2026 New GSNA Exam Dumps with PDF and VCE Free: https://www.2passeasy.com/dumps/GSNA/
It is impossible to pass GIAC GSNA exam without any help in the short term. Come to Actualtests soon and find the most advanced, correct and guaranteed GIAC GSNA practice questions. You will get a surprising result by our Rebirth GIAC Systems and Network Auditor practice guides.
Check GSNA free dumps before getting the full version:
NEW QUESTION 1
Which of the following mechanisms is closely related to authorization?
- A. Sending secret data such as credit card information.
- B. Allowing access to a particular resource.
- C. Verifying username and password.
- D. Sending data so that no one can alter it on the way.
Answer: B
Explanation:
Authorization is a process that verifies whether a user has permission to access a Web resource. A Web server can restrict access to some of its resources to only those clients that log in using a recognized username and password. To be authorized, a user must first be authenticated. Answer C is incorrect. Verifying username and password describes the mechanism of authentication. Authentication is the process of verifying the identity of a user. This is usually done using a user name and password. This process compares the provided user name and password with those stored in the database of an authentication server. Answer D is incorrect. Sending data so that no one can alter it on the way describes the mechanism of data integrity. Data integrity is a mechanism that ensures that the data is not modified during transmission from source to destination. This means that the data received at the destination should be exactly the same as that sent from the source. Answer A is incorrect. Sending secret data such as credit card information describes the mechanism of confidentiality. Confidentiality is a mechanism that ensures that only the intendeA, Duthorized recipients are able to read data. The data is so encrypted that even if an unauthorized user gets access to it, he will not get any meaning out of it.
NEW QUESTION 2
John works as a Network Administrator for Perfect Solutions Inc. The company has a
Linux-based network. John is working as a root user on the Linux operating system. He has a data.txt file in which each column is separated by the TAB character. Now, he wants to use this file as input for a data mining software he has created. The problem preventing him from accomplishing his task is that with his data mining software, he has used TAB as a delimiter to distinguish between columns. Hence, he is unable to use this file as input for the software. However, if he somehow replaces the TAB characters of the file with SPACE characters, he can use this file as an input file for his data mining software. Which of the following commands will John use to replace the TAB characters of the file with SPACE characters?
- A. expand -t 1 data.txt > data.txt
- B. cat data.txt
- C. chmod 755 data.txt
- D. touch data.txt
Answer: A
Explanation:
According to the scenario, John can replace the TAB characters with single space characters with the expand command. With the expand -t 1 data.txt > data.txt command, the TABs of data.txt are changed into single spaces and are redirected by using the > command into the data.txt file. Now, John can use the data.txt file as the input file for his data mining software.
NEW QUESTION 3
You work as a Desktop Support Technician for XYZ CORP. The company uses a Windows-based network comprising 50 Windows XP Professional computers. You want to
include the Safe Mode with Command Prompt feature into the boot.ini file of a Windows XP Professional computer. Which of the following switches will you use?
- A. /safeboot:network /sos /bootlog /noguiboot
- B. /safeboot:minimal /sos /bootlog /noguiboot
- C. /safeboot:minimal(alternateshell) /sos /bootlog /noguiboot
- D. /safeboot:dsrepair /sos
Answer: C
Explanation:
Safe-mode boot switches are used in the Windows operating systems to use the afe-mode boot feature. To use this feature the user should press F8 during boot. These modes are available in the Boot.ini file. Users can also automate the boot process using this feature. Various switches used for various modes are given below:
NEW QUESTION 4
Which of the following methods can be helpful to eliminate social engineering threat? (Choose three)
- A. Data encryption
- B. Data classification
- C. Password policies
- D. Vulnerability assessments
Answer: BCD
Explanation:
The following methods can be helpful to eliminate social engineering threat: Password policies Vulnerability assessments Data classification Password policy should specify that how the password can be shared. Company should implement periodic penetration and vulnerability assessments. These assessments usually consist of using known hacker tools and common hacker techniques to breach a network security. Social engineering should also be used for an accurate assessment. Since social engineers use the knowledge of others to attain information, it is essential to have a data classification model in place that all employees know and follow. Data classification assigns level of sensitivity of company information. Each classification level specifies that who can view and edit data, and how it can be shared.
NEW QUESTION 5
Which of the following are the disadvantages of Dual-Homed Host Firewall Architecture?
- A. It can provide services by proxying them.
- B. It can provide a very low level of control.
- C. User accounts may unexpectedly enable services a user may not consider secure.
- D. It provides services when users log on to the dual-homed host directly.
