system failure
Answer: B
Explanation: Try using Last Known Good Configuration if you can't start Windows, but it started correctly the last time you turned on the computer.
Reference: Using Last Known Good Configuration
NEW QUESTION 16
HOTSPOT
Your network contains an Active Directory domain named contoso.com. The domain contains a file server named Server1. Server1 is a BranchCache hosted cache server that is located in a branch office.
The network contains client computers that run either Windows 7 or Windows 8.
For the branch office, all of the user accounts and the client computer accounts are located in an organizational unit (OU) named Branch1. A Group Policy object (GPO) named GPO1 is linked to Branch 1. GPO1 contains the BranchCache settings.
You discover that users in the branch office who have client computers that run Windows 7 do not access cached content from Server1. Users in the branch office who have Windows 8 computers access cached content from Server1.
You need to configure the Windows 7 computers to use BranchCache on Server1. Which setting should you configure in GPO1?
To answer, select the appropriate setting in the answer area.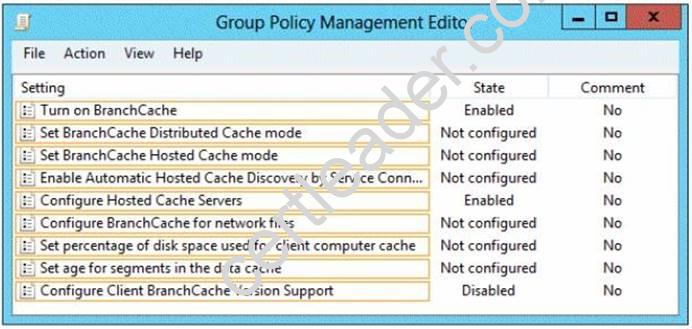
Answer:
Explanation: Hosted Cache mode
In hosted cache mode, cached content is maintained on a computer running Windows Server 2008 R2 on the branch office network.
NEW QUESTION 17
You have a server named Server1 that runs Windows Server 2012 R2.
You need to configure Server1 to create an entry in an event log when the processor usage exceeds 60 percent.
Which type of data collector should you create?
- A. an event trace data collector
- B. a performance counter data collector
- C. a performance counter alert
- D. a configuration data collector
Answer: C
NEW QUESTION 18
Your network contains an Active Directory domain named contoso.com. All domain controllers run Windows Server 2012 R2. The domain contains two domain controllers. The domain controllers are configured as shown in the following table.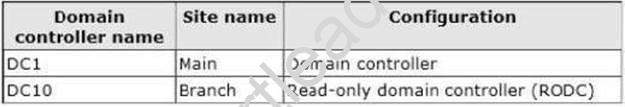
The Branch site contains a perimeter network.
For security reasons, client computers in the perimeter network can communicate with client computers in the Branch site only. You plan to deploy a new RODC to the perimeter network in the Branch site. You need to ensure that the new RODC will be able to replicate from DC10. What should you do first on DC10?
- A. Enable the Bridge all site links setting.
- B. Run the Active Directory Domain Services Configuration Wizard.
- C. Create an Active Directory site link bridge.
- D. Create an Active Directory site.
Answer: C
Explanation: A. Site link transitivity is controlled by the Bridge all site links option on the properties pages of transport folders (such as IP or SMTP) in the Active Directory Sites and Services snapin. Site link transitivity is enabled by default.
B.
C. If you cannot place a writable Windows Server 2008 domain controller in the nearest site to the RODC, RODC replication depends on a site link bridge between the site links that contain the site of the RODC and the site of the writable Windows Server 2008 domain controller.
D. AD Site not readed for RODC
http://technet.microsoft.com/en-us/library/dd736189(v=WS.10).aspx http://technet.microsoft.com/en-us/library/cc738789(v=ws.10).aspx http://technet.microsoft.com/en-us/library/cc732632(v=ws.10).aspx http://technet.microsoft.com/en-us/library/cc778718(v=WS.10).aspx
100% Valid and Newest Version 70-412 Questions & Answers shared by 2passeasy, Get Full Dumps HERE: https://www.2passeasy.com/dumps/70-412/ (New 435 Q&As)