2026 New GSNA Exam Dumps with PDF and VCE Free: https://www.2passeasy.com/dumps/GSNA/
It is more faster and easier to pass the GIAC GSNA exam by using Download GIAC GIAC Systems and Network Auditor questuins and answers. Immediate access to the Renewal GSNA Exam and find the same core area GSNA questions with professionally verified answers, then PASS your exam with a high score now.
Free demo questions for GIAC GSNA Exam Dumps Below:
NEW QUESTION 1
John works as a professional Ethical Hacker. He is assigned a project to test the security of www.we-are-secure.com. He is working on the Linux operating system. He wants to sniff the we-are-secure network and intercept a conversation between two employees of the company through session hijacking. Which of the following tools will John use to accomplish the task?
- A. IPChains
- B. Tripwire
- C. Hunt
- D. Ethercap
Answer: C
Explanation:
In such a scenario, John will use Hunt which is capable of performing both the hacking techniques, sniffing and session hijacking. Answer D is incorrect. Ethercap is a network sniffer and packet generator. It may be an option, but John wants to do session hijacking as well. Hence, he will not use Ethercap. Answer A is incorrect. IPChains is a firewall. Answer B is incorrect. Tripwire is a file and directory integrity checker.
NEW QUESTION 2
You work as a Software Developer for UcTech Inc. You are building a Web site that will contain study materials on the Java language. The company wants that members can
access all the pages, but non-members have only limited access to the Web site pages. Which of the following security mechanisms will you use to accomplish the task?
- A. Data integrity
- B. Authentication
- C. Confidentiality
- D. Authorization
Answer: D
Explanation:
Authorization is a process that verifies whether a user has permission to access a Web resource. A Web server can restrict access to some of its resources to only those clients that log in using a recognized username and password. To be authorized, a user must first be authenticated. Answer B is incorrect. Authentication is the process of verifying the identity of a user. This is usually done using a user name and password. This process compares the provided user name and password with those stored in the database of an authentication server. Answer C is incorrect. Confidentiality is a mechanism that ensures that only the intended and authorized recipients are able to read data. The data is so encrypted that even if an unauthorized user gets access to it, he will not get any meaning out of it. Answer A is incorrect. Data integrity is a mechanism that ensures that the data is not modified during transmission from source to destination. This means that the data received at the destination should be exactly the same as that sent from the source.
NEW QUESTION 3
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He is using the Linux operating system. He wants to use a wireless sniffer to sniff the We-are-secure network. Which of the following tools will he use to accomplish his task?
- A. WEPCrack
- B. Kismet
- C. Snadboy's Revelation
- D. NetStumbler
Answer: B
Explanation:
According to the scenario, John will use Kismet. Kismet is a Linux-based 802.11 wireless network sniffer and intrusion detection system. It can work with any wireless card that supports raw monitoring (rfmon) mode. Kismet can sniff 802.11b, 802.11a, 802.11g, and 802.11n traffic. Kismet can be used for the following tasks: To identify networks by passively collecting packets To detect standard named networks To detect masked networks
To collect the presence of non-beaconing networks via data traffic Answer D is incorrect. NetStumbler is a Windows-based tool that is used for the detection of wireless LANs using the IEEE 802.11a, 802.11b, and 802.11g standards. It detects wireless networks and marks their relative position with a GPS. Answer A is incorrect. WEPCrack is an open source tool that breaks IEEE 802.11 WEP secret keys. Answer C is incorrect. Snadboy's Revelation is not a sniffer. It is used to see the actual password behind the asterisks.
NEW QUESTION 4
Mark is an attacker. He wants to discover wireless LANs by listening to beacons or sending probe requests and thereby provide a launch point for further attacks. Which of the following tools can he use to accomplish the task?
- A. DStumbler
- B. Wellenreiter
- C. KisMAC
- D. Airmon-ng
Answer: ACD
Explanation:
War driving is an attack in which the attacker discovers wireless LANs by listening to beacons or sending probe requests, thereby providing a launch point for further attacks. Airmon-ng, DStumbler, KisMAC, MacStumbler, NetStumbler, Wellenreiter, and WiFiFoFum are the tools that can be used to perform a war driving attack. Answer B is incorrect. Wellenreiter is a tool that is used to perform MAC spoofing attacks.
NEW QUESTION 5
You work as a Security manager for Qualoxizz Inc. Your company has number of network switches in the site network infrastructure. Which of the following actions will you perform to ensure the security of the switches in your company?
- A. Open up all the unused management ports.
- B. Set similar passwords for each management port.
- C. Set long session timeouts.
- D. Ignore usage of the default account settings.