Answer: ACD
Explanation:
A dual-homed host is one of the firewall architectures for implementing preventive security. It provides the first-line defense and protection technology for keeping untrusted bodies from compromising information security by violating trusted network space as shown in the image below: A dual-homed host (or bastion host) is a system fortified with two network interfaces (NICs) that sits between an un-trusted network (like the Internet) and trusted network (such as a corporate network) to provide secure access. Dual-homed, or bastion, is a general term for proxies, gateways, firewalls, or any server that provides secured applications or services directly to an untrusted network.
A dual-homed host also has some disadvantages, which are as follows:
* 1. It can provide services by proxying them.
* 2. User accounts may unexpectedly enable services a user may not consider secure.
* 3. It provides services when users log on to the dual-homed host directly.
Answer B is incorrect. Dual-Homed Host Firewall Architecture can provide a very high level of control.
NEW QUESTION 6
Which of the following Web attacks is performed by manipulating codes of programming languages such as SQL, Perl, Java present in the Web pages?
- A. Command injection attack
- B. Code injection attack
- C. Cross-Site Scripting attack
- D. Cross-Site Request Forgery
Answer: B
Explanation:
A code injection attack exists whenever a scripting or programming language is used in a Web page. All that the attacker needs is an error or opening. That opening usually comes in the form of an input field that is not validated correctly. It is not necessary for the code injection attack to be on the Web page. It can be located in the back end as part of a database query of the Web site. If any part of the server uses Java, JavaScript, C, SQL, or any other code between the Internet and the data, it is vulnerable to the code injection attack.
Answer C is incorrect. A cross site scripting attack is one in which an attacker enters malicious data into a Website. For example, the attacker posts a message that contains malicious code to any newsgroup site. When another user views this message, the browser interprets this code and executes it and, as a result, the attacker is able to take control of the user's system. Cross site scripting attacks require the execution of client-side languages such as JavaScript, Java, VBScript, ActiveX, Flash, etc. within a user's Web environment. With the help of a cross site scripting attack, the attacker can perform cookie stealing, sessions hijacking, etc. Answer A is incorrect. A command injection attack is used to inject and execute commands specified by the attacker in the vulnerable application. The application, which executes unwanted system commands, is like a virtual system shell. The attacker may use it as any authorized system user. However, commands are executed with the same privileges and environment as the application has. The command injection attacks are possible in most cases because of lack of correct input data validation, which can be manipulated by the attacker. Answer D is incorrect. Cross-site request forgery, also known as one-click attack or session riding, is a type of malicious exploit of a website whereby unauthorized commands are transmitted from a user that the website trusts. Unlike cross-site scripting (XSS), which exploits the trust a user has for a particular site, CSRF exploits the trust that a site has in a user's browser. The attack works by including a link or script in a page that accesses a site to which the user is known to have authenticated.
NEW QUESTION 7
In which of the following does a Web site store information such as user preferences to provide customized services to users?
- A. Protocol
- B. ActiveX control
- C. Cookie
- D. Keyword
Answer: C
Explanation:
A cookie is a small bit of text that accompanies requests and pages as they move between Web servers and browsers. It contains information that is read by a Web application, whenever a user visits a site. Cookies are stored in the memory or hard disk of client computers. A Web site stores information, such as user preferences and settings in a cookie. This information helps in providing customized services to users. There is absolutely no way a Web server can access any private information about a user or his computer through cookies, unless a user provides the information. A Web server cannot access cookies created by other Web servers.
Answer A is incorrect. A protocol is a set of predefined rules that govern how two or more processes communicate and interact to exchange data. Protocols are considered as the building blocks of network communication. Computer protocols are used by communicating
devices and software services to format data in a way that all participants understand. It provides a context in which to interpret communicated information. Answer B is incorrect. ActiveX controls are software components that can be integrated into Web pages and applications, within a computer or among computers in a network, to reuse the functionality. Reusability of controls reduces development time of applications and improves program interfaces. They enhance the Web pages with formatting features and animation. ActiveX controls can be used in applications written in different programming languages that recognize Microsoft's Component Object Model (COM). These controls always run in a container. ActiveX controls simplify and automate the authoring tasks, display data, and add functionality to Web pages. Answer D is incorrect. Keywords are important terms used to search Web pages on a particular topic. For example, if a user enters a keyword "Networking" in a search engine form, all Web pages containing the term "Networking" will be displayed.
NEW QUESTION 8
Which of the following statements about a session are true? (Choose two)
- A. The creation time can be obtained using the getSessionCreationTime() method of the HttpSession.
- B. The getAttribute() method of the HttpSession interface returns a String.
