2026 New GSNA Exam Dumps with PDF and VCE Free: https://www.2passeasy.com/dumps/GSNA/
Certleader GSNA Questions are updated and all GSNA answers are verified by experts. Once you have completely prepared with our GSNA exam prep kits you will be ready for the real GSNA exam without a problem. We have Renewal GIAC GSNA dumps study guide. PASSED GSNA First attempt! Here What I Did.
Free demo questions for GIAC GSNA Exam Dumps Below:
NEW QUESTION 1
Mark works as a Network Administrator for We-are-secure Inc. He finds that the We-are- secure server has been infected with a virus. He presents to the company a report that describes the symptoms of the virus. A summary of the report is given below: This virus has a dual payload, as the first payload of the virus changes the first megabyte of the hard drive to zero. Due to this, the contents of the partition tables are deleted and the computer hangs. The second payload replaces the code of the flash BIOS with garbage values. This virus spreads under the Portable Executable File Format under Windows 95, Windows 98, and Windows ME. Which of the following viruses has the symptoms as the one described above?
- A. I Love You
- B. Nimda
- C. Chernobyl
- D. Melissa
Answer: C
Explanation:
The Chernobyl (CIH) virus is a good example of a dual payload virus. Since the first payload of the virus changes the first megabyte of a computer's hard drive to zero, the contents of the partition tables are deleted, resulting in the computer hanging. The second payload of CIH replaces the code of the flash BIOS with garbage values so that the flash BIOS is unable to give a warning, the end result being that the user is incapable of changing the BIOS settings. CIH spreads under the Portable Executable file format under Windows 95, Windows 98, and Windows ME.
Answer A is incorrect. The I LOVE YOU virus is a VBScript virus in which a victim gets an email attachment titled as "I Love You" with an attachment file named as "Love-Letter-For- You.txt.vbs". When the victim clicks on this attachment, the virus script infects the victim's computer. The virus first scans system's memory for passwords, which are sent back to the virus' creator. In the next step, the virus replicates itself and sends its copy to each address in the victim's Outlook address book. Finally, the virus corrupts files with extensions .vbs, .vbe, .js, .css, .wsh, .sct, .hta, .jpg, .jpeg, .mp2, and .mp3 by overwriting them with a copy of itself. Answer D is incorrect. The Melissa virus infects Word 97 documents and the NORMAL.DOT file of Word 97 and Word 2000. This macro virus resides in word documents containing one macro named as "Melissa". The Melissa virus has the ability to spread itself very fast by using an e-mail. When the document infected by the Melissa virus is opened for the first time, the virus checks whether or not the user has installed Outlook on the computer. If it finds the Outlook, it sends e-mail to 50 addresses from the address book of the Outlook. This virus can spread only by using the Outlook. This virus is also known as W97M/Melissa, Kwyjibo, and Word97.Meliss Answer B is incorrect. Nimda is a mass mailing virus that spreads itself in attachments named README.EXE. It affects Windows 95, 98, ME, NT4, and Windows 2000 users. Nimda uses the Unicode exploit to infect IIS Web servers.
NEW QUESTION 2
You have an online video library. You want to upload a directory of movies. Since this process will take several hours, you want to ensure that the process continues even after the terminal is shut down or session is closed. What will you do to accomplish the task?
- A. Use the bg command to run the process at the background.
- B. Add the nohup command in front of the process.
- C. Add the nohup command at the end of the process.
- D. Run the process inside a GNU Screen-style screen multiplexer.
Answer: BD
Explanation:
Whenever the nohup command is added in front of any command or process, it makes the command or process run even after the terminal is shut down or session is closed. All processes, except the 'at' and batch requests, are killed when a user logs out. If a user wants a background process to continue running even after he logs out, he must use the nohup command to submit that background command. To nohup running processes, press ctrl+z, enter "bg" and enter "disown". The other way to accomplish the task is to run the command/process inside a GNU Screen-style screen multiplexer, and then detach the screen. GNU Screen maintains the illusion that the user is always logged in, and allows the user to reattach at any time. This has the advantage of being able to continue to interact with the program once reattached (which is impossible with nohup alone). Answer C is incorrect. The nohup command works when it is added in front of a command. Answer A is incorrect. The bg command cannot run the command or process after the terminal is shut down or session is closed.