Answer: D
Explanation:
A switch with a management port using a default user account permits an attacker to intrude inside by making connections using one or more of the well-known default user accounts (e.g., administrator, root, security). Therefore, the default account settings should not be used. Answer A is incorrect. The unused management ports on a switch should always be blocked to prevent port scanning attacks from the attackers. Answer B is incorrect. Setting similar passwords on all management ports increases the vulnerability of password cracking. The matching passwords on all ports can be used by the attacker to break into all ports once the password of one of the ports is known. Answer C is incorrect. Short timeout sessions should always be set to reduce the session period. If the connections to a management port on a switch do not have a timeout period set or have a large timeout period (greater than 9 minutes), then the connections will be more available for an attacker to hijack them.
NEW QUESTION 6
Adam works as a Security Analyst for Umbrella Inc. He is retrieving large amount of log data from syslog servers and network devices such as Router and switches. He is facing difficulty in analyzing the logs that he has retrieved. To solve this problem, Adam decides to use software called Sawmill. Which of the following statements are true about Sawmill?
- A. It incorporates real-time reporting and real-time alerting.
- B. It is used to analyze any device or software package, which produces a log file such as Web servers, network devices (switches & routers etc.), syslog servers etc.
- C. It is a software package for the statistical analysis and reporting of log files.
- D. It comes only as a software package for user deployment.
Answer: ABC
Explanation:
Sawmill is a software package for the statistical analysis and reporting of log files, with dynamic contextual filtering, 'live' data zooming, user interface customization, and custom calculated reports. Sawmill incorporates real-time reporting and real-time alerting. Sawmill also includes a page tagging server and JavaScript page tag for the analysis of client side
clicks (client requests) providing a total view of visitor traffic and on-site behavioral activity. Sawmill Analytics is offered in three forms, as a software package for user deployment, as a turnkey on-premise system appliance, and as a SaaS service. Sawmill analyzes any device or software package producing a log file and that includes Web servers, firewalls, proxy servers, mail servers, network devices (switches & routers etc.), syslog servers, databases etc. Its range of potential uses by knowledge workers is essentially limitless. Answer D is incorrect. Sawmill Analytics software is available in three different forms; as a software package for user deployment, as a turnkey on-premise system appliance, and as a SaaS service.
NEW QUESTION 7
Peter works as a Web Developer for XYZ CORP. He is developing a Web site for the company. In one of the Web pages, Peter wants to ensure that certain information is consistent and visible while the other information changes. Which of the following will he use to accomplish this?
- A. Tables
- B. Navigation links
- C. Data elements
- D. Frames
Answer: D
Explanation:
Peter will use frames in the Web page. Frames are extensions of the HTML 3.2 standard introduced by Netscape. Elements such as navigation links and title graphic, can be placed in static individual frames. The <frame> tag defines the contents that will appear in each frame. It is used within the <frameset> tag. Frames allow users to display multiple HTML files at a time. Answer A is incorrect. A table is used to handle data in tabular form. Answer B is incorrect. Navigation links are used with the navigation bar to display a page. These hyperlinks are relative to the navigational structure of a Web site. Answer C is incorrect. Data elements are used to access data in XML format from a Web server.
NEW QUESTION 8
You work as a Network Administrator for XYZ CORP. The company has a Windows Server 2008 network environment. The network is configured as a Windows Active Directory- based single forest single domain network. You have installed a Windows Server 2008 computer as the domain controller. The client computers of the company use the Windows XP Professional operating system. When a user logs on to a client computer, it gets authenticated by the domain controller. You want to audit the logon events that would be generated on the domain controller. Which of the following audit settings do you need to configure to accomplish the task?
- A. Audit account management
- B. Audit logon events
- C. Audit directory service access
- D. Audit account logon events
Answer: D
Explanation:
'Audit account logon events' is one of the nine audit settings that can be configured on a Windows computer. This performs auditing whenever a user logs on or off from a different computer in which the computer performing the auditing is used for validating the account, for example, when a user logs on to a Windows XP Professional computer, but gets authenticated by a domain controller. The event would be generated on the domain controller, as it is actually being used for validating the user. Answer A is incorrect. Audit account management is one of the nine audit settings that can be configured on a Windows computer. This option is enabled to audit each event that is related to a user managing an account in the user database on the computer where the auditing is configured. These events include the following: Creating a user account Adding a user account to a group Renaming a user account Changing password for a user account This option is also used to audit the changes to the domain account of the domain controllers. Answer C is incorrect. The 'Audit directory service access' option is enabled to capture the events that are related to the users accessing the Active Directory object which has been configured to track user access through the System Access Control List (SACL) of the object. Answer B is incorrect. The 'Audit logon events' option is enabled to audit each event that is related to a user logging on to, logging off from, or making a network connection to the computer configured to audit logon events.
