2026 New GSNA Exam Dumps with PDF and VCE Free: https://www.2passeasy.com/dumps/GSNA/
Master the GSNA GIAC Systems and Network Auditor content and be ready for exam day success quickly with this Testking GSNA exam guide. We guarantee it!We make it a reality and give you real GSNA questions in our GIAC GSNA braindumps.Latest 100% VALID GIAC GSNA Exam Questions Dumps at below page. You can use our GIAC GSNA braindumps and pass your exam.
Free demo questions for GIAC GSNA Exam Dumps Below:
NEW QUESTION 1
You are tasked with creating an ACL to apply to Fa0/0 based on the following requirements: The ACL must be protocol specific. All traffic from host 10.10.45.2 and subnet 10.10.1.32/27 must be denied access through the router. Telnet and SSH must be denied for ALL hosts except the management host with the IP address of 10.10.0.100. This management host must not only have Telnet and SSH access, but access to any port in the TCP and UDP suite to any destination. HTTP, HTTPS, and DNS requests must be allowed for all hosts on subnets 10.10.2.0/24 and 10.10.3.0/24 to any destination. All remaining traffic must be denied. Cisco IOS applies an implied deny all at the end of an ACL. However, you must provide this configuration manually so that engineers can see hit counts on the deny all traffic when running the show ip access-lists command. Which of the following sets of commands will you choose to complete the configuration on Router A?
- A. RouterA(config)#access-list 110 deny ip host 10.10.45.2 any RouterA(config)#access-list 110 deny ip 10.10.1.32 0.0.0.31 any RouterA(config)#access-list 110 permit tcp host 10.10.0.100 any RouterA(config)#access-list 110 permit udp host 10.10.0.100 any RouterA(config)#access-list 110 permit tcp 10.10.2.0 0.0.1.255 any eq 80RouterA(config)#access-list 110 permit tcp 10.10.2.0 0.0.1.255 any eq 443RouterA(config)#access-list 110 permit udp 10.10.2.0 0.0.1.255 any eq 53 RouterA(config)#access-list 110 deny ip any any RouterA(config)#interface fa0/0RouterA(config-if)#ip access-group 110 out
- B. RouterA(config)#access-list 110 deny ip host 10.10.45.2 any RouterA(config)#access-list 110 deny ip 10.10.1.32 0.0.0.31 any RouterA(config)#access-list 110 permit ip host 10.10.0.100 any RouterA(config)#access-list 110 permit tcp 10.10.2.0 0.0.1.255 any eq 80RouterA(config)#access-list 110 permit tcp 10.10.2.0 0.0.1.255 any eq 443RouterA(config)#access-list 110 permit udp 10.10.2.0 0.0.1.255 any eq 53 RouterA(config)#access-list 110 deny ip any any RouterA(config)#interface fa0/0 RouterA(config-if)#ip access-group 110 in
- C. RouterA(config)#access-list 110 deny ip host 10.10.45.2 any RouterA(config)#access-list 110 deny ip 10.10.1.32 0.0.0.31 any RouterA(config)#access-list 110 permit tcp host 10.10.0.100 any RouterA(config)#access-list 110 permit udp host 10.10.0.100 any RouterA(config)#access-list 110 permit tcp 10.10.2.0 0.0.1.255 any eq 80RouterA(config)#access-list 110 permit tcp 10.10.2.0 0.0.1.255 any eq 443RouterA(config)#access-list 110 permit udp 10.10.2.0 0.0.1.255 any eq 53 RouterA(config)#access-list 110 deny ip any any RouterA(config)#interface fa0/0 RouterA(config-if)#ip access-group 110 in
- D. RouterA(config)#access-list 99 deny ip host 10.10.45.2 any RouterA(config)#access-list 99 deny ip 10.10.1.32 0.0.0.31 any RouterA(config)#access-list 99 permit tcp host 10.10.0.100 any RouterA(config)#access-list 99 permit udp host 10.10.0.100 any RouterA(config)#access-list 99 permit tcp 10.10.2.0 0.0.1.255 any eq 80RouterA(config)#access-list 99 permit tcp 10.10.2.0 0.0.1.255 any eq 443RouterA(config)#access-list 99 permit udp 10.10.2.0 0.0.1.255 any eq 53 RouterA(config)#access-list 99 deny ip any any RouterA(config)#interface fa0/0 RouterA(config-if)#ip access-group 99 in
Answer: C
Explanation:
This ACL is an extended ACL. It meets the traffic requirements and is applied to Fa0/0 in the appropriate direction of in, which matches traffic going into the interface. In addition, this ACL meets the needs for subnets 10.10.2.0/24 and 10.10.3.0/24 by applying the subnet and wildcard mask of 10.10.2.0 0.0.1.255 for the lines that apply http, https, and dns. These subnets are covered by the wildcard mask 0.0.1.255. This wildcard mask is applied to a range of hosts from 10.10.2.0 through 10.10.3.255 which covers both of the subnets required. This is handy since both subnets are next to each other in their network numbers. Note: If the network numbers were not next to each other, for example 10.10.2.0/24 and 10.10.20.0/24, then the wildcard mask of 0.0.1.255 would be incorrect. A wildcard mask of 0.0.0.255 would be required. The configuration of the ACL would then be applied using the following commands: <!-- Only the relevant commands are displayed --> RouterA(config)#access-list 110 permit tcp 10.10.2.0 0.0.0.255 any eq 80
RouterA(config)#access-list 110 permit tcp 10.10.2.0 0.0.0.255 any eq 443
RouterA(config)#access-list 110 permit udp 10.10.2.0 0.0.0.255 any eq 53
RouterA(config)#access-list 110 permit tcp 10.10.20.0 0.0.0.255 any eq 80
RouterA(config)#access-list 110 permit tcp 10.10.20.0 0.0.0.255 any eq 443
RouterA(config)#access-list 110 permit udp 10.10.20.0 0.0.0.255 any eq 53
NEW QUESTION 2
You work as a Network Administrator for NTY Inc. The company has a secure wireless network. While auditing the network for maintaining security, you find an unknown node. You want to locate that node. Which tool will you use to pinpoint the actual physical location of the node?
- A. Kismet
- B. Ekahau
- C. WEPCrack
- D. AirSnort
Answer: B
Explanation:
Ekahau is an easy-to-use powerful and comprehensive tool for network site surveys and optimization. It is an auditing tool that can be used to pinpoint the actual physical location of wireless devices in the network. This tool can be used to make a map of the office and then perform the survey of the office. In the process, if one finds an unknown node, ekahau can be used to locate that node. Answer D is incorrect. AirSnort is a Linux-based WLAN WEP cracking tool that recovers encryption keys. AirSnort operates by passively monitoring transmissions. It uses Ciphertext Only Attack and captures approximately 5 to 10 million packets to decrypt the WEP keys.
Answer A is incorrect. Kismet is a Linux-based 802.11 wireless network sniffer and intrusion detection system. It can work with any wireless card that supports raw monitoring (rfmon) mode. Kismet can sniff 802.11b, 802.11a, 802.11g, and 802.11n traffic. Kismet can be used for the following tasks: To identify networks by passively collecting packets To detect standard named networks To detect masked networks To collect the presence of non-beaconing networks via data traffic Answer C is incorrect. WEPcrack is a wireless network cracking tool that exploits the vulnerabilities in the RC4 Algorithm, which comprises the WEP security parameters. It mainly consists of three tools, which are as follows: WeakIVGen: It allows a user to emulate the encryption output of 802.11 networks to weaken the secret key used to encrypt the network traffic. Prism-getIV: It analyzes packets of information until ultimately matching patterns to the one known to decrypt the secret key. WEPcrack: It pulls the all beneficial data of WeakIVGen and Prism-getIV to decipher the network encryption.
NEW QUESTION 3
You work as an Exchange Administrator for XYZ CORP. The network design of the company is given below: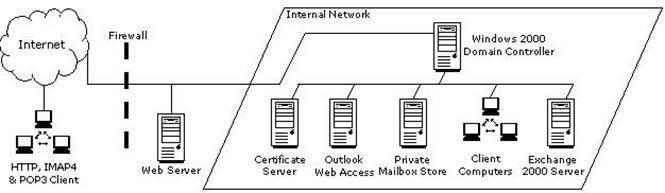
Employees are required to use Microsoft Outlook Web Access to access their emails remotely. You are required to accomplish the following goals: Ensure fault tolerance amongst the servers. Ensure the highest level of security and encryption for the Outlook Web Access clients. What will you do to accomplish these goals?