NEW QUESTION 3
You run the wc -c file1.txt command. If this command displays any error message, you want to store the error message in the error.txt file. Which of the following commands will you use to accomplish the task?
- A. wc -c file1.txt >>error.txt
- B. wc -c file1.txt 1>error.txt
- C. wc -c file1.txt 2>error.txt
- D. wc -c file1.txt >error.txt
Answer: C
Explanation:
According to the scenario, you will use the wc -c file1.txt 2>error.txt command to accomplish the task. The 2> operator is an error redirector, which, while running a command, redirects the error (if it exists) on the specified file. Answer B, D are incorrect. The > or 1> redirector can be used to redirect the output of the wc -c file1.txt file to the error.txt file; however, you want to write the errors in the error.txt file, not the whole output. Answer A is incorrect. The >> operator will redirect the output of the command in the same manner as the > or 1> operator. Although the >> operator will not overwrite the error.txt file, it will append the error.txt file.
NEW QUESTION 4
You work as the Network Administrator for XYZ CORP. The company has a Unix-based network. You want to identify the secure terminals from where the root can be allowed to log in. Which of the following Unix configuration files can you use to accomplish the task?
- A. /etc/services
- B. /etc/ioports
- C. /proc/interrupts
- D. /etc/securetty
Answer: D
Explanation:
In Unix, the /etc/securetty file is used to identify the secure terminals from where the root can be allowed to log in. Answer B is incorrect. In Unix, the /etc/ioports file shows which I/O ports are in use at the moment. Answer A is incorrect. In Unix, the /etc/services file is the configuration file that lists the network services that the system supports. Answer C is incorrect. In Unix, the /proc/interrupts file is the configuration file that shows the interrupts in use and how many of each there has been.
NEW QUESTION 5
You want to record auditing information in the SYS.AUD$ table, and also want to record SQL bind variables as well as the SQL text in the audit trail. Which of the following statements will accomplish this task?
- A. ALTER SYSTEM SET AUDIT_TRAIL = DB, XML SCOPE=SPFILE;
- B. ALTER SYSTEM SET AUDIT_TRAIL = 'DB, EXTENDED' SCOPE=SPFILE;
- C. ALTER SYSTEM SET AUDIT_TRAIL = 'DB','EXTENDED' SCOPE=SPFILE;
- D. ALTER SYSTEM SET AUDIT_TRAIL = DB, EXTENDED SCOPE=SPFILE;
- E. ALTER SYSTEM SET AUDIT_FILE_DEST = 'DB, EXTENDED' SCOPE=SPFILE;
- F. ALTER SYSTEM SET AUDIT_TRAIL = DB, EXTENDED SCOPE=BOTH;
Answer: CD
Explanation:
The initialization parameter AUDIT_TRAIL is used to specify the kind of auditing that needs to be performed, as well as the destination where it will be performed. There are three basic values for auditing that are DB, OS, and XML. Specifying DB sends all audit rows to the table SYS.AUD$, OS sends the audit rows to an operating system file, and XML sends the audit rows to an operating system file in the XML format. The location for external audit rows is specified by the AUDIT_FILE_DEST parameter. By adding the EXTENDED parameter for either DB or XML auditing, all SQL bind variables and the text of all SQL commands are included in the audit row. EXTENDED cannot be specified for OS auditing. In addition, NONE can be specified as the value for AUDIT_TRAIL, which will disable all auditing. Answer B is incorrect. DB, EXTENDED in single quotes cannot be specified when setting the AUDIT_TRAIL parameter. Answer E is incorrect. AUDIT_TRAIL must be set to specify the type of auditing. AUDIT_FILE_DEST is used to specify the operating system location for either OS or XML auditing. Answer A is incorrect. DB and XML auditing cannot be specified at the same time and the database must be restarted for the auditing change to go into effect.
NEW QUESTION 6
Which of the following is an attempt to give false information or to deny that a real event or transaction should have occurred?