- C. The time for the setMaxInactiveInterval() method of the HttpSession interface is specified in seconds.
- D. The isNew() method is used to identify if the session is new.
Answer: CD
Explanation:
The setMaxInactiveInterval() method sets the maximum time in seconds before a session becomes invalid. The syntax of this method is as follows: public void
setMaxInactiveInterval(int interval) Here, interval is specified in seconds. The isNew() method of the HttpSession interface returns true if the client does not yet know about the session, or if the client chooses not to join the session. This method throws an IllegalStateException if called on an invalidated session. Answer B is incorrect. The getAttribute(String name) method of the HttpSession interface returns the value of the named attribute as an object. It returns a null value if no attribute with the given name is bound to the session. This method throws an IllegalStateException if it is called on an invalidated session. Answer A is incorrect. The creation time of a session can be obtained using the getCreationTime() method of the HttpSession.
NEW QUESTION 9
You work as a Database Administrator for XYZ CORP. The company has a multi-platform network. The company requires a database that can receive data from various types of operating systems. You want to design a multidimensional database to accomplish the task. Which of the following statements are true about a multidimensional database?
- A. It is used to optimize Online Analytical Processing (OLAP) applications.
- B. It is used to optimize data warehouse.
- C. It is rarely created using input from existing relational databases.
- D. It allows users to ask questions that are related to summarizing business operations and trends.
Answer: ABD
Explanation:
A multidimensional database (MDB) is a type of database that is optimized for data warehouse and Online Analytical Processing (OLAP) applications. Multidimensional databases are frequently created using input from existing relational databases. Whereas a relational database is typically accessed using a Structured Query Language (SQL) query, a multidimensional database allows a user to ask questions like "How many Aptivas have been sold in Nebraska so far this year?" and similar questions related to summarizing business operations and trends. An OLAP application that accesses data from a multidimensional database is known as a MOLAP (multidimensional OLAP) application. Answer C is incorrect. A multidimensional database is frequently created using input from existing relational databases.
NEW QUESTION 10
On which of the following does a CGI program execute?
- A. Router
- B. Web server
- C. Client
- D. Client and Web server
Answer: B
Explanation:
The Common Gateway Interface (CGI) specification is used for creating executable programs that run on a Web server. CGI defines the communication link between a Web server and Web applications. It gives a network or Internet resource access to specific programs. For example, when users submit an HTML form on a Web site, CGI is used to pass this information to a remote application for processing, and retrieve the results from the application. It then returns these results to the user by means of an HTML page. Answer A is incorrect. CGI programs do not execute on routers.
NEW QUESTION 11
John works as a Network Administrator for Perfect Solutions Inc. The company has a
Linux-based network. John is working as a root user on the Linux operating system. He has recently backed up his entire Linux hard drive into the my_backup.tgz file. The size of the my_backup.tgz file is 800MB. Now, he wants to break this file into two files in which the size of the first file named my_backup.tgz.aa should be 600MB and that of the second file named my_backup.tgz.ab should be 200MB. Which of the following commands will John use to accomplish his task?
- A. split --verbose -b 200m my_backup.tgz my_backup.tgz
- B. split --verbose -b 200m my_backup.tgz my_backup.tgz
- C. split --verbose -b 600m my_backup.tgz my_backup.tgz
- D. split --verbose -b 600m my_backup.tgz my_backup.tgz
Answer: D
Explanation:
According to the scenario, John wants to break the my_backup.tgz file into two files in which the size of the first file named my_backup.tgz.aa should be 600MB and that of the second file named my_backup.tgz.ab should be 200MB. Hence, he will use the the split --verbose -b 600 my_backup.tgz my_backup.tgz. command, which will automatically break the first file into 600MB named my_backup.tgz.aa, and the rest of the data (200MB) will be assigned to the second file named my_backup.tgz.ab. The reason behind the names is that the split command provides suffixes as 'aa', 'ab', 'ac', ..., 'az', 'ba', 'bb', etc. in the broken file names by default. Hence, both conditions, the file names as well as the file sizes, match with this command. Note: If the size of the tar file my_backup.tgz is 1300MB, the command split --verbose -b 600 my_backup.tgz my_backup.tgz. breaks the my_backup.tgz file into three files, i.e., my_backup.tgz.aa of size 600MB, my_backup.tgz.ab of size 600MB, and my_backup.tgz.ac of size 100MB.
NEW QUESTION 12
You are concerned about war driving bringing hackers attention to your wireless network. What is the most basic step you can take to mitigate this risk?