NEW QUESTION 9
Which of the following tools can be used by a user to hide his identity?
- A. War dialer
- B. IPchains
- C. Proxy server
- D. Rootkit
- E. Anonymizer
Answer: BCE
Explanation:
A user can hide his identity using any firewall (such as IPChains), a proxy server, or an anonymizer.
NEW QUESTION 10
You work as a Network Administrator for XYZ CORP. The company has a TCP/IP-based network environment. The network contains Cisco switches and a Cisco router. A user is unable to access the Internet from Host B. You also verify that Host B is not able to connect to other resources on the network. The IP configuration of Host B is shown below: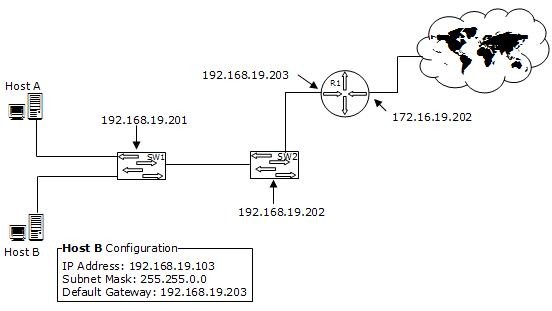
Which of the following is the most likely cause of the issue?
- A. An incorrect subnet mask is configured on Host B.
- B. The IP address of Host B is not from the correct IP address range of the network.
- C. There is an IP address conflict on the network.
- D. An incorrect default gateway is configured on Host B.
Answer: A
Explanation:
According to the network diagram, the IP address range used on the network is from the class C private address range. The class C IP address uses the following default subnet mask: 255.255.255.0 The question specifies that the subnet mask used in Host B is 255.255.0.0, which is an incorrect subnet mask.
NEW QUESTION 11
Which of the following wireless security standards supported by Windows Vista provides the highest level of security?
- A. WPA-EAP
- B. WEP
- C. WPA-PSK
- D. WPA2
Answer: D
Explanation:
WPA2 is an updated version of WPA. This standard is also known as IEEE 802.11i. WPA2 offers enhanced protection to wireless networks than WPA and WEP standards. It is also available as WPA2-PSK and WPA2-EAP for home and enterprise environment respectively. Answer B is incorrect. than WEP (Wired Equivalent Protection).
Windows Vista supports both WPA-PSK and WPA-EAP. Each of these is described as follows: WPA-PSK: PSK stands for Preshared key. This standard is meant for home environment. WPA-PSK requires a user to enter an 8- character to 63-character passphrase into a wireless client. The WPA converts the passphrase into a 256-bit key. WPA-EAP: EAP stands for Extensible Authentication Protocol. This standard relies on a back-end server that runs Remote Authentication Dial-In User Service for user authentication. Note: Windows Vista supports a user to use a smart card to connect to a WPA-EAP protected network.
NEW QUESTION 12
Which of the following is required by a Web-based application to connect to a database?
- A. DSN
- B. DNS
- C. CGI
- D. FQDN
Answer: A
Explanation:
A Web-based application uses Data Source Name (DSN) to connect to a database. DSN is a logical name used by Open Database Connectivity (ODBC) to refer to connection information required to access dat Answer C is incorrect. The Common Gateway Interface (CGI) specification is used for creating executable programs that run on a Web server. CGI defines the communication link between a Web server and Web applications. It gives a network or Internet resource access to specific programs. For example, when users submit an HTML form on a Web site, CGI is used to pass this information to a remote application for processing, and retrieve the results from the application. It then returns these results to the user by means of an HTML page. Answer D is incorrect. Fully Qualified Domain Name (FQDN) is a unique name of a host or computer, which represents its position in the hierarchy. An FQDN begins with a host name and ends with the top-level domain name. FQDN includes the second-level domain and other lower level domains. For example, the FQDN of the address HTTP://WWW.UNI.ORG will be WWW.UNI.ORG where WWW is the host name, UNI is the second-level domain, and ORG is the top-level domain name. Answer B is incorrect. Domain Name System (DNS) is a hierarchical naming system used for locating domain names on private TCP/IP networks and the Internet. It provides a service for mapping DNS domain names to IP addresses and vice versa. DNS enables users to use friendly names to locate computers and other resources on an IP network. TCP/IP uses IP addresses to locate and connect to hosts, but for users, it is easier to use names instead of IP address to locate or connect to a site. For example, users will be more comfortable in using the host name www.uCertify.com rather than using its IP address 66.111.64.227.
NEW QUESTION 13
You work as a programmer for uCertify.Inc. You have a session object named session1 with an attribute named Attribute1, and an HttpSessionBindingEvent object binding1 bound to session1. Which of the following will be used to retrieve Attribute1?