- A. A DDoS attack
- B. A repudiation attack
- C. A reply attack
- D. A dictionary attack
Answer: B
Explanation:
A repudiation attack is an attempt to give false information or to deny that a real event or transaction should have occurred. Answer A is incorrect. In a distributed denial of service (DDOS) attack, an attacker uses multiple computers throughout the network that has been previously infected. Such computers act as zombies and work together to send out bogus messages, thereby increasing the amount of phony traffic. The major advantages to an attacker of using a distributed denial-of-service attack are that multiple machines can generate more attack traffic than one machine, multiple attack machines are harder to turn off than one attack machine, and that the behavior of each attack machine can be stealthier, making it harder to track down and shut down. TFN, TRIN00, etc. are tools used for a DDoS attack. Answer C is incorrect. A replay attack is a type of attack in which attackers capture packets containing passwords or digital signatures whenever packets pass between two hosts on a network. In an attempt to obtain an authenticated connection, the attackers then resend the captured packet to the system. In this type of attack, the attacker does not know the actual password, but can simply replay
the captured packet. Answer D is incorrect. Dictionary attack is a type of password guessing attack. This type of attack uses a dictionary of common words to find out the password of a user. It can also use common words in either upper or lower case to find a password. There are many programs available on the Internet to automate and execute dictionary attacks.
NEW QUESTION 7
You work as a Network Administrator for XYZ CORP. The company has a Windows Active Directory-based single domain single forest network. The functional level of the forest is Windows Server 2003. The company's management has decided to provide laptops to its sales team members. These laptops are equipped with smart card readers. The laptops will be configured as wireless network clients. You are required to accomplish the following tasks: The wireless network communication should be secured. The laptop users should be able to use smart cards for getting authenticated. In order to accomplish the tasks, you take the following steps: Configure 802.1x and WEP for the wireless connections. Configure the PEAP-MS-CHAP v2 protocol for authentication. What will happen after you have taken these steps?
- A. Both tasks will be accomplished.
- B. The laptop users will be able to use smart cards for getting authenticated.
- C. The wireless network communication will be secured.
- D. None of the tasks will be accomplished.
Answer: C
Explanation:
As 802.1x and WEP are configured, this step will enable the secure wireless network communication. For authentication, you have configured the PEAP-MS-CHAP v2 protocol. This protocol can be used for authentication on wireless networks, but it cannot use a public key infrastructure (PKI). No certificate can be issued without a PKI. Smart cards cannot be used for authentication without certificates. Hence, the laptop users will not be able to use smart cards for getting authenticated.
NEW QUESTION 8
In a network, a data packet is received by a router for transmitting it to another network. In order to make decisions on where the data packet should be forwarded, the router checks with its routing table. Which of the following lists does a router check in a routing table?
- A. Available networks
- B. Available packets
- C. Available protocols
- D. Available paths
Answer: AD
Explanation:
A Routing table stores the actual routes to all destinations; the routing table is populated from the topology table with every destination network that has its successor and optionally feasible successor identified (if unequal-cost load-balancing is enabled using the variance command). The successors and feasible successors serve as the next hop routers for these destinations. Unlike most other distance vector protocols, EIGRP does not rely on periodic route dumps in order to maintain its topology table. Routing information is exchanged only upon the establishment of new neighbor adjacencies, after which only changes are sent. Answer C is incorrect. A routing table does not contain any list of protocols. Answer B is incorrect. A routing table does not contain any list of packets.
NEW QUESTION 9
You are the security manager of Microliss Inc. Your enterprise uses a wireless network infrastructure with access points ranging 150-350 feet. The employees using the network complain that their passwords and important official information have been traced. You discover the following clues: The information has proved beneficial to an other company. The other company is located about 340 feet away from your office. The other company is also using wireless network. The bandwidth of your network has degraded to a great extent. Which of the following methods of attack has been used?
- A. A piggybacking attack has been performed.
- B. A DOS attack has been performed.
- C. The information is traced using Bluebugging.
- D. A worm has exported the information.