- A. Implement WPA
- B. Implement WEP
- C. Don't broadcast SSID
- D. Implement MAC filtering
Answer: C
Explanation:
By not broadcasting your SSID some simple war driving tools won't detect your network. However you should be aware that there are tools that will still detect networks that are not broadcasting their SSID across your network. Answer D is incorrect. While MAC filtering may help prevent a hacker from accessing your network, it won't keep him or her from finding your network.
NEW QUESTION 13
One of the sales people in your company complains that sometimes he gets a lot of unsolicited messages on his PD A. After asking a few questions, you determine that the issue only occurs in crowded areas like airports. What is the most likely problem?
- A. Spam
- B. Blue snarfing
- C. A virus
- D. Blue jacking
Answer: D
Explanation:
Blue jacking is the process of using another bluetooth device that is within range (about 30' or less) and sending unsolicited messages to the target. Answer B is incorrect. Blue snarfing is a process whereby the attacker actually takes control of the phone. Perhaps copying data or even making calls. Answer C is incorrect. A virus would not cause unsolicited messages. Adware might, but not a virus. Answer A is incorrect. Spam would not be limited to when the person was in a crowded area.
NEW QUESTION 14
Which of the following statements about Secure Sockets Layer (SSL) are true? (Choose two)
- A. It provides connectivity between Web browser and Web server.
- B. It provides mail transfer service.
- C. It provides communication privacy, authentication, and message integrity.
- D. It uses a combination of public key and symmetric encryption for security of data.
Answer: CD
Explanation:
Secure Sockets Layer (SSL) is a protocol used to transmit private documents via the Internet. SSL uses a combination of public key and symmetric encryption to provide communication privacy, authentication, and message integrity. Using the SSL protocol, clients and servers can communicate in a way that prevents eavesdropping and tampering of data on the Internet. Many Web sites use the SSL protocol to obtain confidential user information, such as credit card numbers. By convention, URLs that require an SSL connection start with https: instead of http:. By default, SSL uses port 443 for secured communication. For a SSL connection between a Web browser and Web server, you must enter https, for example, "https://www.vzen.com", instead of http as the protocol type in the URL. This will instruct the Web browser to use a different port for communication. SSL uses TCP port 443 for communication.
NEW QUESTION 15
Which of the following statements is true about COLSPAN attribute?
- A. COLSPAN is used to create columns in a table.
- B. COLSPAN is used to divide one column into many columns.
- C. COLSPAN is used to span one column across many rows.
- D. COLSPAN is used to span one column across many columns.
Answer: D
Explanation:
COLSPAN attribute is used to span one column across many columns. COLSPAN is an attribute of <TD> and <TH> tags that allow a single column in a table to take space that is occupied by several columns. If the specified COLSPAN value is greater than the number of columns in the table, then a new column is created at the end of the row. Reference: MSDN, Contents: COLSPAN
NEW QUESTION 16
You are the Security Consultant and have been hired to check security for a client's network. Your client has stated that he has many concerns but the most critical is the security of Web applications on their Web server. What should be your highest priority then in checking his network?
- A. Setting up a honey pot
- B. Vulnerability scanning
- C. Setting up IDS
- D. Port scanning
Answer: B
Explanation:
According to the question, you highest priority is to scan the Web applications for vulnerability.
NEW QUESTION 17
You have to move the whole directory /foo to /bar. Which of the following commands will you use to accomplish the task?
- A. mv /bar /foo
- B. mv -R /foo /bar
- C. mv /foo /bar
- D. mv -r /bar /foo
Answer: C
Explanation:
You will use the mv /foo /bar command to move the whole directory /foo to /bar. The mv command moves files and directories from one directory to another or renames a file or directory. mv must always be given at least two arguments. The first argument is given as a source file. The second argument is interpreted as the destination. If destination is an existing directory, the source file is moved to that directory with the same name as the source. If the destination is any other directory, the source file is moved and/or renamed to that destination name. Syntax : mv [options] source destination Some important options used with mv command are as follows: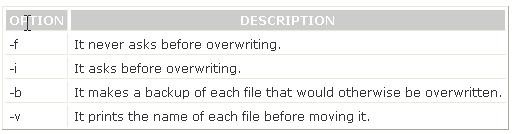
Answer A is incorrect. The mv /bar /foo command will move the whole /bar directory to the /foo directory. Answer B, D are incorrect. These are not valid Linux commands.
NEW QUESTION 18
......
100% Valid and Newest Version GSNA Questions & Answers shared by Dumpscollection.com, Get Full Dumps HERE: https://www.dumpscollection.net/dumps/GSNA/ (New 368 Q&As)