- A. Object obj=binding1.getSession().getAttribute("Attribute1");
- B. Object obj=binding1.getAttribute("Attribute1");
- C. Long MyAttribute=session1.getAttribute("Attribute1");
- D. Object obj=session1.getAttribute("Attribute1");
- E. String str1=session1.getAttribute("Attribute1");
Answer: AD
Explanation:
The following two code are used to retrieve Attribute1: 1.Object obj=session1.getAttribute("Attribute1"); The getAttribute() method is used to retrieve the bound object with the specified name in this session, or null if no object is bound under the name. 2.Object obj=binding1.getSession().getAttribute("Attribute1"); The getSession() gets the current valid session associated with this request. a String object. Answer B is incorrect. The HttpSessionBindingEvent object cannot use the getAttribute() method.
NEW QUESTION 14
Mark implements a Cisco unified wireless network for Tech Perfect Inc. Which functional area of the Cisco unified wireless network architecture includes intrusion detection and prevention?
- A. Network services
- B. Wireless clients
- C. Network unification
- D. Wireless access points
Answer: A
Explanation:
Network services is the last functional area of the Cisco unified wireless network architecture. This functional area includes the self-depending network, enhanced network support, such as location services, intrusion detection and prevention, firewalls, network admission control, and all other services. Answer C is incorrect. Network unification is a functional area of the Cisco unified wireless network architecture. This functional area includes the following wireless LAN controllers: 1.The 6500 series catalyst switch 2.Wireless services module (WiSM) 3.Cisco wireless LAN controller module (WLCM) 4.Cisco catalyst 3750 series integrated WLC 5.Cisco 4400 series WLC 6.Cisco 2000 series WLC Answer B is incorrect. Wireless clients is a functional area of the Cisco unified wireless network. The client devices are connected to a user. Answer D is incorrect. A wireless access point (WAP) is a device that allows wireless communication devices to connect to a wireless network using Wi-Fi, Bluetooth, or related standards. The WAP usually connects to a wired network, and it can transmit data between wireless devices and wired devices on the network. Each access point can serve multiple users within a defined network area. As people move beyond the range of one access point, they are automatically handed over to the next one. A small WLAN requires a single access point. The number of access points in a network depends on the number of network users and the physical size of the network.
NEW QUESTION 15
You check performance logs and note that there has been a recent dramatic increase in the amount of broadcast traffic. What is this most likely to be an indicator of?
- A. Misconfigured router
- B. DoS attack
- C. Syn flood
- D. Virus
Answer: B
Explanation:
There are several denial of service (DoS) attacks that specifically use broadcast traffic to flood a targeted computer. Seeing an unexplained spike in broadcast traffic could be an indicator of an attempted denial of service attack. Answer D is incorrect. Viruses can cause an increase in network traffic, and it is possible for that to be broadcast traffic. However, a DoS attack is more likely than a virus to cause this particular problem. Answer C is incorrect. A syn flood does not cause increased broadcast traffic. Answer A is incorrect. A misconfigured router could possibly cause an increase in broadcast traffic. However, this a recent problem, the router is unlikely to be the issue.
NEW QUESTION 16
John works as a Network Administrator for Perfect Solutions Inc. The company has a Linux-based network. John is working as a root user on the Linux operating system. He wants to break a dat a.txt file, 200MB in size, into two files in which the size of the first file named data.txt.aa should be 150MB and that of the second file named data.txt.ab should be 50MB. To accomplish his task and to further delete the data.txt file, he enters the following command: split --verbose -b 150m data.txt data.txt. ; rm -vf data.txt Which of the following commands can John use to join the splitted files into a new data.txt file?
- A. vi data.txt.* > data.txt
- B. less data.txt.* > data.txt
- C. vi data.txt.*
- D. cat data.txt.* > data.txt
Answer: D
Explanation:
The cat data.txt.* command will display both the splitted files, and the > command will redirect the output into a new data.txt file.
NEW QUESTION 17
You work as the Network Technician for XYZ CORP. The company has a Linux-based network. You are working on the Red Hat operating system. You want to view only the last 4 lines of a file named /var/log/cron. Which of the following commands should you use to accomplish the task?
- A. tail -n 4 /var/log/cron
- B. tail /var/log/cron
- C. cat /var/log/cron
- D. head /var/log/cron
Answer: A
Explanation:
The tail -n 4 /var/log/cron command will show the last four lines of the file /var/log/cron.
NEW QUESTION 18
......
P.S. Easily pass GSNA Exam with 368 Q&As 2passeasy Dumps & pdf Version, Welcome to Download the Newest 2passeasy GSNA Dumps: https://www.2passeasy.com/dumps/GSNA/ (368 New Questions)