2026 New CAS-003 Exam Dumps with PDF and VCE Free: https://www.2passeasy.com/dumps/CAS-003/
Our pass rate is high to 98.9% and the similarity percentage between our CAS-003 study guide and real exam is 90% based on our seven-year educating experience. Do you want achievements in the CompTIA CAS-003 exam in just one try? I am currently studying for the CompTIA CAS-003 exam. Latest CompTIA CAS-003 Test exam practice questions and answers, Try CompTIA CAS-003 Brain Dumps First.
Online CAS-003 free questions and answers of New Version:
NEW QUESTION 1
A security architect is determining the best solution for a new project. The project is developing a new intranet with advanced authentication capabilities, SSO for users, and automated provisioning to streamline Day 1 access to systems. The security architect has identified the following requirements:
1. Information should be sourced from the trusted master data source.
2. There must be future requirements for identity proofing of devices and users.
3. A generic identity connector that can be reused must be developed.
4. The current project scope is for internally hosted applications only.
Which of the following solution building blocks should the security architect use to BEST meet the requirements?
- A. LDAP, multifactor authentication, oAuth, XACML
- B. AD, certificate-based authentication, Kerberos, SPML
- C. SAML, context-aware authentication, oAuth, WAYF
- D. NAC, radius, 802.1x, centralized active directory
Answer: A
NEW QUESTION 2
DRAG DROP
A security consultant is considering authentication options for a financial institution. The following authentication options are available security mechanism to the appropriate use case. Options may be used once.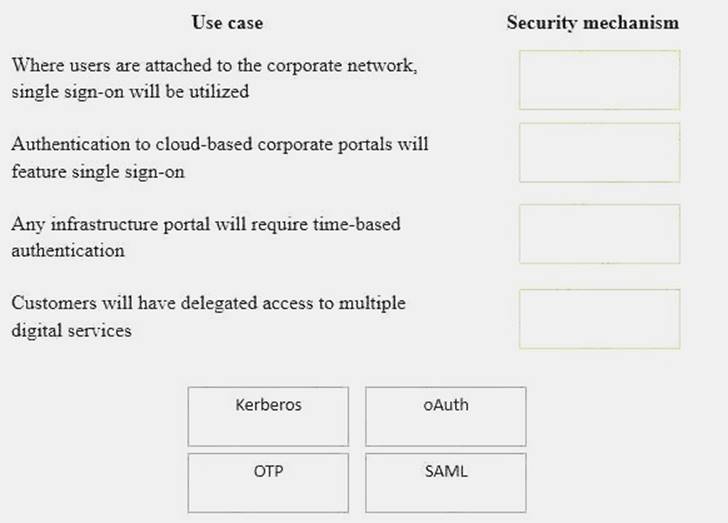
Solution:
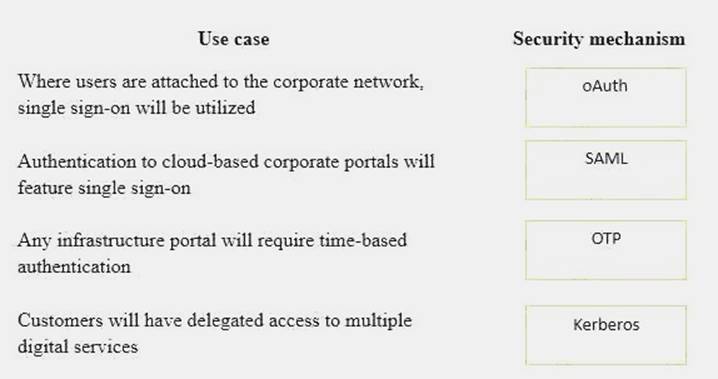
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 3
Given the following output from a security tool in Kali:
- A. Log reduction
- B. Network enumerator
- C. Fuzzer
- D. SCAP scanner
Answer: D
NEW QUESTION 4
After investigating virus outbreaks that have cost the company $1,000 per incident, the company’s Chief Information Security Officer (CISO) has been researching new antivirus software solutions to use and be fully supported for the next two years. The CISO has narrowed down the potential solutions to four candidates that meet all the company’s performance and capability requirements:
Using the table above, which of the following would be the BEST business-driven choice among five possible solutions?