Answer: A
Explanation:
Piggybacking refers to access of a wireless Internet connection by bringing one's own computer within the range of another's wireless connection, and using that service without the subscriber's explicit permission or knowledge. It is a legally and ethically controversial practice, with laws that vary in jurisdictions around the world. While completely outlawed in some jurisdictions, it is permitted in others. The process of sending data along with the acknowledgment is called piggybacking. Answer C is incorrect. Bluebugging is an attack used only in a Bluetooth network. Bluebugging is a form of bluetooth attack often caused by a lack of awareness. Bluebugging tools allow attacker to "take control" of the victim's phone via the usage of the victim's Bluetooth phone headset. It does this by pretending to be the users bluetooth headset and therefore "tricking" the phone to obey its call commands. Answer D is incorrect. A worm is a software program that uses computer networks and security holes to replicate itself from one computer to another. It usually performs malicious actions, such as using the resources of computers as well as shutting down computers. Answer B is incorrect. A Denial-of-Service (DoS) attack is mounted with the objective of causing a negative impact on the performance of a computer or network. It is also known as a network saturation attack or bandwidth consumption attack. Attackers perform DoS attacks by sending a large number of protocol packets to the network. The effects of a DoS attack are as follows: Saturates network resources Disrupts connections between two computers, thereby preventing communications between services Disrupts services to a specific computer Causes failure to access a Web site Results in an increase in the amount of spam A Denial-of-Service attack is very common on the Internet because it is much easier to accomplish. Most of the DoS attacks rely on the weaknesses in the TCP/IP protocol.
NEW QUESTION 10
You work as the Network Administrator for XYZ CORP. The company has a Unix-based network. You want to do RARP mapping from hardware mapping addresses to IP addresses. Which of the following Unix configuration files can you use to accomplish the task?
- A. /etc/dhcpd.conf
- B. /etc/motd
- C. /etc/exports
- D. /etc/ethers
Answer: D
Explanation:
In Unix, the /etc/ethers file is used by system administrators for RARP mapping from hardware mapping addresses to IP addresses.
Answer A is incorrect. In Unix, the /etc/dhcpd.conf file is the configuration file for the DHCP server daemon. Answer C is incorrect. In Unix, the /etc/exports file describes exported file systems for NFS services. Answer B is incorrect. In Unix, the /etc/motd file automatically displays the message of the day after a successful login.
NEW QUESTION 11
You work as a Network Administrator for XYZ CORP. The company's Windows 2000 network is configured with Internet Security and Acceleration (ISA) Server 2000. ISA Server is configured as follows: The server uses the default site and content rule and default IP packet filters. Packet filtering is enabled. The server has two protocol rules: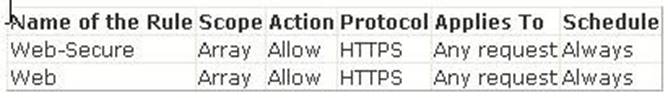
Users in the network complain that they are unable to access secure Web sites. However, they are able to connect to Web sites in which secure transmission is not required. What is the most likely cause?
- A. A protocol rule that allows the use of HTTP has not been created.
- B. An IP packet filter that allows the use of network traffic on port 80 has not been created.
- C. An IP packet filter that allows the use of network traffic on port 443 has not been created.
- D. A protocol rule that allows the use of HTTPS has not been created.
Answer: C
Explanation:
The default IP packet filter allows HTTP protocol (for non-secure communication) at port 80 to access the Internet. However, to allow users to access secure Web sites, you will have to create an additional packet filter to allow communication on port 443.
NEW QUESTION 12
Which of the following services are provided by the proxy servers?
- A. Intrusion detection
- B. Logging
- C. Hiding network resources
- D. Caching
Answer: BCD
Explanation:
A proxy server is a very important element for firewall applications. The services that it provides are as follows: Hide network resources: Proxy replaces the network IP address with a single IP address. Multiple systems can use a single IP address. Logging: A proxy server can log incoming and outgoing access, allowing a user to see every possible details of successful and failed connections. Cache: A proxy server can save information obtained from the Internet. It regularly updates these copies and automatically shows these pages, and will thus not need to access the Internet to view them.