- A. Install one front-end Exchange 2000 server and continue to run Microsoft Outlook Web Access on the existing serve
- B. Place the new server on the perimeter networ
- C. Configure unique URLs for each serve
- D. Configure Certificate Service
- E. Create a rule on the firewall to direct port 443 to the servers.
- F. Install two front-end Exchange 2000 server
- G. Place the new servers on the internal network and configure load balancing between the
- H. Configure Certificate Service
- I. Create a rule on the firewall to redirect port 443 to the servers.
- J. Install two front-end Exchange 2000 server
- K. Place the new servers on the perimeter network and configure load balancing between the
- L. Configure Certificate Service
- M. Create a rule on the firewall to redirect port 443 to the servers.
- N. Install two Exchange 2000 server
- O. Place the new servers on the perimeter networ
- P. Configure unique URLs for each serve
- Q. Configure Certificate Service
- R. Create a rule on the firewall to direct port 443 to the servers.
Answer: C
Explanation:
To ensure fault tolerance among the servers and to get the highest possible level of security and encryption for OWA clients, you must install two front-end Exchange 2000 servers. Place the new servers on the perimeter network and configure load balancing between them. To enhance security, you should also configure Certificate Services and create a rule on the firewall to redirect port 443 to the servers. The most secure firewall configuration is placing a firewall on either side of the front-end servers. This isolates the front-end servers in a perimeter network, commonly referred to as a demilitarized zone (DMZ). It is always better to configure more than one front-end server to get fault tolerance.
NEW QUESTION 4
Which of the following commands can be used to intercept and log the Linux kernel messages?
- A. syslogd
- B. klogd
- C. sysklogd
- D. syslog-ng
Answer: BC
Explanation:
The klogd and sysklogd commands can be used to intercept and log the Linux kernel messages.
NEW QUESTION 5
You work as a Network Administrator for Tech Perfect Inc. The company has a Windows Active Directory-based single domain single forest network. The functional level of the
forest is Windows Server 2003. The company has recently provided laptops to its sales team members. You have configured access points in the network to enable a wireless network. The company's security policy states that all users using laptops must use smart cards for authentication. Which of the following authentication techniques will you use to implement the security policy of the company?
- A. IEEE 802.1X using EAP-TLS
- B. IEEE 802.1X using PEAP-MS-CHAP
- C. Pre-shared key
- D. Open system
Answer: A
Explanation:
In order to ensure that the laptop users use smart cards for authentication, you will have to configure IEEE 802.1X authentication using the EAP-TLS protocol on the network.
NEW QUESTION 6
Which of the following is the best way to authenticate users on the intranet?
- A. By using Forms authentication.
- B. By using Basic authentication.
- C. By using clear text.
- D. By using NT authentication.
Answer: D
Explanation:
The best way to authenticate users on the intranet is by using NT authentication. Windows NT authentication works where the client and server computers are located in the same or trusted domains. Using NT authentication with an anonymous logon account is the best way to authenticate users on intranet because passwords are not transmitted over the network. User credentials are supplied automatically, if the user is logged on to a Windows machine. Answer B is incorrect. Basic authentication is used to authenticate users on the Internet. It is used by most of the browsers for authentication and connection. When using Basic authentication, the browser prompts the user for a username and password. This information is then transmitted across the Hypertext Transfer Protocol (HTTP). Answer A is incorrect. Forms authentication is used in an ASP environment to issue appropriate Membership server related cookies, to a user. Answer C is incorrect. Clear text is not an authentication method.
NEW QUESTION 7
Which of the following statements is NOT true about FAT16 file system?
- A. FAT16 file system works well with large disks because the cluster size increases as thedisk partition size increases.
- B. FAT16 file system supports file-level compression.
- C. FAT16 does not support file-level security.
- D. FAT16 file system supports Linux operating system.
Answer: AB
Explanation:
FAT16 file system was developed for disks larger than 16MB. It uses 16-bit allocation table entries. FAT16 file system supports all Microsoft operating systems. It also supports OS/2 and Linux. Answer C, D are incorrect. All these statements are true about FAT16 file system.
NEW QUESTION 8
Which of the following is the default port for Hypertext Transfer Protocol (HTTP)?