- A. Product A
- B. Product B
- C. Product C
- D. Product D
- E. Product E
Answer: E
NEW QUESTION 5
An administrator wants to enable policy based filexible mandatory access controls on an open source OS to prevent abnormal application modifications or executions. Which of the following would BEST
accomplish this?
- A. Access control lists
- B. SELinux
- C. IPtables firewall
- D. HIPS
Answer: B
Explanation:
The most common open source operating system is LINUX.
Security-Enhanced Linux (SELinux) was created by the United States National Security Agency (NSA) and is a Linux kernel security module that provides a mechanism for supporting access control
security policies, including United States Department of Defense–style mandatory access controls (MAC).
NSA Security-enhanced Linux is a set of patches to the Linux kernel and some utilities to incorporate a strong, filexible mandatory access control (MAC) architecture into the major subsystems of the kernel. It provides an enhanced mechanism to enforce the separation of information based on confidentiality and integrity requirements, which allows threats of tampering and bypassing of application security mechanisms to be addressed and enables the confinement of damage that can
be caused by malicious or flawed applications. Incorrect Answers:
A: An access control list (ACL) is a list of permissions attached to an object. An ACL specifies which users or system processes are granted access to objects, as well as what operations are allowed on given objects. ACLs do not enable policy based filexible mandatory access controls to prevent abnormal application modifications or executions.
C: A firewall is used to control data leaving a network or entering a network based on source and destination IP address and port numbers. IPTables is a Linux firewall. However, it does not enable policy based filexible mandatory access controls to prevent abnormal application modifications or executions.
D: Host-based intrusion prevention system (HIPS) is an installed software package which monitors a single host for suspicious activity by analyzing events occurring within that host. It does not enable policy based filexible mandatory access controls to prevent abnormal application modifications or executions.
References:
https://en.wikipedia.org/wiki/SeHYPERLINK "https://en.wikipedia.org/wiki/Security- Enhanced_Linux"curity-Enhanced_Linux
NEW QUESTION 6
While attending a meeting with the human resources department, an organization’s information security officer sees an employee using a username and password written on a memo pad to log into a specific service. When the information security officer inquires further as to why passwords are being written down, the response is that there are too many passwords to remember for all the different services the human resources department is required to use.
Additionally, each password has specific complexity requirements and different expiration time frames. Which of the following would be the BEST solution for the information security officer to recommend?
- A. Utilizing MFA
- B. Implementing SSO
- C. Deploying 802.1X
- D. Pushing SAML adoption
- E. Implementing TACACS
Answer: B
NEW QUESTION 7
A security administrator is shown the following log excerpt from a Unix system:
2013 Oct 10 07:14:57 web14 sshd[1632]: Failed password for root from 198.51.100.23 port 37914 ssh2
2013 Oct 10 07:14:57 web14 sshd[1635]: Failed password for root from 198.51.100.23 port 37915 ssh2
2013 Oct 10 07:14:58 web14 sshd[1638]: Failed password for root from 198.51.100.23 port 37916 ssh2
2013 Oct 10 07:15:59 web14 sshd[1640]: Failed password for root from 198.51.100.23 port 37918 ssh2
2013 Oct 10 07:16:00 web14 sshd[1641]: Failed password for root from 198.51.100.23 port 37920 ssh2
2013 Oct 10 07:16:00 web14 sshd[1642]: Successful login for root from 198.51.100.23 port 37924 ssh2
Which of the following is the MOST likely explanation of what is occurring and the BEST immediate response? (Select TWO).
- A. An authorized administrator has logged into the root account remotely.
- B. The administrator should disable remote root logins.
- C. Isolate the system immediately and begin forensic analysis on the host.
- D. A remote attacker has compromised the root account using a buffer overflow in sshd.
- E. A remote attacker has guessed the root password using a dictionary attack.
- F. Use iptables to immediately DROP connections from the IP 198.51.100.23.
- G. A remote attacker has compromised the private key of the root account.
- H. Change the root password immediately to a password not found in a dictionar
Answer: CE
Explanation:
The log shows six attempts to log in to a system. The first five attempts failed due to ‘failed password’. The sixth attempt was a successful login. Therefore, the MOST likely explanation of what is occurring is that a remote attacker has guessed the root password using a dictionary attack.