NEW QUESTION 13
You work as a Network Auditor for XYZ CORP. The company has a Windows-based network. While auditing the company's network, you are facing problems in searching the faults and other entities that belong to it. Which of the following risks may occur due to the existence of these problems?
- A. Residual risk
- B. Inherent risk
- C. Secondary risk
- D. Detection risk
Answer: D
Explanation:
Detection risks are the risks that an auditor will not be able to find what they are looking to detect. Hence, it becomes tedious to report negative results when material conditions (faults) actually exist. Detection risk includes two types of risk: Sampling risk: This risk occurs when an auditor falsely accepts or erroneously rejects an audit sample. Nonsampling risk: This risk occurs when an auditor fails to detect a condition because of not applying the appropriate procedure or using procedures inconsistent with the audit objectives (detection faults). Answer A is incorrect. Residual risk is the risk or danger of an action or an event, a method or a (technical) process that, although being abreast with science, still conceives these dangers, even if all theoretically possible safety measures would be applied (scientifically conceivable measures). The formula to calculate residual risk is (inherent risk) x (control risk) where inherent risk is (threats vulnerability). In the economic context, residual means "the quantity left over at the end of a process; a remainder". Answer B is incorrect. Inherent risk, in auditing, is the risk that the account or section being audited is materially misstated without considering internal controls due to error or fraud. The assessment of inherent risk depends on the professional judgment of the auditor, and it is done after assessing the business environment of the entity being audited. Answer C is incorrect. A secondary risk is a risk that arises as a straight consequence of implementing a risk response. The secondary risk is an outcome of dealing with the original risk. Secondary risks are not as rigorous or important as primary risks, but can turn out to be so if not estimated and planned properly.
NEW QUESTION 14
You work as a Network Architect for Tech Perfect Inc. The company has a TCP/IP based Enterprise network. The company uses Cisco IOS technologies in the Enterprise network. You have enabled system message logging (syslog) service on all the routers that are currently working in the network. The syslog service provides all the reports, and important error and notification messages. You want to store all the reports and messages. Choose the locations where you can store all of these.
- A. Auxiliary
- B. Buffer
- C. Syslog server
- D. tty lines
- E. Console
Answer: BCDE
Explanation:
According to the scenario, you have enabled system message logging (syslog) service on all the routers that are currently working in the network. If you want to store all the repots, important error and notification messages sent by the routers, you can store all of these in the buffer, console, syslog server, and tty lines. You can use buffer, if you want to store syslog messages for later analysis of the network. Buffer is the memory of the router. The syslog messages that you have stored in the buffer are later available for the network analysis until the router is rebooted. You can use console port of the routers to send syslog messages to the attached terminal. You can also use vty and tty lines to send syslog messages to the remote terminal. However, the messages send through the console, vty, and tty lines are not later available for network analysis. You can use syslog server to store all the reports, and important error and notification messages. It is the best option to store all these because it is easy to configure a syslog server and you can store a large volume of logs. Note: If you have configured to run an SNMP agent, the routers send all the reports, and important error and messages in the form of SNMP traps to an SNMP server. Using this you can store the reports and messages for a long period of time. Answer A is incorrect. You cannot store syslog messages in the auxiliary line.
NEW QUESTION 15
You work as a Network Administrator for XYZ CORP. The company has a Windows-based network. You want to configure the ACL with a Cisco router. Which of the following router prompts can you use to accomplish the task?
- A. router(config-if)#
- B. router(config)#
- C. router(config-ext-nacl)#
- D. router#
Answer: C
Explanation:
The auditor of a Cisco router should be familiar with the variety of privilege modes. The current privilege mode can be quickly identified by looking at the current router prompt. The prime modes of a Cisco router are as follows: #Nonprivileged mode: router>
#Priviledged mode: router# #Global configuration mode: router(config)# #Interface configuration mode: router(config-if)# #ACL configuration mode: router(config-ext-nacl)#
#Boot loader mode: router(boot) #Remote connectivity config mode: router(config-line)#
NEW QUESTION 16
Which of the following does an anti-virus program update regularly from its manufacturer's Web site?