- A. 20
- B. 443
- C. 80
- D. 21
Answer: C
Explanation:
Hypertext Transfer Protocol (HTTP) is a client/server TCP/IP protocol used on the World Wide Web (WWW) to display Hypertext Markup Language (HTML) pages. HTTP defines how messages are formatted and transmitted, and what actions Web servers and browsers should take in response to various commands. For example, when a client application or browser sends a request to the server using HTTP commands, the server responds with a message containing the protocol version, success or failure code, server information, and body content, depending on the request. HTTP uses TCP port 80 as the default port. Answer B is incorrect. Port 443 is the default port for Hypertext Transfer Protocol Secure (HTTPS) and Secure Socket Layer (SSL). Answer A, D are incorrect. By default, FTP server uses TCP port 20 for data transfer and TCP port 21 for session control.
NEW QUESTION 9
What is the extension of a Cascading Style Sheet?
- A. .hts
- B. .cs
- C. .js
- D. .css
Answer: D
Explanation:
A Cascading Style Sheet (CSS) is a separate text file that keeps track of design and formatting information, such as colors, fonts, font sizes, and margins, used in Web pages. CSS is used to provide Web site authors greater control on the appearance and presentation of their Web pages. It has codes that are interpreteA, Dpplied by the browser on to the Web pages and their elements. CSS files have .css extension. There are three types of Cascading Style Sheets: External Style Sheet Embedded Style Sheet Inline Style Sheet
NEW QUESTION 10
You work as a Network Administrator for InfraTech Inc. You have been assigned the task of designing the firewall policy for the company. Which of the following statements can be considered acceptable in the 'contracted worker statement' portion of the firewall policy?
- A. No contractors shall have access to the authorized resources.
- B. No contractors shall be permitted to scan the network.
- C. No contractors shall have access to the unauthorized resources.
- D. No contractors can access FTP unless specifically granted permissions to use it.
Answer: BCD
Explanation:
There are different portions that can be included in the firewall policy. These portions include the acceptable use statement, the network connection statement, the contracted worker statement, and the firewall administrator statement. The contracted worker statement portion of the policy is related to the contracted or the temporary workers. It states the rights and permissions for these workers. Some of the items hat can be included in this portion are as follows: No contractors can use FTP unless specifically granted to use it. No contractors shall have access to TELNET unless specifically granted to use it. No contractors shall have access to unauthorized resources. No contractors shall have access to scan the network. Answer A is incorrect. Only authorized resources should be accessed by the contractors.
NEW QUESTION 11
Which of the following records is the first entry in a DNS database file?
- A. CNAME
- B. SOA
- C. SRV
- D. MX
Answer: B
Explanation:
Start of Authority (SOA) record is the first record in any DNS database file. The SOA resource record includes the following fields: owner, TTL, class, type, authoritative server, refresh, minimum TTL, etc. Answer A is incorrect. Canonical Name (CNAME) is a resource record that creates an alias for the specified Fully Qualified Domain Name (FQDN). It hides the implementation details of a network from the clients that are connected to the network. Answer D is incorrect. MX is a mail exchange resource record in the database file of a DNS server. It specifies a mail exchange server for a DNS domain name. Answer C is incorrect. SRV resource record is a DNS record that enables users to specify the location of servers for a specific service, protocol, and DNS domain. For example, if there are two servers in a domain, creating SRV records specifies which hosts serve as Web servers, and resolvers can then retrieve all the SRV resource records for the Web servers.
NEW QUESTION 12
Sarah works as a Web Developer for XYZ CORP. She develops a Web site for the company. She uses tables in the Web site. Sarah embeds three tables within a table. What is the technique of embedding tables within a table known as?
- A. Nesting tables
- B. Stacking tables
- C. CSS tables
- D. Horned tables
Answer: A
Explanation:
In general, nesting means embedding a construct inside another. Nesting tables is a technique in which one or more tables are embedded within a table. Answer B, C, D are incorrect. There are no techniques such as stacking tables, horned tables, or CSS tables.
NEW QUESTION 13
Which of the following tools uses Internet Control Message Protocol (ICMP)?
- A. Port scanner
- B. Brutus
- C. Fragroute
- D. Ping scanner
Answer: D
Explanation:
A ping scanner is a tool that sends ICMP ECHO requests across a network and rapidly makes a list of responding nodes. Internet Control Message Protocol (ICMP) is an integral part of IP. It is used to report an error in datagram processing. The Internet Protocol (IP) is used for host-to-host datagram service in a network. The network is configured with connecting devices called gateways. When an error occurs in datagram processing, gateways or destination hosts report the error to the source hosts through the
ICMP protocol. The ICMP messages are sent in various situations, such as when a datagram cannot reach its destination, when the gateway cannot direct the host to send traffic on a shorter route, when the gateway does not have the buffering capacity, etc. Answer A, B, C are incorrect. These tools do not use ICMP to perform their functions.