The BEST immediate response is to isolate the system immediately and begin forensic analysis on the host. You should isolate the system to prevent any further access to it and prevent it from doing any damage to other systems on the network. You should perform a forensic analysis on the system to determine what the attacker did on the system after gaining access.
Incorrect Answers:
A: It is unlikely that an authorized administrator has logged into the root account remotely. It is unlikely that an authorized administrator would enter an incorrect password five times.
B: Disabling remote root logins is not the best course of action. The attacker has already gained access to the system so potentially the damage is already done.
D: The log does not suggest a buffer overflow attack; the failed passwords suggest a dictionary attack. F: Using iptables to immediately DROP connections from the IP 198.51.100.23 is not the best course of action. The attacker has already gained access to the system so potentially the damage is already done.
G: The log does not suggest a remote attacker has compromised the private key of the root account; the failed passwords suggest a dictionary attack.
H: Changing the root password is a good idea but it is not the best course of action. The attacker has already gained access to the system so potentially the damage is already done.
NEW QUESTION 8
A large company is preparing to merge with a smaller company. The smaller company has been very profitable, but the smaller company’s main applications were created in-house. Which of the following actions should the large company’s security administrator take in preparation for the merger?
- A. A review of the mitigations implemented from the most recent audit findings of the smaller company should be performed.
- B. An ROI calculation should be performed to determine which company's application should be used.
- C. A security assessment should be performed to establish the risks of integration or co-existence.
- D. A regression test should be performed on the in-house software to determine security risks associated with the software.
Answer: C
Explanation:
With any merger regardless of the monetary benefit there is always security risks and prior to the merger the security administrator should assess the security risks to as to mitigate these. Incorrect Answers:
A: This is the concern of the smaller organization and not the bigger company for which the security
administrator is working.
B: The Cost benefit analysis (ROI) is done as part of the phased changeover process.
D: A regression test is used after a change to validate that inputs and outputs are correct, not prior to a merger.
References:
Project Management Institute, A Guide to the Project Management Body of Knowledge (PMBOK Guide), 5th Edition, Project Management Institute, Inc., Newtown Square, 2013, p. 345
Gregg, Michael, and Billy Haines, CASP CompTIA Advanced Security Practitioner Study Guide, John Wiley & Sons, Indianapolis, 2012, pp. 148, 165, 337
NEW QUESTION 9
