2026 New SY0-701 Exam Dumps with PDF and VCE Free: https://www.2passeasy.com/dumps/SY0-701/
Your success in CompTIA SY0-701 is our sole target and we develop all our SY0-701 braindumps in a way that facilitates the attainment of this target. Not only is our SY0-701 study material the best you can find, it is also the most detailed and the most updated. SY0-701 Practice Exams for CompTIA SY0-701 are written to the highest standards of technical accuracy.
Also have SY0-701 free dumps questions for you:
NEW QUESTION 1
A security team is providing input on the design of a secondary data center that has Which of the following should the security team recommend? (Select two).
- A. Coniguring replication of the web servers at the primary site to offline storage
- B. Constructing the secondary site in a geographically disperse location
- C. Deploying load balancers at the primary site
- D. Installing generators
- E. Using differential backups at the secondary site
- F. Implementing hot and cold aisles at the secondary site
Answer: BD
Explanation:
* B. Constructing the secondary site in a geographically disperse location would ensure that a natural disaster at the primary site would not affect the secondary site. It would also allow for failover during traffic surge situations by distributing the load across different regions. D. Installing generators would provide protection against power surges and outages by providing backup power sources in case of a failure. Generators are part of the physical security requirements for data centers as they ensure availability and resilience. References: 1
CompTIA Security+ Certification Exam Objectives, page 8, Domain 2.0: Architecture and Design, Objective 2.1 : Explain the importance of secure staging deployment concepts 2
CompTIA Security+ Certification Exam
Objectives, page 9, Domain 2.0: Architecture and Design, Objective 2.3: Summarize secure application
development, deployment, and automation concepts 3
CompTIA Security+ Certification Exam Objectives, page 11, Domain 2.0: Architecture and Design, Objective 2.5: Explain the importance of physical security controls
NEW QUESTION 2
Physical access to the organization's servers in the data center requires entry and exit through multiple access points: a lobby, an access control vestibule, three doors leading to the server floor itself and eventually to a caged area solely for the organization's hardware. Which of the following controls is described in this scenario?
- A. Compensating
- B. Deterrent
- C. Preventive
- D. Detective
Answer: C
Explanation:
The scenario describes preventive controls, which are designed to stop malicious actors from gaining access to the organization's servers. This includes using multiple access points, such as a lobby, an access control vestibule, and multiple doors leading to the server floor, as well as caging the organization's hardware. According to the CompTIA Security+ SY0-601 document, preventive controls are "designed to stop malicious actors from performing a malicious activity or gaining access to an asset." These controls can include technical solutions, such as authentication and access control systems, physical security solutions, such as locks and barriers, and administrative solutions such as policy enforcement.
NEW QUESTION 3
Which of the following threat actors is most likely to be motivated by ideology?
- A. Business competitor
- B. Hacktivist
- C. Criminal syndicate
- D. Script kiddie
- E. Disgruntled employee
Answer: B
Explanation:
A hacktivist is a threat actor who is most likely to be motivated by ideology. A hacktivist is a person or group who uses hacking skills and techniques to promote a political or social cause. Hacktivists may target government, corporate, or religious entities that they disagree with or oppose. Hacktivists may use various methods to achieve their goals, such as defacing websites, leaking sensitive data, launching denial-of-service attacks, or spreading propaganda. Hacktivists are not motivated by financial gain or personal benefit, but rather by their beliefs and values. References: https://www.uscybersecurity.net/hacktivist/
https://www.uscybersecurity.net/hacktivist/ https://www.fortinet.com/resources/cyberglossary/what-is-hacktivism
https://www.fortinet.com/resources/cyberglossary/what-is-hacktivism
NEW QUESTION 4
A security administrator wants to implement a program that tests a user's ability to recognize attacks over the organization's email system Which of the following would be BEST suited for this task?
- A. Social media analysis
- B. Annual information security training
- C. Gamification
- D. Phishing campaign
Answer: D
Explanation:
A phishing campaign is a simulated attack that tests a user's ability to recognize attacks over the organization's email system. Phishing campaigns can be used to train users on how to identify and report suspicious emails.
References: CompTIA Security+ Study Guide, Exam SY0-601, 4th Edition, Chapter 2: Technologies and Tools, pp. 85-86.
NEW QUESTION 5
A security analyst is currently addressing an active cyber incident. The analyst has been able to identify affected devices that are running a malicious application with a unique hash. Which of the following is the next step according to the incident response process?