NEW QUESTION 14
Sarah works as a Web Developer for XYZ CORP. She is creating a Web site for her company. Sarah wants greater control over the appearance and presentation of Web pages. She wants the ability to precisely specify the display attributes and the appearance of elements on the Web pages. How will she accomplish this?
- A. Use the Database Design wizard.
- B. Make two templates, one for the index page and the other for all other pages.
- C. Use Cascading Style Sheet (CSS).
- D. Make a template and use it to create each Web page.
Answer: C
Explanation:
Sarah should use the Cascading Style Sheet (CSS) while creating Web pages. This will give her greater control over the appearance and presentation of the Web pages and will also enable her to precisely specify the display attributes and the appearance of elements on the Web pages.
NEW QUESTION 15
Which of the following features of a switch helps to protect network from MAC flood and MAC spoofing?
- A. Multi-Authentication
- B. Port security
- C. MAC Authentication Bypass
- D. Quality of Service (QoS)
Answer: B
Explanation:
If a switch has the ability to enable port security, this will help to protect network from both the MAC Flood and MAC Spoofing attacks. Answer D is incorrect. Quality of Service (QoS) feature is useful for prioritizing VOIP traffic. Switches are offering the ability to assign a device a Quality of Service (QoS) value or a rate limiting value based on the RADIUS response. Answer A is incorrect. Multi-Authentication feature is used to allow multiple devices to use a single port. Answer C is incorrect. MAC Authentication Bypass feature is used to allow the RADIUS server to specify the default VLAN/ACL for every device that doesn't authenticate by 802.1X.
NEW QUESTION 16
John used to work as a Network Administrator for We-are-secure Inc. Now he has resigned from the company for personal reasons. He wants to send out some secret information of the company. To do so, he takes an image file and simply uses a tool image hide and embeds the secret file within an image file of the famous actress, Jennifer Lopez, and sends it to his Yahoo mail id. Since he is using the image file to send the data, the mail server of his company is unable to filter this mail. Which of the following techniques is he performing to accomplish his task?
- A. Web ripping
- B. Steganography
- C. Email spoofing
- D. Social engineering
Answer: B
Explanation:
According to the scenario, John is performing the Steganography technique for sending malicious data. Steganography is an art and science of hiding information by embedding harmful messages within other seemingly harmless messages. It works by replacing bits of unused data, such as graphics, sound, text, and HTML, with bits of invisible information in regular computer files. This hidden information can be in the form of plain text, cipher text, or even in the form of images. Answer A is incorrect. Web ripping is
a technique in which the attacker copies the whole structure of a Web site to the local disk and obtains all files of the Web site. Web ripping helps an attacker to trace the loopholes of the Web site. Answer D is incorrect. Social engineering is the art of convincing people and making them disclose useful information such as account names and passwords. This information is further exploited by hackers to gain access to a user's computer or network. This method involves mental ability of the people to trick someone rather than their technical skills. A user should always distrust people who ask him for his account name or password, computer name, IP address, employee ID, or other information that can be misused. Answer C is incorrect. John is not performing email spoofing. In email spoofing, an attacker sends emails after writing another person's mailing address in the from field of the email id.
NEW QUESTION 17
Which of the following standards is used in wireless local area networks (WLANs)?
- A. IEEE 802.4
- B. IEEE 802.3
- C. IEEE 802.5
- D. IEEE 802.11b
Answer: D
Explanation:
IEEE 802.11b is an extension of the 802.11 standard. It is used in wireless local area
networks (WLANs) and provides 11 Mbps transmission speeds in the bandwidth of 2.4 GHz. Answer B is incorrect. IEEE 802.3 is a standard for wired networks , which defines the media access control (MAC) layer for bus networks that use CSMA/CD. Answer A is incorrect. IEEE 802.4 is a standard for wired networks , which defines the MAC layer for bus networks that use a token- passing mechanism. Answer C is incorrect. IEEE 802.5 is a standard for wired networks, which defines the MAC layer for token-ring networks.
NEW QUESTION 18
......
Recommend!! Get the Full GSNA dumps in VCE and PDF From Certleader, Welcome to Download: https://www.certleader.com/GSNA-dumps.html (New 368 Q&As Version)