- A. Hotfixes
- B. Permissions
- C. Service packs
- D. Definition
Answer: D
Explanation:
An anti-virus program updates the virus definition file regularly from the anti- virus manufacturer's Web site. Antivirus (or anti-virus) software is used to prevent, detect, and remove malware, including computer viruses, worms, and trojan horses. Such programs may also prevent and remove adware, spyware, and other forms of malware. Traditional antivirus software solutions run virus scanners on schedule, on demand and some run scans in real time. If a virus or malware is located, the suspect file is usually placed into a quarantine to terminate its chances of disrupting the system. Traditional antivirus solutions scan and compare against a publicized and regularly updated dictionary of malware otherwise known as a blacklist. Some antivirus solutions have additional options that employ a heuristic engine which further examines the file to see if it is behaving in a similar manner to previous examples of malware. A new technology utilized by a few antivirus solutions is whitelisting; this technology first checks if the file is trusted and only questions those that are not. With the addition of wisdom of crowds, antivirus solutions backup other antivirus techniques by harnessing the intelligence and advice of a community of trusted users to protect each other. Answer C is incorrect. A service pack is a collection of Fixes and Patches in a single product. A service pack can be used to handle a large number of viruses and bugs or to update an operating system with advanceB, Detter capabilities. A service pack usually contains a number of file replacements. Answer A is incorrect. Hotfix is a collection of files used by Microsoft for software updates that are released between major service pack releases. A hotfix is about a problem, occurring under specific circumstances, which cannot wait to be fixed till the next service pack release. Hotfixes are generally related to security problems. Hence, it is essential to fix these problems as soon as possible. Answer B is incorrect. An anti-virus program does not update Permissions regularly from its manufacturer's Web site.
NEW QUESTION 17
You work as a Network Administrator for XYZ CORP. The company has a Linux-based network. You need to configure a firewall for the company. The firewall should be able to keep track of the state of network connections traveling across the network. Which of the following types of firewalls will you configure to accomplish the task?
- A. A network-based application layer firewall
- B. Host-based application firewall
- C. An application firewall
- D. Stateful firewall
Answer: D
Explanation:
A stateful firewall is a firewall that keeps track of the state of network connections (such as TCP streams, UDP communication) traveling across it. The firewall is programmed to distinguish legitimate packets for different types of connections. Only packets matching a known connection state will be allowed by the firewall; others will be rejected. Answer B is incorrect. A host-based application firewall can monitor any application input, output, and/or system service calls made from, to, or by an application. This is done by examining information passed through system calls instead of, or in addition to, a network stack. A host-based application firewall can only provide protection to the applications running on the same host. An example of a host-based application firewall that controls system service calls by an application is AppArmor or the Mac OS X application firewall. Host-based application firewalls may also provide network-based application firewalling. Answer A is incorrect. A network-based application layer firewall, also known as a proxy-based or reverse-proxy firewall, is a computer networking firewall that operates at the application layer of a protocol stack. Application firewalls specific to a particular kind of network traffic may be titled with the service name, such as a Web application firewall. They may be implemented through software running on a host or a stand-alone piece of network hardware. Often, it is a host using various forms of proxy servers to proxy traffic before passing it on to the client or server. Because it acts on the application layer, it may inspect the contents of the traffic, blocking specified content, such as certain websites, viruses, and attempts to exploit known logical flaws in client software. Answer C is incorrect. An application firewall is a form of firewall that controls input, output, and/or access from, to, or by an application or service. It operates by monitoring and potentially blocking the input, output, or system service calls that do not meet the configured policy of the firewall. The application firewall is typically built to monitor one or more specific applications or services (such as a web or database service), unlike a stateful network firewall, which can provide some access controls for nearly any kind of network traffic. There are two primary categories of application firewalls: Network-based application firewalls Host-based application firewalls
NEW QUESTION 18
......
Recommend!! Get the Full GSNA dumps in VCE and PDF From Surepassexam, Welcome to Download: https://www.surepassexam.com/GSNA-exam-dumps.html (New 368 Q&As Version)