DRAG DROP
Drag and drop the cloud deployment model to the associated use-case scenario. Options may be used only once or not at all.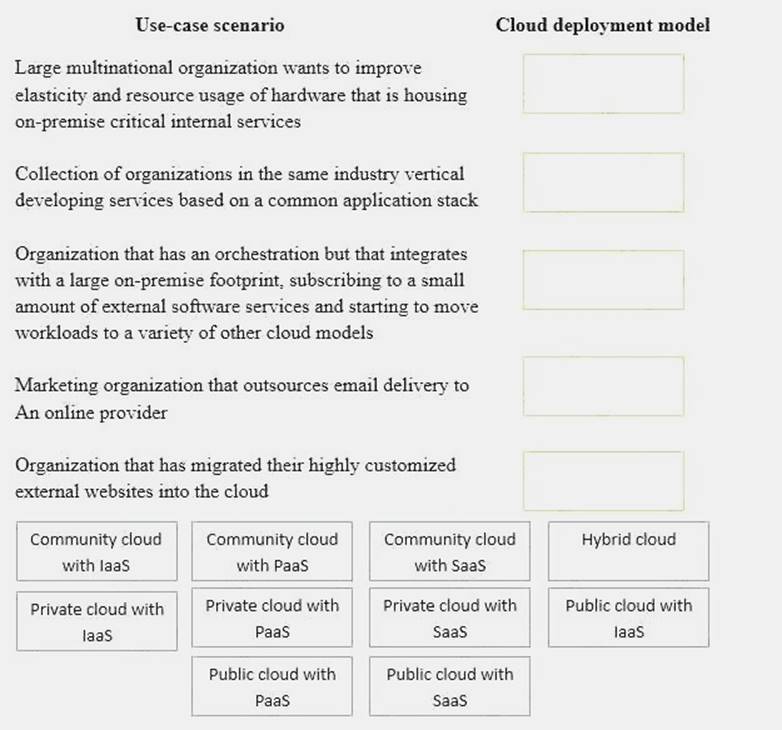
Solution:
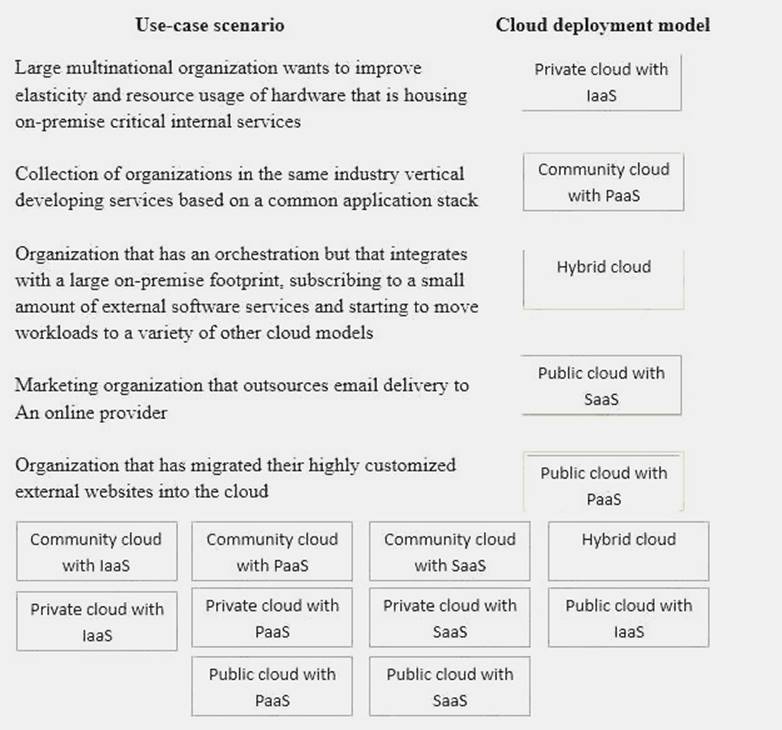
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 10
A security administrator notices a recent increase in workstations becoming compromised by malware. Often, the malware is delivered via drive-by downloads, from malware hosting websites, and is not being detected by the corporate antivirus. Which of the following solutions would provide the BEST protection for the company?
- A. Increase the frequency of antivirus downloads and install updates to all workstations.
- B. Deploy a cloud-based content filter and enable the appropriate category to prevent further infections.
- C. Deploy a WAF to inspect and block all web traffic which may contain malware and explogts.
- D. Deploy a web based gateway antivirus server to intercept viruses before they enter the networ
Answer: B
Explanation:
The undetected malware gets delivered to the company via drive-by and malware hosing websites. Display filters and Capture filters when deployed on the cloud-based content should provide the protection required.
Incorrect Answers:
A: The company already has an antivirus application that is not detecting the malware, increasing the frequency of antivirus downloads and installing the updates will thus not address the issue of the drive-by downloads and malware hosting websites.
C: A WAF is designed to sit between a web client and a web server to analyze OSI Layer 7 traffic; this will not provide the required protection in this case. WAFs are not 100% effective.
D: A web-based gateway antivirus is not going to negate the problem of drive-by downloads and malware hosting websites.
References:
Gregg, Michael, and Billy Haines, CASP CompTIA Advanced Security Practitioner Study Guide, John Wiley & Sons, Indianapolis, 2012, pp. 116, 405-406
NEW QUESTION 11
A forensics analyst suspects that a breach has occurred. Security logs show the company’s OS patch system may be compromised, and it is serving patches that contain a zero-day explogt and backdoor. The analyst extracts an executable file from a packet capture of communication between a client computer and the patch server. Which of the following should the analyst use to confirm this suspicion?
- A. File size
- B. Digital signature
- C. Checksums
- D. Anti-malware software
- E. Sandboxing
Answer: B
NEW QUESTION 12
An architect was recently hired by a power utility to increase the security posture of the company’s power generation and distribution sites. Upon review, the architect identifies legacy hardware with highly vulnerable and unsupported software driving critical operations. These systems must exchange data with each other, be highly synchronized, and pull from the Internet time sources.
Which of the following architectural decisions would BEST reduce the likelihood of a successful attack without harming operational capability? (Choose two.)