- A. Recovery
- B. Lessons learned
- C. Containment
- D. Preparation
Answer: C
Explanation:
Containment is the next step according to the incident response process after identifying affected devices that are running a malicious application with a unique hash. Containment involves isolating the compromised devices or systems from the rest of the network to prevent the spread of the attack and limit its impact. Containment can be done by disconnecting the devices from the network, blocking network traffic to or from them, or applying firewall rules or access control lists. Containment is a critical step in incident response because it helps to preserve evidence for further analysis and remediation, and reduces the risk of data loss or exfiltration
https://www.fortinet.com/resources/cyberglossary/incident-response https://www.ibm.com/topics/incident-response
NEW QUESTION 6
A company is required to continue using legacy software to support a critical service. Which of the following BEST explains a risk of this practice?
- A. Default system configuration
- B. Unsecure protocols
- C. Lack of vendor support
- D. Weak encryption
Answer: C
Explanation:
Using legacy software to support a critical service poses a risk due to lack of vendor support. Legacy software is often outdated and unsupported, which means that security patches and upgrades are no longer available. This can leave the system vulnerable to exploitation by attackers who may exploit known vulnerabilities in the software to gain unauthorized access to the system.
Reference: CompTIA Security+ Study Guide, Exam SY0-601, Chapter 1: Attacks, Threats, and Vulnerabilities
NEW QUESTION 7
A junior security analyst is reviewing web server logs and identifies the following pattern in the log file: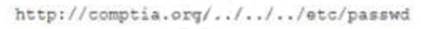
Which ol the following types of attacks is being attempted and how can it be mitigated?
- A. XS
- B. mplement a SIEM
- C. CSR
- D. implement an IPS
- E. Directory traversal implement a WAF
- F. SQL infection, mplement an IDS
Answer: C
Explanation:
Detailed
The attack being attempted is directory traversal, which is a web application attack that allows an attacker to access files and directories outside of the web root directory. A WAF can help mitigate this attack by detecting and blocking attempts to access files outside of the web root directory.
References: CompTIA Security+ Study Guide: Exam SY0-601, Chapter 4: Securing Application Development and Deployment, p. 191
NEW QUESTION 8
A company uses a drone for precise perimeter and boundary monitoring. Which of the following should be MOST concerning to the company?
- A. Privacy
- B. Cloud storage of telemetry data
- C. GPS spoofing
- D. Weather events
Answer: A
Explanation:
The use of a drone for perimeter and boundary monitoring can raise privacy concerns, as it may capture video and images of individuals on or near the monitored premises. The company should take measures to ensure that privacy rights are not violated. References: CompTIA Security+ Study Guide, Exam SY0-601, 4th Edition, Chapter 8
CompTIA Security+ Study Guide, Exam SY0-601, 4th Edition, Chapter 8
NEW QUESTION 9
A technician is setting up a new firewall on a network segment to allow web traffic to the internet while hardening the network. After the firewall is configured, users receive errors stating the website could not be located. Which of the following would best correct the issue?
- A. Setting an explicit deny to all traffic using port 80 instead of 443
- B. Moving the implicit deny from the bottom of the rule set to the top
- C. Configuring the first line in the rule set to allow all traffic
- D. Ensuring that port 53 has been explicitly allowed in the rule set
Answer: D
Explanation:
Port 53 is the default port for DNS traffic. If the firewall is blocking port 53, then users will not be able to resolve domain names and will receive errors stating that the website could not be located.
The other options would not correct the issue. Setting an explicit deny to all traffic using port 80 instead of 443 would block all HTTP traffic, not just web traffic. Moving the implicit deny from the bottom of the rule set to the top would make the deny rule more restrictive, which would not solve the issue. Configuring the first line in the rule set to allow all traffic would allow all traffic, including malicious traffic, which is not a good security practice.
Therefore, the best way to correct the issue is to ensure that port 53 has been explicitly allowed in the rule set. Here are some additional information about DNS traffic: DNS traffic is used to resolve domain names to IP addresses.
DNS traffic is used to resolve domain names to IP addresses. DNS traffic is typically unencrypted, which makes it vulnerable to eavesdropping.
DNS traffic is typically unencrypted, which makes it vulnerable to eavesdropping. There are a number of ways to secure DNS traffic, such as using DNS over HTTPS (DoH) or DNS over TLS (DoT).
There are a number of ways to secure DNS traffic, such as using DNS over HTTPS (DoH) or DNS over TLS (DoT).
NEW QUESTION 10
A systems administrator is required to enforce MFA for corporate email account access, relying on the possession factor. Which of the following authentication methods should the systems administrator choose? (Select two).
- A. passphrase
- B. Time-based one-time password
- C. Facial recognition
- D. Retina scan
- E. Hardware token
- F. Fingerprints
Answer: BE
Explanation:
Time-based one-time password (TOTP) and hardware token are authentication methods that rely on the possession factor, which means that the user must have a specific device or object in their possession to authenticate. A TOTP is a password that is valid for a short period of time and is generated by an app or a device that the user has. A hardware token is a physical device that displays a code or a password that the user can enter to authenticate. A passphrase (Option A) is a knowledge factor, while facial recognition (Option C), retina scan (Option D), and fingerprints (Option F) are all inherence factors.
https://ptgmedia.pearsoncmg.com/imprint_downloads/pearsonitcertification/bookreg/9780136798675/97801367 https://www.youtube.com/watch?v=yCJyPPvM-xg
NEW QUESTION 11
Which of the following disaster recovery tests is the LEAST time consuming for the disaster recovery team?
