2026 New PCCSA Exam Dumps with PDF and VCE Free: https://www.2passeasy.com/dumps/PCCSA/
Master the PCCSA Palo Alto Networks Certified Cybersecurity Associate content and be ready for exam day success quickly with this Certleader PCCSA exam answers. We guarantee it!We make it a reality and give you real PCCSA questions in our Paloalto-Networks PCCSA braindumps.Latest 100% VALID Paloalto-Networks PCCSA Exam Questions Dumps at below page. You can use our Paloalto-Networks PCCSA braindumps and pass your exam.
Free PCCSA Demo Online For Paloalto-Networks Certifitcation:
NEW QUESTION 1
Which well-known port is associated with the Simple Mail Transfer Protocol?
- A. 143
- B. 25
- C. 997
- D. 40
Answer: B
NEW QUESTION 2
A firewall located on an organization’s network perimeter can be used to protect against which type of attack?
- A. a malicious SaaS application file accessed from an unmanaged mobile phone
- B. ransomware installed from an infected USB drive
- C. malware installed on the laptop by a disgruntled employee
- D. a malicious PDF file located on an internet website
Answer: D
NEW QUESTION 3
Which option describes a characteristic of a distributed denial-of-service attack?
- A. uses multiple types of malware to corrupt system services
- B. uses a single remote host to delete data from multiple target servers
- C. uses a single remote host to flood a target network with traffic
- D. uses a botnet to flood traffic to a target network
Answer: D
NEW QUESTION 4
What is the function of a hashing protocol?
- A. encrypts data with encapsulation
- B. establishes an unencrypted tunnel
- C. establishes a secure tunnel
- D. provides data integrity
Answer: D
NEW QUESTION 5
What is an example of a distance-vector routing protocol?
- A. OSPF
- B. BGP
- C. RIP
- D. IGRP
Answer: C
NEW QUESTION 6
What method can be used to guarantee that a document originates from you and no one else?
- A. public key encryption, encrypting the document with the private key and making the public key available to others
- B. symmetric encryption, ecnrypting the document with the secret key and making a different secret key available to others
- C. symmetric encryption, ecnrypting the document with the secret key and making the same secret kay available to others
- D. public key encryption, encrypting the document with the private key and making the private key available to others
Answer: A
NEW QUESTION 7
From which resource can a Palo Alto Networks firewall get URL category information for URLs whose categories cannot be found on the firewall?
- A. App-ID database
- B. WildFire
- C. PDF file
- D. PAN-DB database
Answer: D
NEW QUESTION 8
Which two types of SaaS applications are allowed by an IT department? (Choose two.)
- A. tolerated
- B. certified
- C. sanctioned
- D. unsanctioned
Answer: AC
NEW QUESTION 9
Match the Palo Alto Networks Wild Fire analysis verdict with its definition.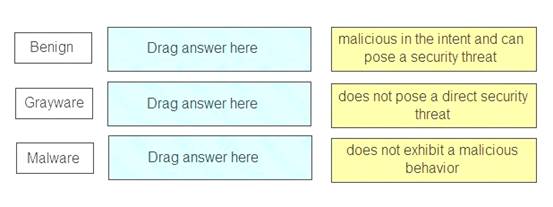
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
Benign – does not exhibit a malicious behavior Grayware – does not pose a direct security threat
Malware – malicious in the intent and can pose a security threat References:
NEW QUESTION 10
Which security component should you configure to block viruses not seen and blocked by the perimeter firewall?
- A. strong endpoint passwords
- B. endpoint disk encryption
- C. endpoint antivirus software
- D. endpoint NIC ACLs
Answer: C
NEW QUESTION 11
Which type of firewall monitors traffic streams from beginning to end?
- A. circuit-level gateway
- B. stateless
- C. stateful
- D. packet filter
Answer: C
NEW QUESTION 12
Which type of attack floods a target with ICMP requests?
- A. route table poisoning
- B. reconnaissance
- C. IP spoofing
- D. denial-of-service
Answer: D
NEW QUESTION 13
Which Palo Alto Networks product or feature includes machine learning to enhance security?
- A. Panorama
- B. MineMeld
- C. Magnifier
- D. User-ID
Answer: C
NEW QUESTION 14
Which two components are part of a next-generation firewall security policy? (Choose two.)
- A. role-based access controls
- B. user identification
- C. content identification
- D. file permissions
Answer: BC
NEW QUESTION 15
An attacker emails a malicious URL links to 50,000 email addresses. The email states that users can click the link to view the latest celebrity news, but the link also secretly infects the user’s laptop. This scenario describes which type of attack?
- A. whailing
- B. phishing
- C. drive-by download
- D. pharming
Answer: B
NEW QUESTION 16
Match each option with the term it describes.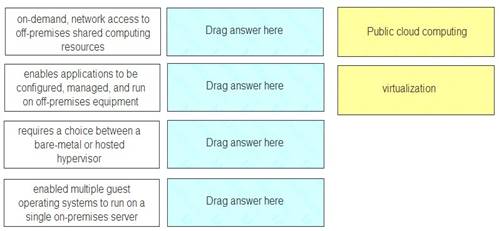
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
Public-cloud computing Public-cloud computing Virtualization Virtualization
NEW QUESTION 17
Which mobile device management feature prevents jailbreaking or rooting?
- A. software distribution
- B. malware protection
- C. policy enforcement
- D. data loss prevention
Answer: C
NEW QUESTION 18
......
Thanks for reading the newest PCCSA exam dumps! We recommend you to try the PREMIUM Surepassexam PCCSA dumps in VCE and PDF here: https://www.surepassexam.com/PCCSA-exam-dumps.html (50 Q&As Dumps)