- A. Isolate the systems on their own network
- B. Install a firewall and IDS between systems and the LAN
- C. Employ own stratum-0 and stratum-1 NTP servers
- D. Upgrade the software on critical systems
- E. Configure the systems to use government-hosted NTP servers
Answer: BE
NEW QUESTION 13
The latest independent research shows that cyber attacks involving SCADA systems grew an average of 15% per year in each of the last four years, but that this year’s growth has slowed to around 7%. Over the same time period, the number of attacks against applications has decreased or stayed flat each year. At the start of the measure period, the incidence of PC boot loader or BIOS based attacks was negligible. Starting two years ago, the growth in the number of PC boot loader attacks has grown exponentially. Analysis of these trends would seem to suggest which of the following strategies should be employed?
- A. Spending on SCADA protections should stay steady; application control spending should increase substantially and spending on PC boot loader controls should increase substantially.
- B. Spending on SCADA security controls should stay steady; application control spending should decrease slightly and spending on PC boot loader protections should increase substantially.
- C. Spending all controls should increase by 15% to start; spending on application controls should be suspended, and PC boot loader protection research should increase by 100%.
- D. Spending on SCADA security controls should increase by 15%; application control spending should increase slightly, and spending on PC boot loader protections should remain steady.
Answer: B
Explanation:
Spending on the security controls should stay steady because the attacks are still ongoing albeit reduced in occurrence Due to the incidence of BIOS-based attacks growing exponentially as the application attacks being decreased or staying flat spending should increase in this field. Incorrect Answers:
A: The SCADA security control spending and not the SCADA protection spending should stay steady. There is no need to in spending on application control.
C: There is no n increase spending on all security controls.
D: This is partly correct, but the spending on application control does not have to increase and the BIOS protections should increase since these attacks are now more prevalent.
References:
Gregg, Michael, and Billy Haines, CASP CompTIA Advanced Security Practitioner Study Guide, John Wiley & Sons, Indianapolis, 2012, p. 343
https://en.wikipedia.org/wiki/SCADA
NEW QUESTION 14
A security analyst has been asked to develop a quantitative risk analysis and risk assessment for the company’s online shopping application. Based on heuristic information from the Security Operations Center (SOC), a Denial of Service Attack (DoS) has been successfully executed 5 times a year. The Business Operations department has determined the loss associated to each attack is $40,000. After implementing application caching, the number of DoS attacks was reduced to one time a year. The cost of the countermeasures was $100,000. Which of the following is the monetary value earned during the first year of operation?
- A. $60,000
- B. $100,000
- C. $140,000
- D. $200,000
Answer: A
Explanation:
ALE before implementing application caching: ALE = ARO x SLE
ALE = 5 x $40,000 ALE = $200,000
ALE after implementing application caching: ALE = ARO x SLE
ALE = 1 x $40,000 ALE = $40,000
The monetary value earned would be the sum of subtracting the ALE calculated after implementing application caching and the cost of the countermeasures, from the ALE calculated before implementing application caching.
Monetary value earned = $200,000 - $40,000 - $100,000 Monetary value earned = $60,000
Incorrect Answers:
B: $100,000 would be the answer if the ARO after implementing application caching was 0.
C: $140,000 is the expected loss in the first year. The ALE after implementing application caching + the cost of the countermeasures.
D: The answer cannot be $200,000 because in the first year of operation the ALE after implementing application caching is $40,000 and the cost of the countermeasures is $100,000.
References: http://www.pearsonitcertification.com/articles/article.aspx?p=418007HYPERLINK
"http://www.pearsonitcertification.com/articles/article.aspx?p=418007&seqNum=4"&HYPERLINK "http://www.pearsonitcertification.com/articles/article.aspx?p=418007&seqNum=4"seqNum=4
NEW QUESTION 15
A security analyst is attempting to break into a client’s secure network. The analyst was not given prior information about the client, except for a block of public IP addresses that are currently in use. After network enumeration, the analyst’s NEXT step is to perform:
- A. a gray-box penetration test
- B. a risk analysis
- C. a vulnerability assessment
- D. an external security audit
- E. a red team exercise
Answer: A
NEW QUESTION 16
Which of the following would be used in forensic analysis of a compromised Linux system? (Select THREE).
- A. Check log files for logins from unauthorized IPs.
- B. Check /proc/kmem for fragmented memory segments.