- A. Tabletop
- B. Parallel
- C. Full interruption
- D. Simulation
Answer: A
Explanation:
A tabletop exercise is a type of disaster recovery test that simulates a disaster scenario in a discussion-based format, without actually disrupting operations or requiring physical testing of recovery procedures. It is the least time-consuming type of test for the disaster recovery team.
NEW QUESTION 12
A major clothing company recently lost a large amount of proprietary information. The security officer must find a solution to ensure this never happens again.
Which of the following is the BEST technical implementation to prevent this from happening again?
- A. Configure DLP solutions
- B. Disable peer-to-peer sharing
- C. Enable role-based
- D. Mandate job rotation
- E. Implement content filters
Answer: A
Explanation:
Data loss prevention (DLP) solutions can prevent the accidental or intentional loss of sensitive data. DLP tools can identify and protect sensitive data by classifying and categorizing it, encrypting it, or blocking it from being transferred outside the organization's network.
NEW QUESTION 13
Which of the following would be used to find the most common web-applicalion vulnerabilities?
- A. OWASP
- B. MITRE ATT&CK
- C. Cyber Kill Chain
- D. SDLC
Answer: A
Explanation:
OWASP (Open Web Application Security Project) is a non-profit organization that provides resources and guidance for improving the security of web applications. It publishes a list of the most common web application vulnerabilities, such as injection, broken authentication, cross-site scripting, etc., and provides recommendations and best practices for preventing and mitigating them
NEW QUESTION 14
An organization experiences a cybersecurity incident involving a command-and-control server. Which of the following logs should be analyzed to identify the impacted host? (Select two).
- A. Application
- B. Authentication
- C. Error
- D. Network
- E. Firewall
- F. System
Answer: DE
Explanation:
Network and firewall logs should be analyzed to identify the impacted host in a cybersecurity incident involving a command-and-control server. A command-and-control server is a central server that communicates with and controls malware-infected devices or bots. A command-and-control server can send commands to the bots, such as downloading additional malware, stealing data, or launching attacks. Network logs can help to identify any suspicious or anomalous network traffic, such as connections to unknown or malicious domains, high-volume data transfers, or unusual protocols or ports. Firewall logs can help to identify any blocked or allowed traffic based on the firewall rules, such as connections to or from the command-and-control server, or any attempts to bypass the firewall. References: https://www.howtogeek.com/726136/what-is-a-command-and-control-server-for-malware/
https://www.howtogeek.com/726136/what-is-a-command-and-control-server-for-malware/
NEW QUESTION 15
A security manager needs to assess the security posture of one of the organization's vendors. The contract with the vendor does not allow for auditing of the vendor's security controls. Which of (he following should the manager request to complete the assessment?
- A. A service-level agreement
- B. A business partnership agreement
- C. A SOC 2 Type 2 report
- D. A memorandum of understanding
Answer: C
Explanation:
SOC 2 (Service Organization Control 2) is a type of audit report that evaluates the controls of service providers to verify their compliance with industry standards for security, availability, processing integrity, confidentiality, and privacy. A Type 2 report is based on an audit that tests the effectiveness of the controls over a period of time, unlike a Type 1 report which only evaluates the design of the controls at a specific point in time.
A SOC 2 Type 2 report would provide evidence of the vendor's security controls and how effective they are over time, which can help the security manager assess the vendor's security posture despite the vendor not allowing for a direct audit.
The security manager should request a SOC 2 Type 2 report to assess the security posture of the vendor. References: CompTIA Security+ Study Guide: Exam SY0-601, Chapter 5
NEW QUESTION 16
A company is concerned about individuals driving a car into the building to gain access. Which of the following security controls would work BEST to prevent this from happening?
- A. Bollard
- B. Camera
- C. Alarms
- D. Signage
- E. Access control vestibule
Answer: A
Explanation:
Bollards are posts designed to prevent vehicles from entering an area. They are usually made of steel or concrete and are placed close together to make it difficult for vehicles to pass through. In addition to preventing vehicles from entering an area, bollards can also be used to protect buildings and pedestrians from ramming attacks. They are an effective and cost-efficient way to protect buildings and pedestrians from unauthorized access.
NEW QUESTION 17
......
Recommend!! Get the Full SY0-701 dumps in VCE and PDF From 2passeasy, Welcome to Download: https://www.2passeasy.com/dumps/SY0-701/ (New 0 Q&As Version)