- C. Check for unencrypted passwords in /etc/shadow.
- D. Check timestamps for files modified around time of compromise.
- E. Use lsof to determine files with future timestamps.
- F. Use gpg to encrypt compromised data files.
- G. Verify the MD5 checksum of system binaries.
- H. Use vmstat to look for excessive disk I/
Answer: ADG
Explanation:
The MD5 checksum of the system binaries will allow you to carry out a forensic analysis of the compromised Linux system. Together with the log files of logins into the compromised system from unauthorized IPs and the timestamps for those files that were modified around the time that the compromise occurred will serve as useful forensic tools.
Incorrect Answers:
B: Checking for fragmented memory segments’ is not a forensic analysis tool to be used in this case. C: The ``/etc/shadow'', contains encrypted password as well as other information such as account or password expiration values, etc. The /etc/shadow file is readable only by the root account. This is a useful tool for Linux passwords and shadow file formats and is in essence used to keep user account information.
E: Isof is used on Linux as a future timestamp tool and not a forensic analysis tool. F: Gpg is an encryption tool that works on Mac OS X.
H: vmstat reports information about processes, memory, paging, block IO, traps, and cpu activity. The first report produced gives averages since the last reboot. Additional reports give information on a sampling period of length delay. The process and memory reports are instantaneous in either case. This is more of an administrator tool.
References:
Gregg, Michael, and Billy Haines, CASP CompTIA Advanced Security Practitioner Study Guide, John Wiley & Sons, Indianapolis, 2012, p. 387
httpsHYPERLINK "https://en.wikipedia.org/wiki/List_of_digital_forensics_tools"://en.wikipedia.org/wiki/List_of_digit al_forensics_tools
NEW QUESTION 17
Users have been reporting unusual automated phone calls, including names and phone numbers, that appear to come from devices internal to the company. Which of the following should the systems administrator do to BEST address this problem?
- A. Add an ACL to the firewall to block VoIP.
- B. Change the settings on the phone system to use SIP-TLS.
- C. Have the phones download new configurations over TFTP.
- D. Enable QoS configuration on the phone VLA
Answer: B
NEW QUESTION 18
An organization has implemented an Agile development process for front end web application development. A new security architect has just joined the company and wants to integrate security activities into the SDLC.
Which of the following activities MUST be mandated to ensure code quality from a security perspective? (Select TWO).
- A. Static and dynamic analysis is run as part of integration
- B. Security standards and training is performed as part of the project
- C. Daily stand-up meetings are held to ensure security requirements are understood
- D. For each major iteration penetration testing is performed
- E. Security requirements are story boarded and make it into the build
- F. A security design is performed at the end of the requirements phase
Answer: AD
Explanation:
SDLC stands for systems development life cycle. An agile project is completed in small sections called iterations. Each iteration is reviewed and critiqued by the project team. Insights gained from the critique of an iteration are used to determine what the next step should be in the project. Each
project iteration is typically scheduled to be completed within two weeks.
Static and dynamic security analysis should be performed throughout the project. Static program analysis is the analysis of computer software that is performed without actually executing programs (analysis performed on executing programs is known as dynamic analysis). In most cases the analysis is performed on some version of the source code, and in the other cases, some form of the object code.
For each major iteration penetration testing is performed. The output of a major iteration will be a functioning part of the application. This should be penetration tested to ensure security of the application.
Incorrect Answers:
B: Security standards and training does not ensure code quality from a security perspective. The only way to ensure code quality is to test the code itself.
C: Ensuring security requirements are understood does not ensure code quality from a security perspective. The only way to ensure code quality is to test the code itself.
E: Storyboarding security requirements does not ensure code quality from a security perspective. The only way to ensure code quality is to test the code itself.
F: A security design does not ensure code quality from a security perspective. The only way to ensure code quality is to test the code itself.
References: https://en.wikipedia.org/wiki/Static_program_analysis
http://searchcio.techtarget.HYPERLINK "http://searchcio.techtarget.com/definition/Agile-projectmanagement" com/definition/Agile-project-management
NEW QUESTION 19
......
Recommend!! Get the Full CAS-003 dumps in VCE and PDF From Certleader, Welcome to Download: https://www.certleader.com/CAS-003-dumps.html (New 555 Q&As Version)